Online Security
Explore Online Security
Latest about Online Security

Score! One of our favorite antivirus apps is up to 58% off right now
By Louis Ramirez published
Sponsored
One of our favorite antivirus apps just got a 58% discount. Here's how to protect your PC and save big on Norton 360 Deluxe.

Online age verification in the USA – a complete timeline
By Olivia Powell last updated
A full timeline of all the age verification laws in the United States, and what they mean for their citizens

Age verification on X – how does it work and do you need to do it?
By George Phillips last updated
X is one of the sites implementing age verification checks. Some users have been unable to comply, while others look to bypass them – here's how it all works.

What is AgeGO, and is it safe to use?
By Olivia Powell last updated
With new age verification laws in the UK, US, and Australia, many people are using AgeGO to verify their age. But is it safe to use?
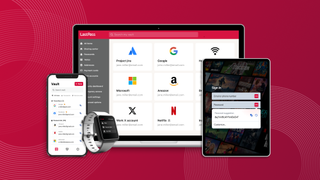
Effortless credential hygiene for every member of your business! LastPass plans are now 30% off
By Paul Hatton published
Get 30% off LastPass and upgrade your password security

1 billion personal records exposed in massive new data leak — full names, addresses, phone numbers and more
By Anthony Spadafora last updated
Security researchers have discovered a database online with troves of personal data from the US, Canada, Australia and dozens of countries around the world.

IPVanish review
By Kristin Hassel last updated
Updated Our VPN experts put IPVanish to the test in this latest review, comparing speed, unblocking, value for money, security, and features. See how IPVanish compares.
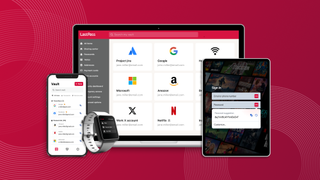
Don't leave your data vulnerable with 30% off LastPass business plans
By Paul Hatton published
Get 30% off LastPass and upgrade your password security

Conduent data breach gets bigger; more than 25 million people across the US are now affected
By Scott Younker published
The Conduent data breach continues to expand as more people have been confirmed to be impacted.

The best password managers in 2026: The foolproof way to secure, store and autofill your passwords
By Anthony Spadafora last updated
The best password managers take the guesswork out of remembering your passwords while helping you generate strong and complex ones for each of your accounts.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
 Club Benefits
Club Benefits










