Microsoft is blocking these macros in Office to boost your PC security
A small change with huge implications

Microsoft is making a small change in the way that Office files downloaded from the internet are handled on PCs — but the change should lead to a huge improvement in computer security.
Specifically, Microsoft said in a blog post last week, it is making it harder to run macros, tiny but powerful scripts — really mini-programs — that can be embedded into Word documents, Excel spreadsheets, and PowerPoint, Access and Visio files.
"We will continue to adjust our user experience for macros, as we've done here, to make it more difficult to trick users into running malicious code via social engineering while maintaining a path for legitimate macros to be enabled where appropriate via Trusted Publishers and/or Trusted Locations," said Microsoft manager Tristan Davis in the blog post.
The change will begin rolling out in April for users on the Office Preview version 2203. It will then spread to regular consumer and business users and older versions of Office, all the way back to Office 2013, over the next couple of years. Microsoft Office on Macs, Android or iOS devices or the web-based Office won't be affected.
"This is potentially a game changer for the cybersecurity industry and, more importantly, customers," tweeted Windows security expert Kevin Beaumont.
This is potentially a game changer for the cybersecurity industry and, more importantly, customers. The world has changed since VBA was around. It’s a big deal to fix this.It needs to be widely available within a year, and backported to supported non-O365 versions too.February 7, 2022
Let's say your company has a new name, and so you write a small script that at the click of a mouse changes all instances of "Acme Enterprises" in a Word doc to "Weyland-Yutani Corporation" — that's a macro.
Convenient, right? That's why Microsoft has let Office users write and use macros since the mid-1990s. But hackers quickly began to use macros to spray malware, steal passwords and create remote backdoors in computer systems.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
Malicious macros inserted into innocent-looking Word and Excel files that can be emailed are downloaded are now responsible for a huge chunk of hacking attacks. Beaumont estimates that 25% of ransomware attacks begin with a macro.
Microsoft belatedly caught on to this abuse, so with Office 2007 it introduced what it called "Protected View" for files downloaded from websites or received as email attachments.
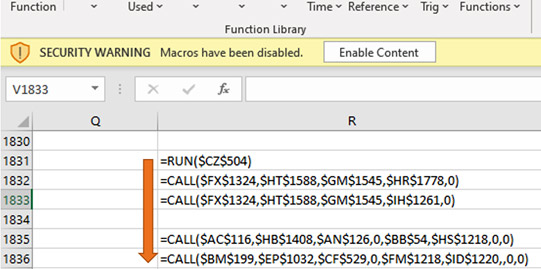
Among other things, Protected View disables macros until the user ( i.e., you) clicks a button labeled "Enable Content" in a yellow bar that says "Security Warning: Macros have been disabled" stretching across the top of the open document or spreadsheet. You've probably seen it.
Well, Protected View hasn't been enough. Many people view it as an inconvenience rather than a security feature and just click Enable Content anyway. Or hackers trick you into clicking it by instructing you to do so in order to see some amazing or important content. (Here's an example of malware that uses poisoned Office files to spread.)
So Microsoft is changing the color of that bar across the document from yellow to red, and changing its text to "SECURITY RISK: Microsoft has blocked macros from running because the source of this file is untrusted."
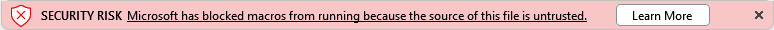
It won't let you enable macros until you click a button labeled "Learn More" — no more Enable Content — and read a Microsoft web page that explains why doing so is a really bad idea.
If you insist on running the macros, the page shows you how, but it's a pain in the patootie. You have to save the file to disk, browse to it in Windows Explorer, right-click the file to view Properties and check "Unblock" in a security setting.
That's definitely going to annoy some Office users. Microsoft is hoping most of them won't bother to enable macros from now on. But it's going to be better overall for the safety and security of all Windows users.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits