To Stop Malware, Restrict User Accounts
A new report confirms that limiting everyday PC use to 'standard' accounts stops almost all malware that can cause serious harm.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
A new report confirms what many security professionals have long presumed: Removing administrator rights from everyday Windows user accounts slows down or stops almost all critical malware infections.
"Ninety-two percent of all vulnerabilities reported by Microsoft with a critical severity rating can be mitigated by removing admin rights," states the enterprise-security firm Avecto, of Manchester, England, in a new report.
MORE: 7 Computer-Security Fixes to Make Right Now
Article continues below"Removing admin rights would mitigate 96 percent of critical vulnerabilities affecting Windows operating systems, 91 percent of critical vulnerabilities affecting Microsoft Office and 100 percent of vulnerabilities in Internet Explorer," Avecto said.
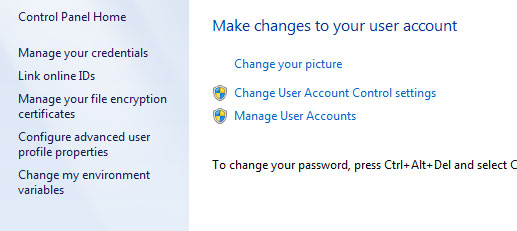
That may sounds complicated, but it's not. There are two kinds of user accounts in Windows machines: Administrator accounts, which can add, alter or remove software and change system-wide settings, and standard accounts, which can't do any of that.
Most malware can do only as much damage as the active user is permitted to do, and malware that infects standard users can't install, alter or delete other software packages. In other words, limiting your own abilities also limits what malware can do.
There are exceptions to these rules — Google Chrome permits user-specific installations for standard users, for example, and some malware can perform "escalations of privilege" to gain administrative rights from a standard account.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
But nearly all malware that meets the Microsoft definition of "critical" — i.e., that can remotely execute code without the legitimate user's permission — can be hindered or stopped by use of standard accounts.
Hence, it's best to perform everyday computer work — Web surfing, emailing, Photoshopping, Microsoft Office work — as a standard user, even if you're the only user for a particular machine. (Windows 7 and 8 standard users can perform administrative tasks if they input the password for an admin account.)
Almost anything nasty that gets in through a Web browser or email attachment will be limited to that account alone and can't damage the rest of the machine.
Unfortunately, most home computers, and even many computers in business or other enterprise environments, are set up so that the primary user has administrative privileges.
"If malware infects a user with admin rights, it can cause incredible damage locally, as well as on a wider network," Avecto states. "Additionally, employees with admin rights have access to install, modify and delete software and files as well as change system settings."
To protect your home computer, create a separate administrator account, give it a strong password and use it only to install or update software. Don't sign into the administrator account for everyday computer use.
Then, use that admin account to downgrade your own primary account, as well as those of other users, to standard (and make sure those accounts have passwords too).
Avecto has posted its full report online, but the company will ask for your name and email address before you can read it.
Follow Paul Wagenseil at @snd_wagenseil. Follow Tom's Guide at @tomsguide, on Facebook and on Google+.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits










