What is a VPN?
Wondering what VPNs are? Or how they work? I'll dig in to the VPN meaning – without the jargon.

If you like to peruse YouTube, or are a fan of podcasts, chances are you've heard of a VPN.
But what actually is a VPN? How does it work? Do you really need to use one even if you just use the internet to scroll through social media and binge-watch Netflix?
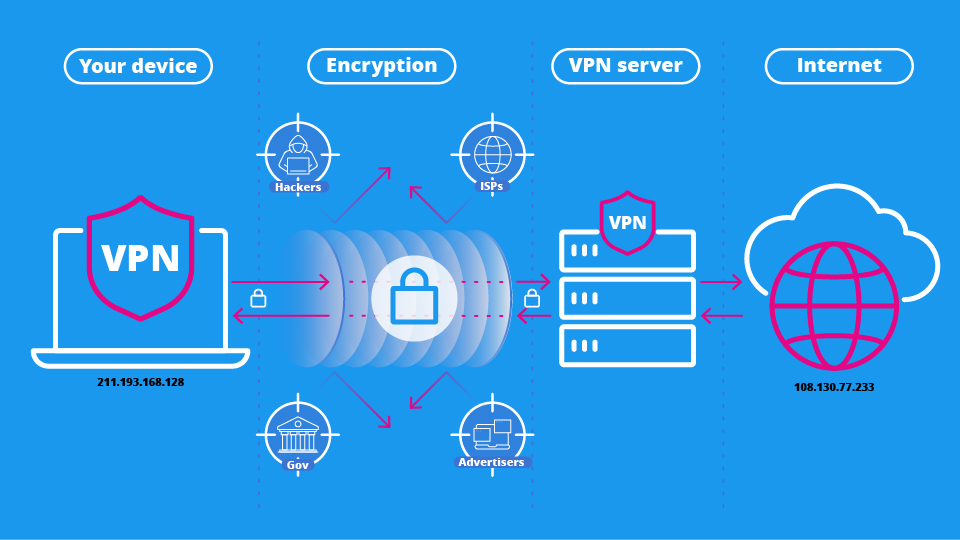
When you use a VPN (or virtual private network), it routes your internet traffic through a secure tunnel and encrypts it. This makes it so no one can see what sites you're visiting, even if they get hold of your internet traffic.
Your connection goes through a server that is either owned or controlled by the VPN. If you pick a server in a different location, you can appear to be connecting to the internet from this location, which allows you to unblock region-specific content quickly and easily.
Unfortunately, if you do a quick Google, a lot of the answers to these questions tend to be laden with jargon, assuming that you're familiar with all sorts of different kinds of technology.
This can lead to the belief that VPNs are only for experts, which couldn't be further from the truth. Nowadays, most of the best VPNs are made for all consumers, no matter their level of technical literacy.
If you're looking for more info on all things VPN, simply read on for all this and more – I'll even explain how using a VPN can help level up your online experience.

