Chrome zero-day bug patched after hackers used it in their attacks — update your browser now
New security update to patch this Chrome zero-day flaw is rolling out now

If you haven’t updated Google Chrome recently, now is the time to do so as Google has released a new security update to address a zero-day vulnerability that has been actively exploited in the wild by hackers.
So far this year, this is the third zero-day bug that the search giant has patched in its browser. The first one was a similar type confusion bug in the V8 JavaScript engine (tracked as CVE-2022-2033) while the second zero-day (tracked as CVE-2023-2136) was found in Skia, Chrome’s 2D graphics library.
Now though according to a new security bulletin from Google, the company has provided some but not many details on a new zero-day bug (tracked as CVE-2023-3079). This is a high-severity vulnerability discovered by the search giant’s own Clément Lecigne from its Threat Analysis Group.
While Google isn’t releasing all of the details yet to give Chrome users time to patch their browsers, it did reveal that it “is aware that an exploit for CVE-2023-3079 exists in the wild”.
Type confusion bug
We’ll likely find out more about this new Chrome zero-day once Google has deemed that enough users have installed the latest security updates to patch it.
In the meantime though, we do know that like the first Chrome zero-day discovered this year, it’s a type confusion bug in the browser’s V8 JavaScript engine. This engine is responsible for executing code within Chrome and as BleepingComputer points out, type confusion bugs typically arise when the engine misinterprets the type of an object during runtime.
Type confusion bugs like this one can easily be exploited by hackers in their attacks since they can be used to manipulate a system’s memory and to execute arbitrary code.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
While zero-day vulnerabilities are always something you want to take seriously and patch as soon as possible, they usually tend to be exploited by state-sponsored hackers that go after high-profile targets like government officials and journalists. Still, these attacks could eventually trickle down to ordinary users which is why keeping your browser up to date is so important.
How to stay safe from zero-day attacks
When it comes to staying safe from cyberattacks exploiting zero-day vulnerabilities, the most important thing you can do personally is to keep all of your software up to date. This means installing the latest security updates right when they become available instead of putting off doing so.
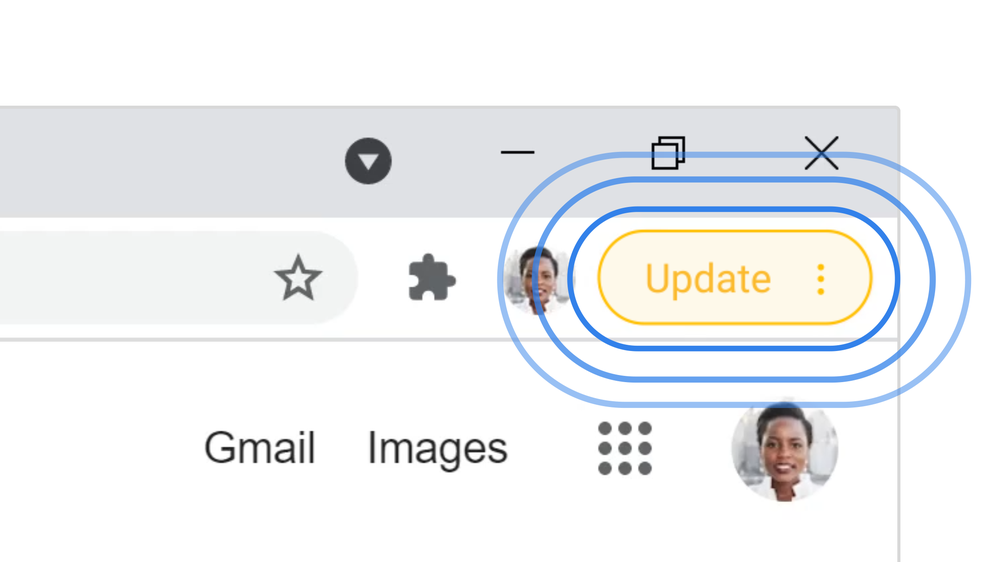
Finding out whether or not there’s a new Chrome update for instance is quite easy to do. When an update is available, you’ll see a bubble next to your profile picture in Google’s browser which is color-coded based on when it was released. The bubble turns green for a 2-day old update, orange for a 4-day old update and red when an update was released at least a week ago.
While clicking on the bubble will download the latest version of Chrome and it will be installed the next time you relaunch your browser, you can also manually update Google’s browser by clicking on the three dots next to your profile picture, clicking on Help and then About Google Chrome. This takes you to the browser’s settings page where you can check to see if you’re running the latest version of Chrome.
Besides keeping your browser up to date, you should also be running the best antivirus software on your Windows PC, the best Mac antivirus software on your Apple computer and one of the best Android antivirus apps on your Android smartphone. This way, you can ensure you’re protected from malware and other viruses.
Once enough Chrome users have installed the latest security update, we’ll likely hear more from Google on this new zero-day vulnerability.
More from Tom's Guide
- Android apps with 30 million downloads contain SpinOk Android malware
- These are the best internet security suites for protecting all of your devices
- Hackers are using pictures to trick you into clicking on phishing links

Anthony Spadafora is the managing editor for security and home office furniture at Tom’s Guide where he covers everything from data breaches to password managers and the best way to cover your whole home or business with Wi-Fi. He also reviews standing desks, office chairs and other home office accessories with a penchant for building desk setups. Before joining the team, Anthony wrote for ITProPortal while living in Korea and later for TechRadar Pro after moving back to the US. Based in Houston, Texas, when he’s not writing Anthony can be found tinkering with PCs and game consoles, managing cables and upgrading his smart home.

 Club Benefits
Club Benefits











