Microsoft Edge, IE Now Detect, Block Malicious Ads
The latest versions of Microsoft Edge and Internet Explorer can detect and block browser exploit kits, malvertising and drive-by downloads.
No one really likes dealing with online ads; we put up with them because they fund our favorite online content. Unfortunately, this tolerance has been harder to maintain with the growing threat of malvertising, or corrupted ads that can infect a computer with malware as soon as a Web page loads.
If you'd prefer to not use an ad blocker, and keep your favorite sites in the black, the latest versions of Microsoft's Edge and Internet Explorer 11 browsers can purportedly now actively detect and block malicious ads, browser exploit kits and other online nasties. Unfortunately for some users, these features will only work on Windows 10 — and unfortunately for Microsoft, they didn't work flawlessly for us.
Internet Explorer 11 and Edge both use SmartScreen, a Microsoft-exclusive Web-content filter introduced in 2009 with Internet Explorer 8. SmartScreen has always done its best to prevent phishing and malware attacks by matching websites to a whitelist of known good URLs, and to a blacklist of known bad ones — a form of passive detection similar to Chrome's Google Safe Browsing.
But as a posting this week on the Microsoft Edge Dev Blog explained, the latest Microsoft updates pushed out in the December 2015 Patch Tuesday give SmartScreen the power to actively detect and block malicious ads, browser exploit kits and other malware that triggers drive-by downloads, whether the affected websites are known or not.
MORE: Best Antivirus Software and Apps
Drive-by downloads are just what they sound like. If you visit an infected website, malware will try to penetrate your browser and install itself on your system, often without any kind of prompt or user click. In recent years, bundles called browser exploit kits have arisen that throw many pieces of malware at a browser at once; in the past year, exploit kits embedded in online ads have become rampant.
Some exploit kits use previously unseen "zero-day" malware that is hard to identify and countered by no software patch. But by looking for factors common to exploit kits, SmartScreen can theoretically detect and prevent even zero-day attacks upon browsers.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
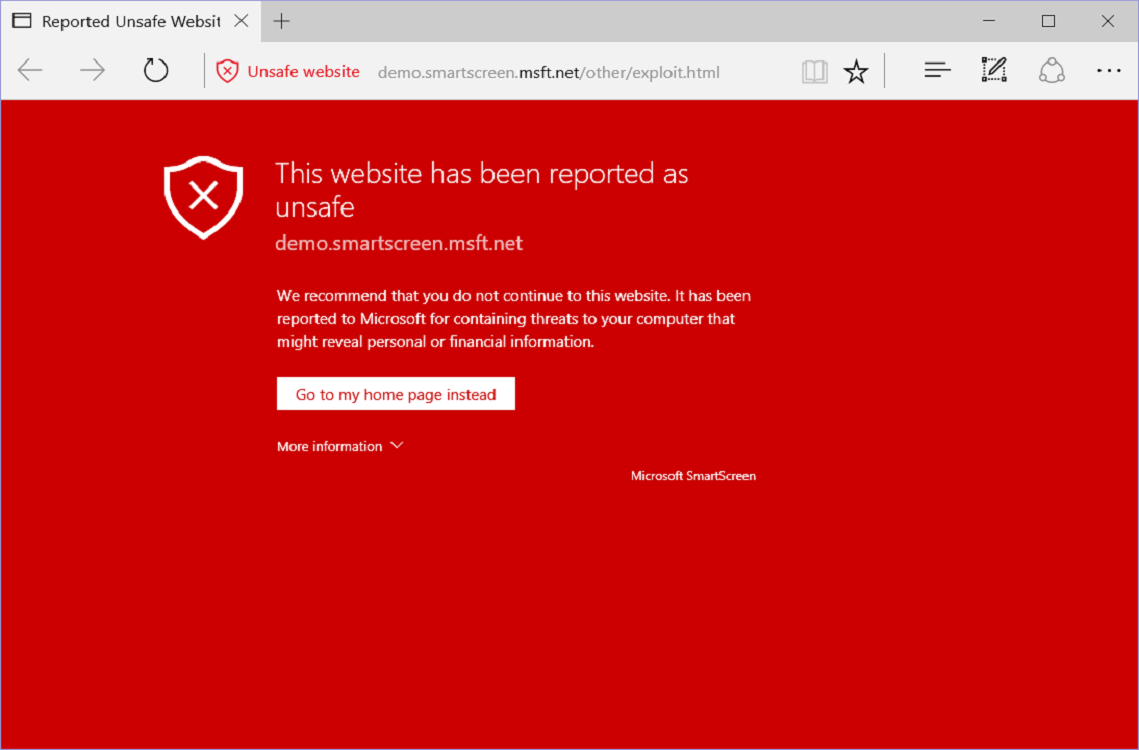
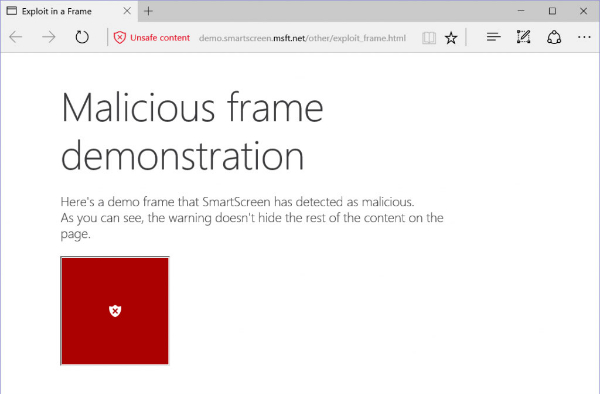
The program's malvertising protection is surprisingly subtle. If SmartScreen detects an unsafe site, it, like Google Safe Search, will turn the entire screen red and warn users that they should not proceed. Malvertising, though, can often spread to perfectly legitimate sites (such as Yahoo or the New York Times), so blocking the entire page would be overkill. SmartScreen can block just the malicious ads, replacing them with a red warning and leaving the rest of the page untouched.
By default, SmartScreen is activated in Edge, in Internet Explorer 8 through 11 and in Windows itself, beginning with Windows 8. But the active malware-blocking feature only works on Windows 10 that has installed last week's software patches.
If you've deactivated SmartScreen in the past and want to turn it back on, doing so is very simple. Enter the Control Panel, and select Action Center. From there, you'll have the option to turn SmartScreen on or off. Tom's Guide recommends that you do this, but SmartScreen's active detection may not yet work as well as Microsoft expects.
In our own rather unscientific tests, SmartScreen on a fully updated version of Edge running in Windows 10 failed to stop an Adobe Shockwave Flash-based Trojan found on a second-tier porn site. (To counter such attacks, it's best to disable Adobe Flash and Shockwave browser plugins.) The Trojan was immediately detected in Edge's cache by a trial version of McAfee LiveSafe installed on the PC, which may be fortunate, as Microsoft's own antivirus programs tend to be subpar.

Marshall Honorof was a senior editor for Tom's Guide, overseeing the site's coverage of gaming hardware and software. He comes from a science writing background, having studied paleomammalogy, biological anthropology, and the history of science and technology. After hours, you can find him practicing taekwondo or doing deep dives on classic sci-fi.

 Club Benefits
Club Benefits