I've been in charge of Tom's Guide's VPN articles since 2020, and in that time I've helped test and review over 100 VPN providers for both Tom's Guide and TechRadar. I strongly believe that privacy, price, and ease of use all go hand in hand to make the very best VPN.
I've covered cybersecurity and tech in TechRadar, T3, and What Hi-Fi?, and you'll also find my work in titles from Watkins Publishing, and even the halls of the Metropolitan Museum of Art.
Top 3 VPNs in 2025
1. NordVPN: our best VPN overall
If any VPN has become a household name over the last few years – it's NordVPN. It's an all-in-one security suite that can block ads, stop malware, and protect your privacy.
It's a powerful streaming unblocker and our #1 pick for Netflix. It boasts speeds of 900 Mbps and has a load of great extra features.
The two-year plan starts at $3.09 per month ($83.43 up front pre-tax) for 27 months protection. There's also a 30-day money-back guarantee so you can try NordVPN for yourself.
2. Surfshark: the best cheap VPN
If you're more budget-conscious, Surfshark is a great option. This VPN gives you premium features like super fast connections and excellent privacy, without a huge price tag.
Not only does Surfshark boasts servers in 100 countries on top of great unblocking capabilities and privacy features, it offers all this for only $1.99 a month ($53.73 up front pre-tax). There's also three months free and a 30-day money-back guarantee.
3. ExpressVPN: best VPN for beginners
ExpressVPN is a great choice for beginners to VPNs thanks to its simple yet effective apps that are available across a range of devices in addition to great unblocking capabilities and top-of-the-range privacy.
The two-year plan is $4.99 per month ($139.72 up front), with three months of extra protection for free and a 30-day money-back guarantee.
What are VPNs for?
It's worth considering which kind of VPN you're interested in before considering the purpose. A business VPN like the one you may use at work (or when working from home) is an essential tool for connecting remote users to a single Intranet and accessing restricted files.
It will have specialized tools to allow teams to work well together like dedicated IPs and a central management system, but you won't want to use it for more recreational reasons.
A consumer VPN – the ones you see advertised in YouTube videos and on TV – are optimized for personal use.
This can be providing you with privacy and security online, allow access to sites that are blocked by your Internet Service Provider (ISP) or government, and unlock international streaming libraries – you'll want one of the best streaming VPNs for this.
When using one, your internet connection is routed a VPN server, rather than your ISP's. Your activity is hidden (which is likely to log any suspicious activity), your IP address will be changed, and so will your apparent location.
In short, a VPN can make you appear to be a totally different person online. That helps to avoid ad trackers, access different content that may be blocked by your ISP, and ensure all your browsing can't be linked back to you.
VPNs can be used on all your devices and across most platforms. We have numerous guides to help you navigate choosing a VPN. These include the best mobile VPN, the best Windows VPN, the best Mac VPN, the most private VPN, plus many more.
What are VPN protocols?
The most secure VPNs use several protocols that encrypt data traffic. This is especially important because data is being transmitted over a public network between two remote locations.
The most popular VPN protocols include:
- Internet Key Exchange (IKEv1 and IKEv2)
- IP Security (IPSec)
- OpenVPN
- WireGuard
Most of the time, you'll use WireGuard, as this is today's gold standard, balancing battle-tested security with the speed you need to stream, game, and browse without hiccups.
In all protocols, both endpoints – your computer, smartphone, or router – and the VPN server, use a "handshake" method of authentication. To successfully initiate this connection, the connecting computer must share a key that matches the required parameters for the receiving location.
Many leading providers have developed their own VPN protocols, designed for improved performance or added security. Examples include NordVPN's NordWhisper, Proton VPN's Stealth, and ExpressVPN's Lightway.
You might also come across the term obfuscation or obfuscating protocols. These disguise the fact you're using a VPN. This is crucial if you face internet censorship and handy for sites that like to block VPNs.
Why do I need a VPN?
Consumer VPNs have a huge amount of advantages. You'll be able to access sites like torrent repositories that may be blocked by your ISP.
If you live in a country with strict VPN or internet laws, you'll be able to sidestep government restrictions.
If you use one of the best Netflix VPNs, you'll be able to watch shows on it that aren't available in your country, and even access country-specific services you pay for like Hulu and HBO Max if you're out of your home country.
What's more, if you take the right precautions alongside using the VPN (for example, browsing in Incognito mode and not entering personal data), you can also avoid linking yourself to any activity you'd prefer to keep totally private.

