Bots, Worms, and More - Guarding Smart Devices On Your Network Against Malicious Software

From kitchen appliances to lighting to thermostats to home security systems, the IoT enables an unprecedented level of convenience and control. Unfortunately, it also carries with it considerable risk. Most of the companies now making smart devices do not have any background in cybersecurity.
Historically, they never had to.
They are appliance manufacturers, entertainment companies, and household goods organizations. For them, security was always the sole domain of their IT department. Toss in the fact that IoT is a highly-competitive market, and you have a perfect storm for creating a cybersecurity nightmare.
Already, we've seen a few indications of what this may involve:
- In December, a video started making the rounds of a hacker using a Ring camera to harass an eight-year-old child.
- 2016's Mirai botnet leveraged over 400,000 IoT devices in a distributed denial-of-service attack that took the entire East Coast of the United States offline.
- In 2016, cybersecurity software firm BlackBerry demonstrated how a smart tea kettle could be used as an entry point for an entire network.
- In 2015, researchers demonstrated that a smart fridge could be hacked to expose the owner's Gmail account credentials.
In 2015, researchers demonstrated that a smart fridge could be hacked to expose the owner's Gmail account credentials.
We're not trying to scare you away from using smart devices or having a connected home, mind you. The technology that underpins IoT is wondrous and has the potential to do some very real good for both our personal and our professional lives. It's also very clear that it's going anywhere anytime soon; we live in a world defined by widespread digitization.
What we are saying is that when installing a new IoT device, you need to be smart about it.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
You need to take the necessary precautions to protect your home network, and by association, yourself. Here's how you can do so.
Avoid default credentials and use two-factor authentication

For IoT devices that require a login, change your username and password immediately after installation. You may also want to give the device a name that doesn't immediately identify the make, model, and brand. This will help protect you against attacks that target specific vulnerabilities (such as the Ring exploit we mentioned above).
You can usually find instructions on how to do this in the technical documentation shipped with your device.
Speaking of credentials, you'll want to use a password manager to ensure that you have a unique password for each device. We'd also strongly recommend enabling two-factor authentication wherever possible, via a tool like the Google Authenticator rather than SMS. The more security you can layer atop your network, the better.
Note that the above doesn't just apply to the regular gamut of 'smart' devices - it also applies to stuff like your router and your webcam.
Shore up individual device security

While you're mucking about with the settings of your smart devices, you may want to check and see what security features (and settings) they've shipped with. The most important thing here is to disable Universal Plug and Play (UPnP), as it's easily-exploitable by hackers looking to hijack those devices for use in a botnet or gain access to your network. We'd also strongly advise looking carefully at what sort of data the device and its associated applications collect, and whether or not that data is really necessary for the device to function
Don't slack on updates

If the software associated with your smart devices has a setting for automatic updates, make sure it's toggled to "on." While it's true that manufacturers release software updates to fix minor bugs and improve functionality, these updates also frequently contain critical security fixes and patches. Consider scheduling these updates so they happen when you know you won't be using a device, so you aren't tempted to disable them for convenience's sake.
Protect your wireless network

