Kids' GPS Tracking Watch Lets Anyone Stalk Your Kid
The MiSafes Kid's Watcher GPS tracker has almost no security and lets anyone with common hacking tools follow and talk to children.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
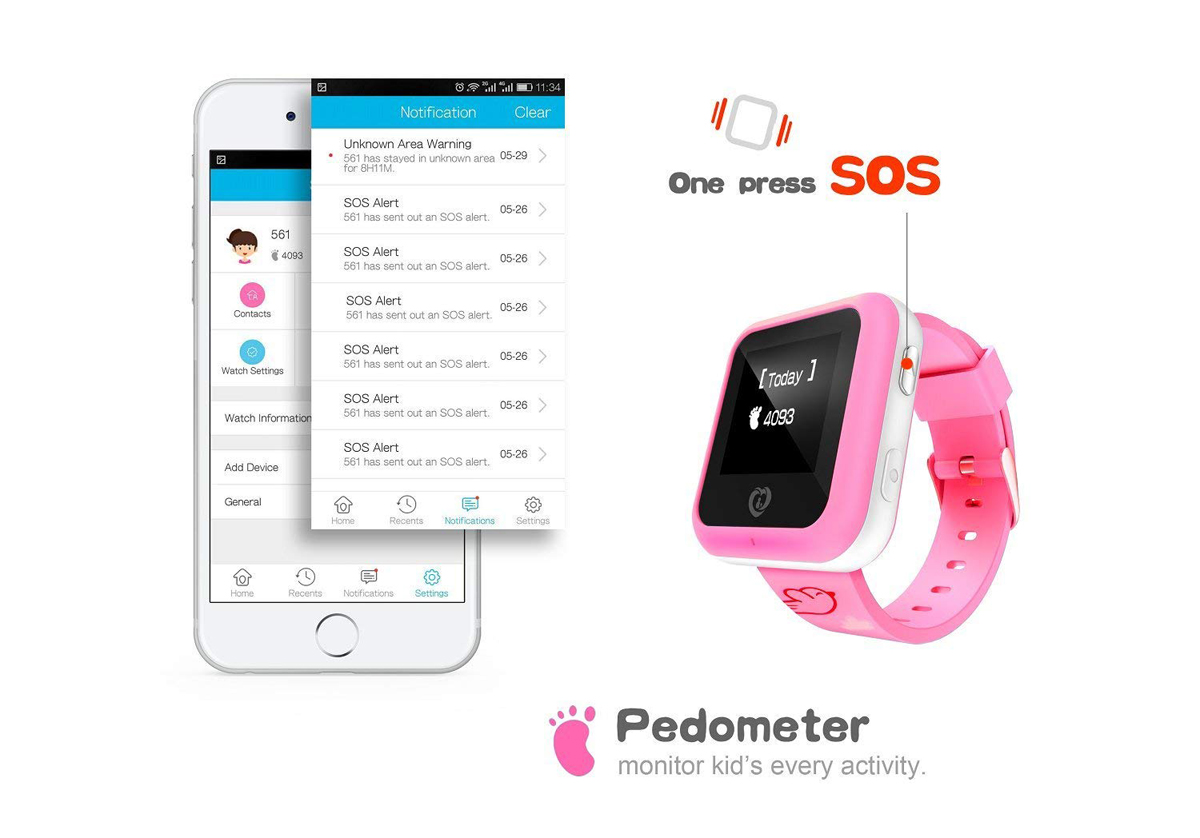
A kid's GPS tracking smartwatch sold in the United Kingdom, and its accompanying smartphone app, have simply abysmal security that would let anyone — including a sexual predator — track, get data on and communicate with children.

That's the upshot of a new report from Pen Test Partners, a British information-security consulting firm, which took a look at the MiSafes Kid's Watcher watch and its iOS app after a friend bought a £9 one for his young son.
"It was bad ... really bad," Pen Test Partners' Alan Monie wrote in a blog posting yesterday (Nov. 15).
Article continues belowThe MiSafes tracking watch is not sold in the United States, but other models that have the same software likely are.
"We believe that in excess of a million smart kids' tracking watches with similar vulnerabilities are being used, possibly in excess of 3 million globally," Monie wrote. "These are sold under numerous brands, but all appear to use remarkably similar APIs [application program interfaces], suggesting a common original device manufacturer or ODM."
MORE: Best GPS Trackers for Kids
Like many kids' tracking watches, the MiSafes Kid's Watcher uses a cellular connection to communicate with the parent's phone. The watch also uses the connection to send data up to a cloud server that processes the child's personal information and current location (as determined by the GPS chip in the watch).
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
The parent can access the information in the cloud server from a dedicated smartphone app or through a web browser. The problem is that none of the data being transmitted between the watch, the cloud and the parent's smartphone or computer is encrypted.
Using a free security-testing tool and a couple of additional MiSafes Kid's Watchers that he bought himself, Monie tapped into the data being sent by the iOS app on his own phone.
He found that by just changing the user ID, he could have accessed tons of data on other people's kids: names, photos, dates of birth, weight, height, parents' phone numbers, the watch's phone number and, perhaps most significantly, current and previous locations.
"It's probably the simplest hack we have ever seen," Monie told the BBC yesterday. "I wish it was more complicated. It isn't."
Monie could also do anything the kids' own parents could do, including calling or texting the kids' watches, or silently calling the watch to secretly listen to what's going on around a child.
"If the watch was left elsewhere in a household, it becomes a remote listening device for anyone on the internet," Monie wrote.
There were a couple of fairly pointless protections in place. The watch kids' would accept calls from or place calls to only whitelisted, approved numbers, but it was easy to get around that by spoofing caller IDs. And the parent's phone number would be easy to get from the wide-open cloud database.
One of Monie's colleagues took a look at the MiSafes parental-app application program interfaces (APIs), which determines how the app interacts with other applications and with cloud servers.
The colleague figured that between 1 million and 3 million GPS-based kids' trackers with the same problems, sold under various brand names, were being used around the world.
While the MiSafes Kid's Watcher isn't sold on the U.S. version of Amazon, several very similar-looking watches, with nearly identical capabilities, are sold there for between $35 and $45.
Both Pen Test Partners and the BBC reached out to MiSafes for comment, but got no answer. The MiSafes.com website is registered to an individual in Shenzhen, the tech-industry hub in southern China.
As for the father and child who'd bought the original MiSafes Kid's Watcher that sparked the research, Pen Test Partners did right by them.
"We felt bad that we'd taken away his son's watch, so we replaced it with one that's had a bit more time spent on security," Monie wrote. "We hope you like your new Apple watch!"
Image credits: MiSafes.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits










