Symantec's 'Death of Antivirus' Is a Dangerous Marketing Ploy
Symantec is marketing to IT pros with its proclamation that antivirus is dead. But don't be fooled: Consumers still need antivirus software.
UPDATED 10:45 a.m. ET Thursday with comment from Symantec.
Earlier this week, an executive of the antivirus software giant Symantec told a reporter from the Wall Street Journal that his company's core business model "is dead."
"We don't think of antivirus as a moneymaker in any way," Brian Dye, senior vice president for information security at Symantec, was quoted as saying.
Because Symantec is a leader in the U.S. antivirus software market, both with its core enterprise business and with its Norton consumer division, and its products for all platforms are considered some of the best antivirus software out there, Dye's comments that "antivirus is dead" got a lot of attention.
MORE: Best Windows Antivirus Software
But the attention was undeserved. Dye's declaration was a marketing ploy, pure and simple. It was aimed at corporate IT departments, executive suites and Symantec investors, an attempt to rebrand old, lumbering Symantec as a lean, nimble rapid-reaction team that "gets it" and can keep up with the ever-changing malware threats facing big American companies.
The fact is, antivirus software is not dead, except in Dye's rather limited definition. Everyone needs to keep using it, even on the Mac and Android platforms, which is why we keep track of the best Mac antivirus software and the best Android antivirus apps.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
The problem with comments such as Dye's is that they may mislead the average user to stop using antivirus software, which will only increase the risks posed by the very real threats.
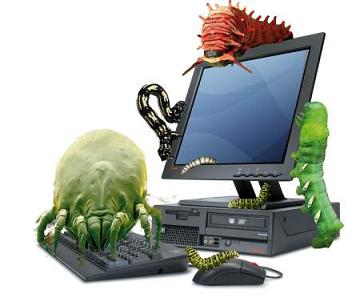
Not what malware looks like, but what it does
Dye's definition of "antivirus" is narrow. He's talking about the business of selling software that scans computers for known malware files, which are detected by their code "signatures," mathematical representations of their unique software profiles.
That business is indeed dead, especially in the enterprise market, because there's no money in it. Only bare-bones antivirus products that are given away free to consumers still practice signature-only detection.
Better AV products — Symantec and Norton included — long ago incorporated more advanced "heuristic" detection systems that not only scan for malware signatures, but detect malware-like behavior.
Heuristic detection is necessary because a lot of malware slips by signature-based systems. Some of it is "zero-day" malware that's never been seen before. Some of it is "polymorphic" malware that changes its code to evade signature blacklists.
Security blogger Brian Krebs noted today (May 7) that many malware creators test their products to make sure they will not be detected by antivirus signature scanners upon initial release.
As the Wall Street Journal noted, Symantec's Norton line of consumer products also includes "a password manager, a spam blocker and a tool that scans a user's Facebook feed to guard against dangerous links" — items that now come standard with high-end consumer antivirus products.
But from a business perspective, heuristic detection and spam blockers aren't enough. Despite decades of assurances by Symantec and its main domestic competitor, McAfee, that antivirus products would keep corporate networks safe, U.S. companies are increasingly finding out the grim truth — that a determined attacker will get through eventually.
That makes Symantec look bad, and it makes smaller firms like Mandiant or FireEye, which get called in to clean up after a corporate data breach or network infection, look good. (Mandiant and FireEye recently merged.)
Lean, mean fighting machine
So Symantec is going to meet the cleanup crews on their own turf. The Wall Street Journal said the company was "creating its own response team to help hacked businesses" and would "sell intelligence briefings on specific threats." It's going to try to provide the intimate, comprehensive service that Symantec slipped away from as it grew large and, arguably, complacent.
There's no doubt that Symantec needs a shakeup. The company recently fired its CEO, the second to get the boot in two years. (The last CEO to leave voluntarily is now chairman of the board at Microsoft.) Its revenue is down, according to the Wall Street Journal, and its Norton consumer line is facing increased competition from well-regarded overseas AV makers such as Kaspersky Lab and Bitdefender.
Yet a post-breach cleanup crew isn't what the ordinary home computer user needs. Joe or Jane Public are not going to be targeted by Chinese state-sponsored hackers looking for corporate secrets.
But Joe, Jane and you are being targeted by cybercriminals who try to steal money and identities with banking Trojans, drive-by downloads, phishing emails and ransomware— all forms of malware that full-fledged, paid and constantly updated antivirus software suites are very good at stopping.
UPDATE: After our article was published, Symantec gave Tom's Guide the following statement:
"The era of AV-only is over. Companies need comprehensive attack prevention that integrates the full range of security technologies. Symantec led the first era of security with antivirus, and it continues to be an important part of our portfolio. Combined with intelligence and other technologies we are pioneering, we can solve larger customer problems that point-based competitors simply cannot do."
Follow Paul Wagenseil at @snd_wagenseil. Follow Tom's Guide at @tomsguide, on Facebook and on Google+.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits











