Don't Fall for These Lame WannaCry Scams
WannaCry scams are popping up left and right, even spreading to Android devices -- which aren't vulnerable to the ransomware.
Just as thunder follows lightning, so too do tech-support scams and phony Android apps follow legitimate malware attacks. WannaCry is a particularly fearsome strain of ransomware that made the rounds last week, but if you have a fully patched Windows machine, it poses no threat to you whatsoever.

That's not what tech support scammers want you to believe, though. Not only have WannaCry phone scams been popping up left and right, but the hysteria has even spread to Android devices — which aren't vulnerable in the first place.
The British National Fraud & Cyber Crime Reporting Center highlighted two WannaCry scams targeting Windows users. Given the level of (somewhat justified) hysteria associated with the ransomware, one might expect the deceptions to be incredibly clever. Unfortunately, they’re just run-of-the-mill fake phone support and phishing schemes. No tech-savvy person would fall for these, but here’s how they work, just in case you come across them.
MORE: How to Protect Yourself from WannaCry Ransomware
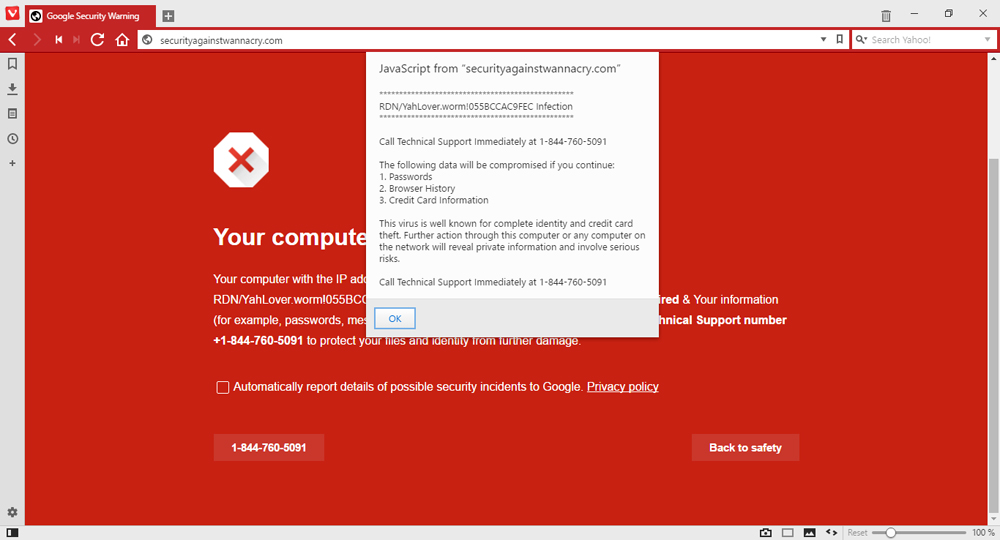
The first scam is a simple splash page that claims a computer is at risk for WannaCry, followed by a popup ad instructing users to call "Technical Support." (It doesn't specify which company's technical support, naturally.)
If a user fails to do so, his or her passwords, browser history, and credit card information are all as good as exposed, the popup warns. If you call the number, scammers will help you install the free Windows Malicious Software Removal Tool — then charge you £320 (about $415 at current exchange rates) for the privilege.
The scam is ridiculous on two levels. First, Microsoft doesn't contact users or offer its phone number over individual security issues — the built-in Windows antivirus software generally does a good job of heading them off at the pass. Second, Microsoft doesn't charge home users for tech support; only business users have to cough up additional dough.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
The second scam is an even more transparent phishing attempt. Users receive an e-mail claiming to be from BT (formerly known as British Telecom), which asks them to "confirm your security upgrade" by providing personal details — name, address, username and password for starters, no doubt.
If the terrible grammar and questionable English ("Deficiency to do so will result in limited access to your profile") don't tip you off, the fact that it asks you to follow a link without providing a URL should. Be sure to check the email domain as well; unless it comes from a legitimate BT address, you can safely ignore it.
Lest you think fake WannaCry tech support is only a British problem, Bleeping Computer saw a browser pop-up from "securityagainstwannacry.com" which implores users to call "technical support" at a North American toll-free number.
As dumb and desperate as the Windows scams are, they can't hold a candle to the sheer idiocy of rash of WannaCry pretenders showing up on Android.
McAfee, a well-known antivirus maker, discussed the rise of Android WannaCry apps on its blog. A quick search through the Google Play Store reveals a host of developers eager to cash in on the ransomware panic. While most WannaCry Android apps are informational or spoofs, some claim to protect Android systems from the dreaded malware — an absolutely ridiculous claim, since WannaCry targets only Windows machines.
Luckily for unsuspecting users, none of the WannaCry antivirus pretenders are spreading malware — yet. But they are inundating users with useless, invasive banner ads to generate revenue for shady overlords in some far corner of the world. Even if WannaCry could infect Android devices, these programs wouldn't protect you; a legitimate Android AV suite might.
To avoid WannaCry scams, take the same precautions you'd take in general online: Verify email addresses and URLs before clicking through, take phone-based tech support with a massive grain of salt and don't download sketchy mobile apps. The scams are easy to avoid this time, but we’ve seen that they can be much cleverer than this.
As for WannaCry itself, just make sure that you keep Windows up to date, and it can't touch you.

Marshall Honorof was a senior editor for Tom's Guide, overseeing the site's coverage of gaming hardware and software. He comes from a science writing background, having studied paleomammalogy, biological anthropology, and the history of science and technology. After hours, you can find him practicing taekwondo or doing deep dives on classic sci-fi.

 Club Benefits
Club Benefits











