MacKeeper Exposes 13 Million Users: What You Need To Do
MacKeeper sells itself as a security and optimization suite for Mac OS X, but it has trouble keeping its own corporate systems secure.
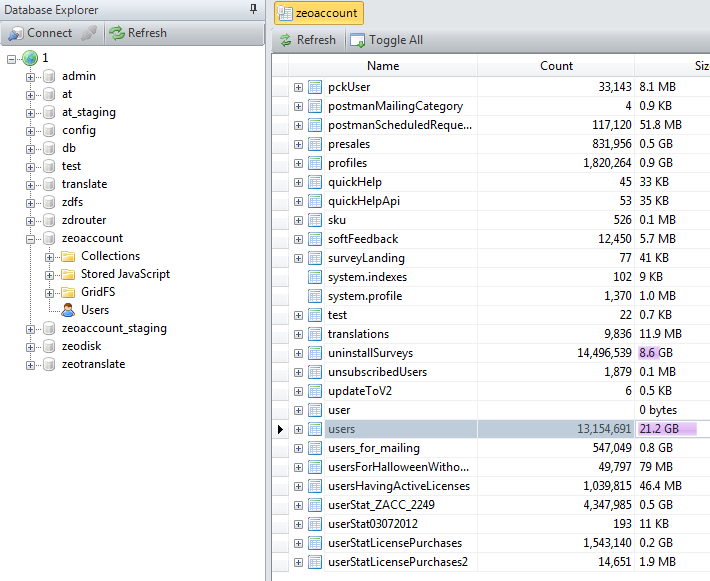
The MacKeeper system maintenance utility suite for OS X, known for advertising with pop-under windows that scare users into installing it, may have given its detractors yet more ammunition. Earlier this week, a security researcher found that the entire company database of MacKeeper maker Kromtech — including a 21GB archive containing information on more than 13 million MacKeeper customers — was online and could be accessed by anyone, without a password.
The user archive contained names, email addresses, usernames, password hashes, phone numbers, IP addresses and system information about MacKeeper clients. It was found by Chris Vickery, an IT professional who was browsing Shodan, a search engine that tracks all Internet-connected devices. Vickery posted proof of his discovery on Reddit and Imgur, and alerted Germany-based Kromtech.
MORE: Best Mac Antivirus Software
Vickery said the Kromtech database was accessible at four different IP addresses. But MacKeeper users can take solace that their credit-card information was not exposed, as a third-party vendor handles purchases.
Kromtech said in a company blog post that it had plugged the database holes, and that nobody aside from Vickery had accessed the database, but its security choices raise questions. On Reddit, Vickery said the MacKeeper passwords were hashed with the weak MD5 encryption algorithm, which lets weak passwords be quickly reversed — just Google "MD5 cracking tool" to see for yourself.
Vickery further said Kromtech did not "salt" any of the passwords, a common technique that adds random characters to text strings to throw off hash-reversal attempts. Kromtech confirmed to Forbes that it used MD5, but said it had been planning to switch to the more secure SHA512 algorithm.
Vickery told independent security reporter Brian Krebs that Kromtech said the exposure was the result of a server misconfiguration made last week. That claim doesn't sit right with Vickery, who says he has found Shodan records of open Kromtech servers dating back to mid-November.
"Let's be serious," opined independent security blogger Graham Cluley. "MacKeeper is supposed to be a security product — and yet it stores passwords that weakly? Its users' details are left on servers open to anyone on the Internet, capable of being accessed without any form of authentication?"
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
MacKeeper has a tricky history. Its original owner, the Ukrainian firm ZeoBIT, which began selling MacKeeper in 2010, paid $2 million this past August to settle a class-action lawsuit over aggressive marketing practices that allegedly tricked users into spending $40 each to upgrade from the free version. In 2013, ZeoBIT sold MacKeeper to Kromtech, which appears to be a company registered in Cologne, Germany, with its principal officers still based in the Ukraine.
Both ZeoBIT and Kromtech have been accused of paying for fake review sites touting MacKeeper, and for paying to bundle it with other Mac software so that users install it by accident. The software itself has received mixed reviews, with some praising its malware-detection engine (licensed from Avira, which makes free Mac antivirus software) and its system-optimizations features.
If you are one of the 13 million users affected by Kromtech's mistake, there are two steps you can take in the wake of this egregious blunder. First, change your MacKeeper password, and check to see if that password was used for other accounts. If so, change those passwords too. Second, consider uninstalling MacKeeper.
If you have a habit of recycling passwords, we recommend that creating and using unique, complex passwords for every important online account (banking, shopping, social media, email — anything that includes personal or financial data) be among your New Year's resolutions.

Henry was a managing editor at Tom’s Guide covering streaming media, laptops and all things Apple, reviewing devices and services for the past seven years. Prior to joining Tom's Guide, he reviewed software and hardware for TechRadar Pro, and interviewed artists for Patek Philippe International Magazine. He's also covered the wild world of professional wrestling for Cageside Seats, interviewing athletes and other industry veterans.
 Club Benefits
Club Benefits





