Billions at risk from Google Chrome security flaw — update your browser right now
New Chrome security flaw is being exploited in spyware attacks

Google has released a new emergency security update for Chrome to fix the fifth zero-day vulnerability in its browser so far this year.
As reported by BleepingComputer, this new zero-day (tracked as CVE-2023-5217) is particularly troubling as hackers have already devised a way to exploit it in their attacks. This is why you’re going to want to update Chrome immediately or risk falling victim yourself.
In a recent security advisory, Google’s Chrome team explained that the latest version of its browser (117.0.5938.132) for Windows, Mac and Linux contains a total of 10 security fixes to patch three high severity vulnerabilities.
According to the advisory, it may take days or even weeks until this emergency security update rolls out to all Chrome users. However, when I went to Chrome’s settings menu and clicked on About Chrome, my browser downloaded the update immediately. As such, if you don’t see the update yet, you should keep checking for it as it’s one you aren’t going to want to put off installing.
Used to install spyware

Of the three vulnerabilities addressed in this new emergency security update, CVE-2023-5217 is the result of a heap buffer overflow weakness in the VP8 encoding in libvpx. It was discovered by Google’s own Clément Lecigne from the company’s Threat Analysis Group (TAG) and can lead to app crashes or arbitrary code execution.
If you’re unfamiliar with TAG, its security researchers have a knack for finding serious zero-days that are used in spyware attacks against high profile individuals like politicians and journalists. In a post on X, TAG’s Maddie Stone confirmed that the zero-day fixed in this latest Chrome update was exploited by hackers to install spyware.
As is often the case with zero-days like this one, Google has yet to share any additional information regarding how it’s been used in attacks in the wild. The reason being is that this gives Chrome’s large install base of 3.22 billion users (according to Statista) additional time to update their browsers.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
Once details about an attack are made public, other copycat hackers may come up with their own exploits for a vulnerability. From here, they then target users that have not yet updated their software to the latest version. Hence, the importance of updating Google Chrome right now.
How to stay safe from attacks exploiting vulnerabilities in Chrome
Just like with the recent zero-day flaws patched by Apple, the most important thing you can do to stay safe in this situation is to update Chrome to the latest version as soon as the update arrives in your browser.
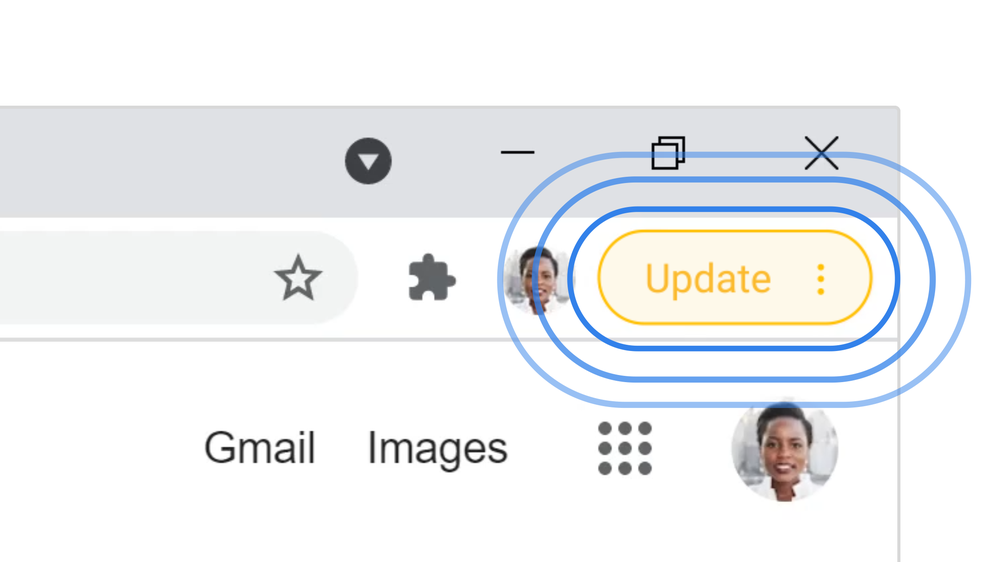
While you can manually check for updates by clicking on the three-dot menu, opening Settings and then going to About Chrome, Google also uses a color-coded warning system to let you know when new updates for its browser are available. These appear as a bubble next to your username and its color changes based on when the update was released. A green bubble means the update is two days old while orange is for a 4-day old update and red shows the update was released at least a week ago. If you need more help though, you can always check out our guide on how to update Google Chrome.
In addition to keeping your browser up to date, you should also be using the best antivirus software on your PC, the best Mac antivirus software on your Apple computer and one of the best Android antivirus apps on your Android smartphone. By using antivirus software alongside installing the latest security updates, you can ensure you’re protected against all manner of cyberattacks.
We probably won’t find out more about how this vulnerability was exploited to install spyware but just knowing that this happened should be enough to convince you that this update isn’t one you want to skip.
More from Tom's Guide
- Hackers are using Facebook Messenger to spread password-stealing malware
- 3 Google Chrome features to activate now if you want to stay safe online
- Chrome is getting a big security upgrade to protect you from malicious extensions

Anthony Spadafora is the managing editor for security and home office furniture at Tom’s Guide where he covers everything from data breaches to password managers and the best way to cover your whole home or business with Wi-Fi. He also reviews standing desks, office chairs and other home office accessories with a penchant for building desk setups. Before joining the team, Anthony wrote for ITProPortal while living in Korea and later for TechRadar Pro after moving back to the US. Based in Houston, Texas, when he’s not writing Anthony can be found tinkering with PCs and game consoles, managing cables and upgrading his smart home.

 Club Benefits
Club Benefits










