Proton VPN Stealth protocol: what is it and why should you use it?
An obfuscated VPN protocol to better evade online censorship

Most, if not all, VPNs are concerned with their user's online security and privacy, with some providers taking it further in their quest to provide anonymity.
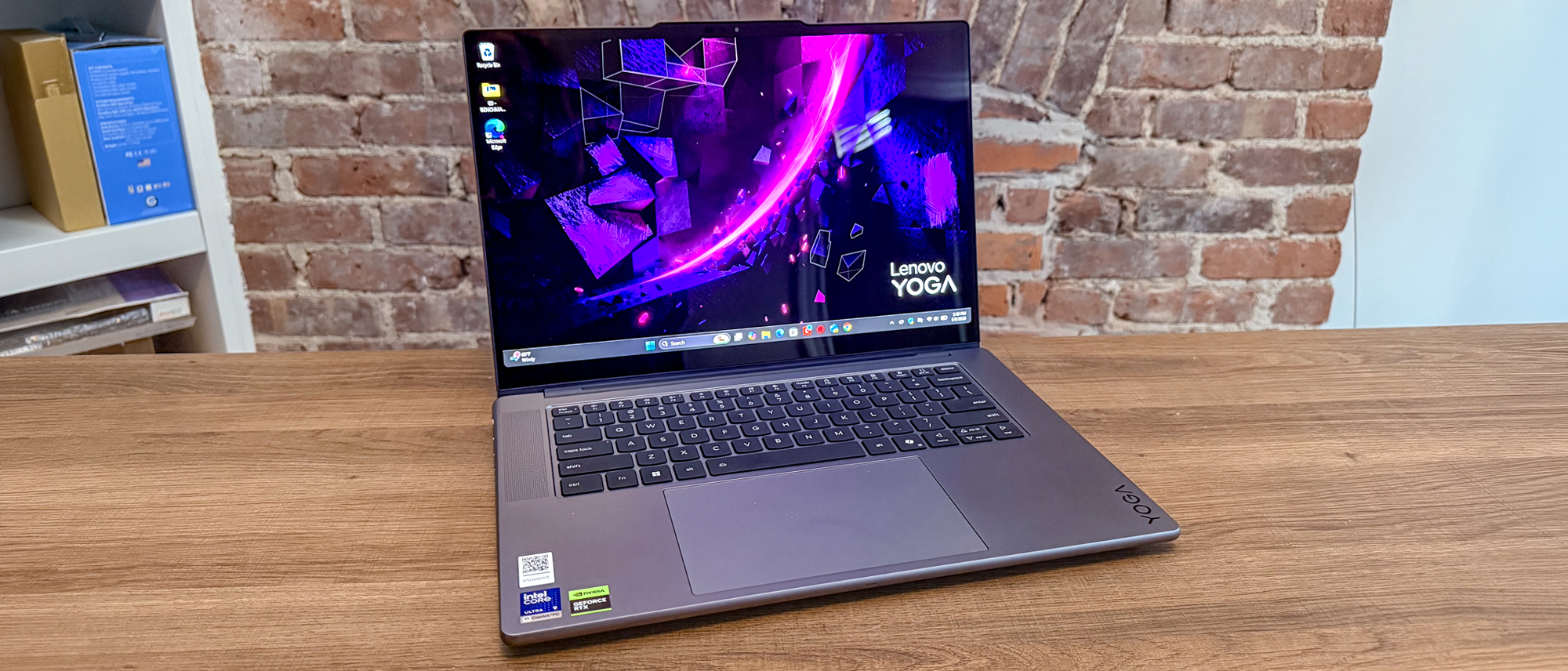
A great example of this comes from one of the best VPN services around, Proton VPN. The Swiss-based provider has continued to promote internet freedom for everyone thanks to its secure protocol, known as stealth.
In Proton's own words, its Stealth protocol is its very own "custom-built anti-censorship protocol" aimed at evading VPN blocks. Let's now look a bit closer at how Proton VPN's Stealth protocol works, and when you should use it.
Proton VPN – Swiss privacy for all
You may know Proton for its other consumer privacy tech products, and its VPN is just as good, if not better, than its other products. Not only is it super secure and have excellent speeds, but its also great for unblocking streaming sites. Prices start at $3.59 per month, and there's also a 30-day money-back guarantee so you can try it out risk-free.
What is Proton VPN Stealth?