Are there downsides to using a VPN?
It's well-known that many VPNs do have an impact on performance. That's almost inevitable thanks to the fact that you're essentially making your connection travel further.
However, if you pick one of the fastest VPNs you won't notice a difference. These VPNs are capable of exceeding 950 Mbps. So as long as your internet can handle it, a VPN won't slow you down.
If you choose to try out a free VPN, make sure it's one of the best free VPNs. They're safe and secure, and will protect your data with the same security and privacy as their paid counterparts.
Suspect free VPNs are popular and you'll find a majority of free VPNs are outright dangerous. If you choose to go with a lesser service you may be putting yourself in danger of having your data stolen and leaked.
However, even reputable free VPNs have certain limitations. For example, you may have a data limit, find you can't stream, and can only protect one device at a time.
These free VPNs do the basics well, but we'd always recommend a paid service. Our best cheap VPN guide is a perfect place to start if you're looking for a VPN on a budget, with premium plans available for under $2 per month.
The Tom's Guide team is always putting VPNs to the test – and we'll let you know the good, the bad, and the ugly that we uncover in our results. Visit our VPN testing methodology page for more information about our process.
It's also worth noting that you may be faced with CAPTCHA tests on some sites when using a VPN. This is because a VPN's IP addresses are shared between users, and some sites may detect 'unusual' activity.
In our experience, however, this is fairly unobtrusive and is preferable to the unprotected alternative.
Is a VPN enough?
For many people, a VPN will offer enough functionality to get more out of the web and stay safe online. It'll get access to more streaming content, stop ad trackers collecting your data, and keep you safer by encrypting your traffic on public Wi-Fi.
However, if you're looking for true web privacy, there are a number of other steps you should take to ensure you're staying anonymous.

First, use Incognito or private browsing mode. That means your history will not be saved, and, depending on your settings, cookies will be disabled. Plus, you won't be automatically signed into websites, which is an easy way of linking your fresh IP straight back to you.
Beyond that, using secure browsers such as Brave, Opera, or Vivaldi help prevent tracking and removes you from the clutches of Google. Separate ad-blockers are a good idea and consider some of the best antivirus software.
If you're looking for anonymity rather than privacy, consider the Tor Browser. It's a decentralized volunteer run network, which focuses on anonymity. VPNs can be used with Tor, although they do different things – our Tor vs VPN page details their similarities and differences.
As always, though, you – the user – are the weakest link. If you're not careful about inputting personal information, no matter how well-protected your connection is you can be discovered.
That won't be a huge issue for most, but no matter what precautions you take to secure your connection, you need to match that with your own diligence and common sense.
FAQs
Do I really need a VPN?
Not everyone needs a VPN. But the unfortunate truth is that the internet is full of threats to your digital security.
A VPN's encrypted tunnel keeps your data secure from third-party snoops and hackers, reducing the risk of identity fraud and theft, and can even help banish invasive ads that use your browsing history to create tailored campaigns.
How much does a VPN cost?
VPNs are available at all price ranges – so you're bound to find a service that suits your budget.
Premium providers come with all the bells and whistles, like antivirus features and password managers, though you'll likely have to pay more for the privilege.
You can save money by choosing a service that offers the tools you'll actually use, and make sure to check out our VPN deals page for all of the latest and greatest offers.
How do I set up a VPN?
Don't worry, getting your VPN up and running is quick and easy. All you need to do is:
1. Choose a provider, pick a plan, and download the right app for the device you're using.
2. Log in to the app.
3. Choose a server to join (locations near you will be quicker, but you'll unblock different content in cities overseas) and hit the connect button.
4. Wait a moment, and you're ready to go.
We test and review VPN services in the context of legal recreational uses. For example: 1. Accessing a service from another country (subject to the terms and conditions of that service). 2. Protecting your online security and strengthening your online privacy when abroad. We do not support or condone the illegal or malicious use of VPN services. Consuming pirated content that is paid-for is neither endorsed nor approved by Future Publishing.

Mo has been rigorously testing, reviewing, and analyzing VPN services at Tom’s Guide for more than five years. He heads up the three-person Tom's Guide VPN team, and is passionate about accessibility: he believes that online privacy should be an option that’s available to everyone. NordVPN and ExpressVPN are the products he uses most on a daily basis, but he experiments weekly with all the top services, evaluating their privacy features, connection speeds across various protocols, and server reliability – among other things – so that he can make confident VPN recommendations that are backed by data. To see his latest advice, head over to Tom’s Guide’s best VPN and best free VPN guides.
- George PhillipsStaff Writer
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Club Benefits
Club Benefits













