Daam Android malware can hold your phone hostage — what you need to know
Sneaky new Android malware can also steal your data and hide from antivirus apps
A new Android malware has been spotted in the wild which can bypass antivirus apps, steal loads of sensitive and financial data and even encrypt all of the files on an infected smartphone by deploying ransomware.
According to a new report from the cybersecurity firm CloudSEK, this new Android malware, dubbed “Daam” by its researchers, poses a significant threat to the best Android phones due to its sophisticated capabilities.
The Daam malware appears to be using sideloaded apps to infect Android smartphones and so far, CloudSEK has found it in APK or Android app installation files for the Psiphon, Boulders and Currency Pro apps. While Psiphon is a VPN app, Boulders is a mobile game and Currency Pro, as the name suggests, is a currency converter.
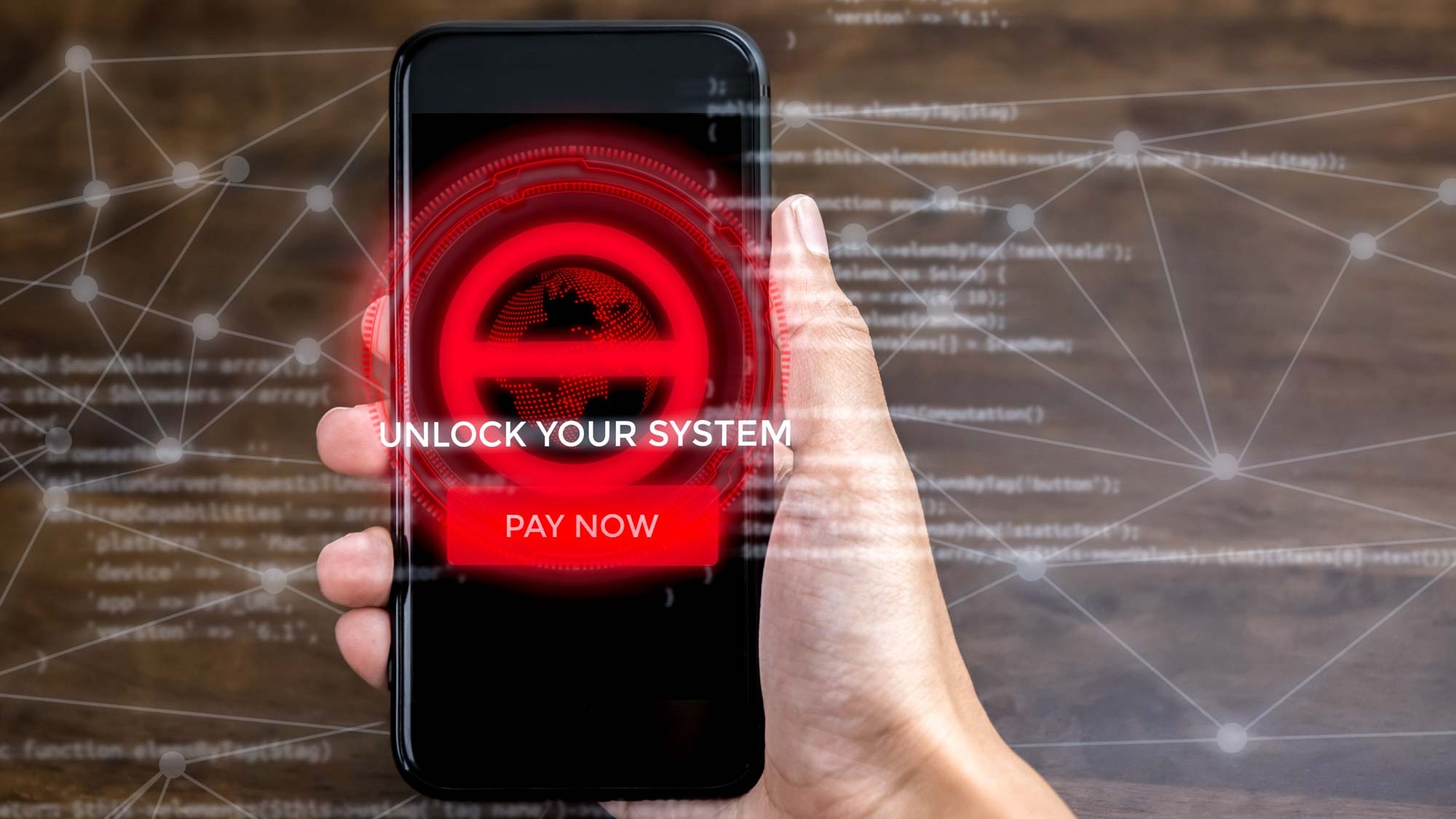
If you’ve sideloaded any of these apps as opposed to installing them through official app stores like the Google Play Store, your Android smartphone could be infected with the Daam malware. Unfortunately though, there may not be an easy fix as the malware can avoid detection by antivirus apps and it may have already locked the files on your smartphone by deploying ransomware.
Encrypting every file on your Android smartphone
The Daam malware is highly sophisticated and includes a number of features designed to steal your data and put your privacy at risk.
The Daam malware has the ability to record all ongoing phone and VoIP calls including calls made through WhatsApp. It can also steal your files and even the contacts from your smartphone.
For instance, the malware has the ability to record all ongoing phone and VoIP calls including calls made through WhatsApp. However, it can also steal your files and even the contacts from your smartphone. Surprisingly, the Daam malware can even steal info on newly added contacts, not just your existing ones.
All of the data stolen by Daam is then sent back to a command and control (C&C) server operated by the hackers behind this malware campaign. It’s worth noting that the malicious apps used to distribute the malware ask for access to sensitive device permissions after installation to gain almost complete access to your Android smartphone.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
If having all of this sensitive data stolen wasn’t bad enough, the Daam malware also utilizes the AES encryption algorithm to encrypt all of the files on an infected Android smartphone without user consent. At the same time, it can also change a smartphone’s device password or PIN to completely lock you out of your phone.
How to stay safe from Android malware that can bypass antivirus apps