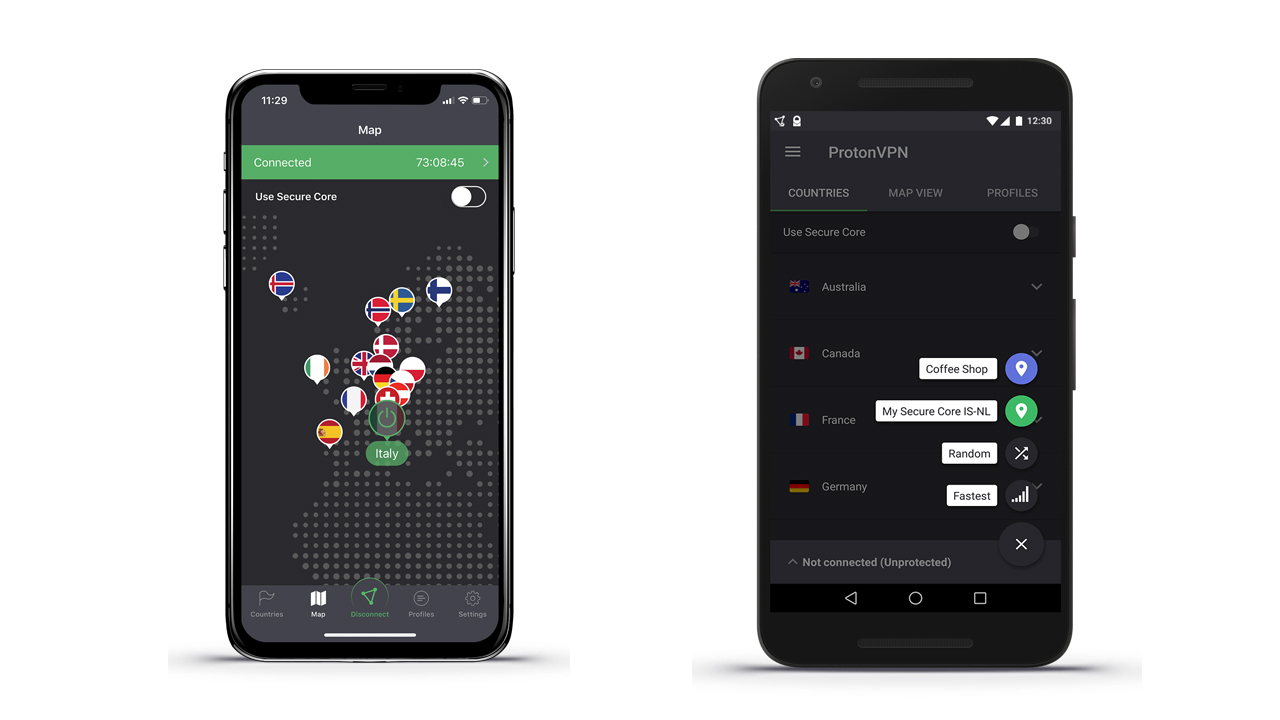
Proton VPN Stealth is the provider's very own obfuscation technology. A feature becoming common across the industry, especially among the most secure VPNs, it's responsible for making your VPN traffic look like a normal connection.
That's necessary as governments and/or other networks (like your workplace or school, for example) might block VPN traffic for security or any other reasons.
While some secure VPN providers might require users to choose an obfuscated server to evade blocks, here, the encryption protocol adds an extra layer of protection. Other providers offering obfuscation include ExpressVPN, NordVPN and Surfshark.
Especially caring about those users living under strict regimes, Proton developed Stealth with the aim to enable users everywhere around the world to evade online censorship at ease.
How does Proton Stealth work?
There are different tactics for successfully obfuscating VPN traffic. It can be done by applying an additional layer of encryption able to mock regular HTTPS traffic, for example. Or, the software might scramble the data to prevent the algorithm from recognizing you're using such security software.
Without going into too much technical detail, Proton Stealth is an open source obfuscation protocol based on WireGuard and TLS. "It is unique to Proton VPN and can be used to connect to all our servers (including our free servers)," a company's spokesperson told us.
Proton's developers also explained that they decided to create their own protocol as projects trying to obfuscate existing ones had failed in the past to deliver a full and effective functionality.
What's more, the provider claims that Stealth establishes its connections in such a unique way able to avoid alerting internet filters.
"We designed our Stealth protocol from the ground up to not have these issues. With Stealth enabled, your Proton VPN connection will be almost completely undetectable," Proton explained.
When should you use Proton Stealth VPN?
We already mentioned how defeating censorship, bypassing VPN bans and promoting internet freedom globally are the main reasons for the introduction of Stealth.
However, even people living in countries where the web isn't restricted can find this option really handy. These include:
- Improving VPN unblocking power: While the best streaming VPNs are great for accessing content, unblocking foreign catalogs is usually against platforms' terms and conditions. For this reason, Netflix and similar companies work hard to detect and block VPN traffic. So, an obfuscated protocol might be of help here.
- Bypassing network restrictions: Both workplace and school networks don't generally allow the use of VPNs for security reasons. This means that you may need to opt to use Stealth if you wish to go private and connect with your security tool.
- Boosting your online security: Connecting to Proton VPN already improves your online privacy. However, an additional layer of encryption is always beneficial in terms of security. This means that using Proton's Stealth protocol can also help better securing your sensitive data against intruders.
What's next for Proton VPN?
Proton VPN has recently made some updates in order to continue providing great privacy and security for users, including:
- More than doubling the number of servers it offers, up to over 8,100
- Increasing its server countries from 70 to 112, with many in Africa.
- Updating its Android app to include split tunneling.
- Completing a new no-logging audit from Securitum.

Chiara is a multimedia journalist committed to covering stories to help promote the rights and denounce the abuses of the digital side of life – wherever cybersecurity, markets, and politics tangle up. She believes an open, uncensored, and private internet is a basic human need and wants to use her knowledge of VPNs to help readers take back control. She writes news, interviews, and analysis on data privacy, online censorship, digital rights, tech policies, and security software, with a special focus on VPNs, for TechRadar, TechRadar Pro, and Tom's Guide. Got a story, tip-off, or something tech-interesting to say? Reach out to chiara.castro@futurenet.com
- Olivia PowellTech Software Commissioning Editor
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Club Benefits
Club Benefits