Where your wireless network is concerned, it should go without saying that you'll want to use the strongest WiFi encryption available to you. It's also extremely important that your WiFi network has a unique SSID and password associated with it. You may want to consider configuring your network so that it doesn't automatically broadcast itself, which can usually be done through your router's configuration portal.
While this may make setting up new devices a bit inconvenient, requiring you to manually enter your details each time, it also makes it far less likely that someone will be able to hijack your network and anything on it.
Finally, if you want to be extra cautious, you can sequester your smart devices on a separate, secondary 'guest' network. You can keep stuff like your smartphone, gaming consoles, and PC on one network, while IoT devices go on the other one. Note that in order to do this, you'll need to invest in a dual-band or tri-band router.
Invest in network security
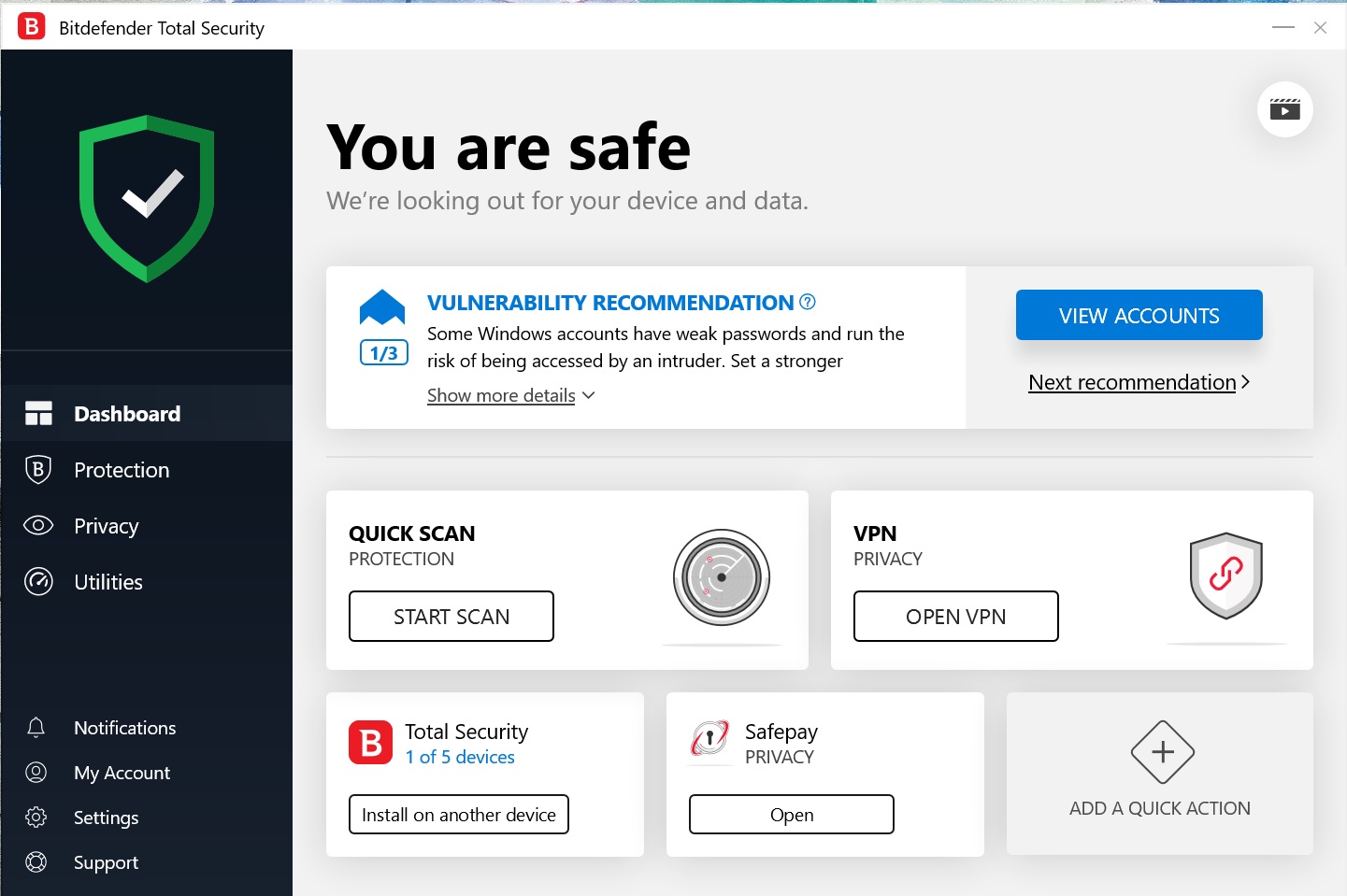
Last but certainly not least, you should understand that even with the above precautions, there's always a chance that a device on your network might be compromised by a hacker or worm. In that regard, the right security software can make all the difference in the world. Enter the award-winning Bitdefender Total Security.
In addition to protecting the devices upon which it's installed, Bitdefender Total Security includes several features designed to safeguard your entire network against advanced threats.
Through the analysis of network-level activity, it's able to block sophisticated exploits, malware, and botnet-related URLs as well as brute-force attacks. It also includes an improved WiFi Security Advisor, ensuring you can get your network up to the highest security standard possible. Finally, a built-in password manager secures your login details and other sensitive data.
If you want a bit of added protection atop Total Security, you may also want to look into Bitdefender BOX, which includes Total Security as well as BOX, a security hub designed specifically with smart homes and IoT devices in mind. Through Bitdefender BOX, you can apply Bitdefender's protection to every endpoint on your network, from smartphones to smart fridges. It helps you remain in control of both your devices and your data, with device-specific security rules, device profiles, and content filtering.
Thus far, we've touched a lot on the technological side of digital safety. But there's a human element to that as well. There are a ton of bad actors on social networks like Facebook, and understanding their tactics and techniques is imperative if you're to keep yourself safe.
That, however, is a topic for next time.