Normally with mobile malware, installing one of the best Android antivirus apps and enabling Google Play Protect on your smartphone would be enough to keep you safe. However, in this case, the Daam malware was designed to hide from antivirus apps.
For this reason, the main way to protect yourself from it is by being extremely careful when downloading new apps. Sideloading apps may be convenient but doing so does put your Android smartphone at risk of a malware infection. This is why you want to stick to official Android app stores instead. Likewise, you still want to read reviews and check an app’s rating before installing it as bad apps do manage to slip past Google’s security checks from time to time.
At the same time, you also want to avoid clicking on any links from unknown senders delivered through email or text message on your smartphone. These links can lead to malicious sites that could trick you into installing malware or harvest your information through phishing.
The Daam malware may be new but it’s already quite capable when it comes to stealing data and making things quite difficult for the owners of an infected Android smartphone. This is why this likely won’t be the last time we hear about it.
More from Tom's Guide
- AI-powered thermal cameras could be used to crack your passwords
- Hackers are using this new Gmail scam to steal your personal data
- EvilExtractor malware steals passwords and holds Windows PCs hostage

Anthony Spadafora is the managing editor for security and home office furniture at Tom’s Guide where he covers everything from data breaches to password managers and the best way to cover your whole home or business with Wi-Fi. He also reviews standing desks, office chairs and other home office accessories with a penchant for building desk setups. Before joining the team, Anthony wrote for ITProPortal while living in Korea and later for TechRadar Pro after moving back to the US. Based in Houston, Texas, when he’s not writing Anthony can be found tinkering with PCs and game consoles, managing cables and upgrading his smart home.

 Club Benefits
Club Benefits











