Period-Tracking Apps Also Track You, Researchers Find
Many widely used period-tracking apps have sloppy security and user privacy, researchers find.
UPDATED with a statement from Planned Parenthood.
BROOKLYN, New York — Many Android apps that track women's menstrual cycles fail to properly protect their users' privacy and security, two researchers said at the Summercon hacker conference on Friday (Jun. 14).

All 10 period-tracking apps also ran a number of programs that tracked their users. Most had weak encryption, stored sensitive data in plain text, requested invasive permissions, or transmitted information about the phone and its user to third parties. A few apps viewed other accounts on the device, or got exact location information. Some programs even allowed the user to transmit medical information to her doctor directly, which would seem to be a violation of the Health Insurance Portability and Accountability Act (HIPAA) of 1996.
Article continues below"Patient privacy should be held to a high standard," said Jacqueline Xavier, a medical student at Indiana University who presented the research along with data scientist Wendy Edwards. "Yet most of these apps are not considered to be medical devices by the FDA, and most of the apps were created without medical-expert involvement."
Before installing and using a period tracker, analyze the permissions it takes by clicking the MORE link on its Google Play Store page, scrolling down to the App Permissions link at the bottom of resulting screen and clicking See More. If an app wants to know your location or find accounts on the device, consider whether it really needs to know those things.
Using an iPhone instead of an Android phone won't necessarily be better. The researchers focused on Android apps because iOS apps are difficult to take apart and analyze, but other studies have shown that third-party apps for both platforms can leak sensitive data equally badly.
MORE: Best Fitness Trackers
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
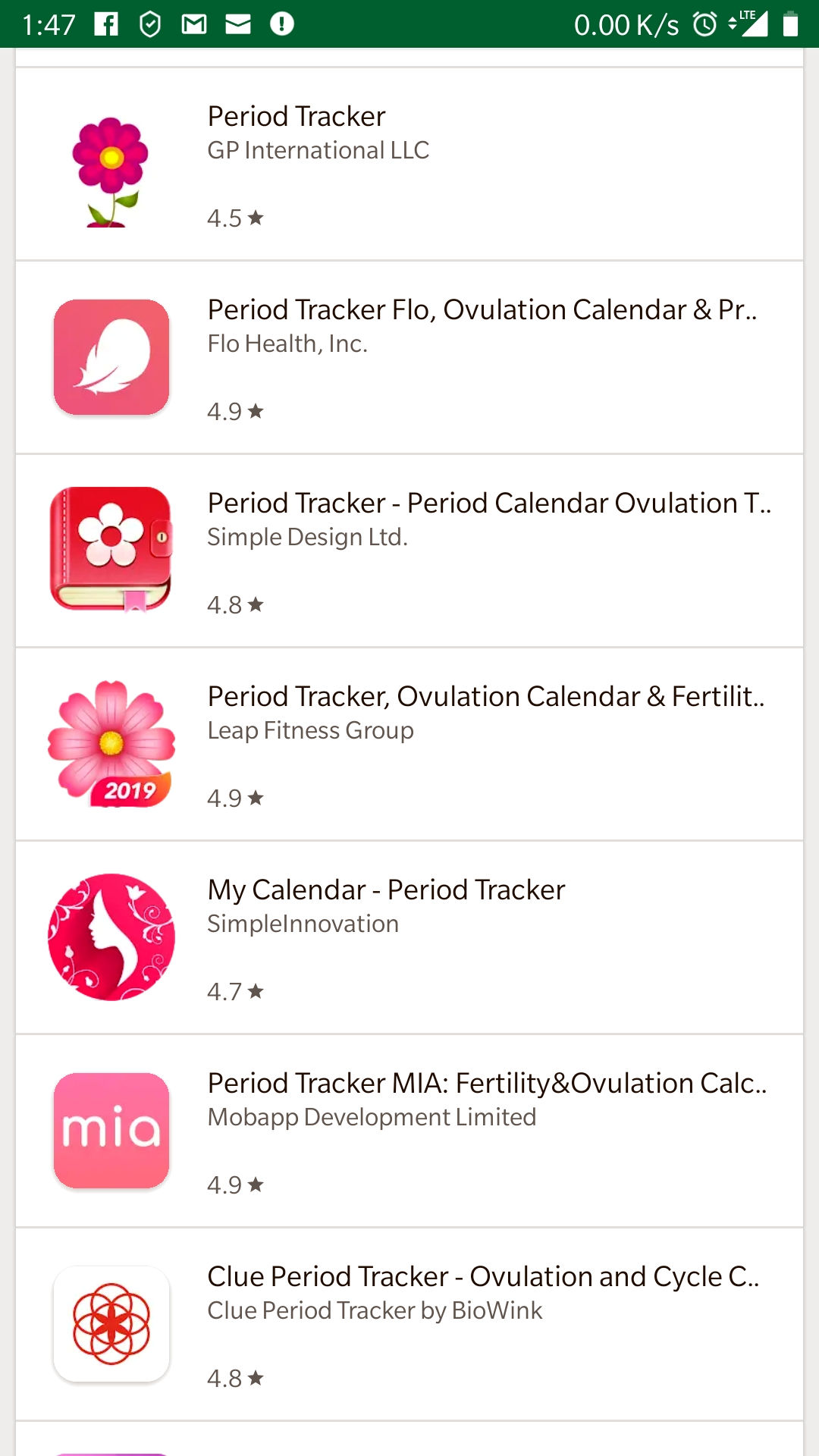
The 10 apps analyzed were Clue Period Tracker, developed by Biowink; Eve Period Tracker, developed by Glow; My Calendar, developed by SimpleInnovation; Ovia Fertility, developed by Ovia Health; Spot On, developed by Planned Parenthood; and five different apps simply named Period Tracker, developed respectively by Amila, Flo, GP International, Leap Fitness Group and Simple Design Ltd.
The apps commonly sent data about the phone, such as its fixed hardware ID number or its temporary advertising ID, to third parties. Generally, the programs shared the phone's make, model and version of Android being run.
Many of the apps also pinged Facebook upon startup, leading Xavier and Edwards to wonder what kind of information was being exchanged between the apps and Facebook. However, when they set up fake Facebook accounts on Android emulators, Facebook quickly detected their efforts and deleted the accounts.
If all this seems trivial, Edwards reminded the audience that "femtech," as technology designed to monitor women's health is called, was on track to attract $1 billion in venture-capital investment this year. It's becoming big business, but there doesn't seem to be an interest in keeping the technology private or secure.
The researchers were asked whether they had reached out to the developers of the period-tracking apps with their findings. Edwards replied that they did not. Other studies in recent years had found and publicized similar results, she said, but the app developers had not tightened up privacy or security as a result.
Tom's Guide has reached out to Planned Parenthood for comment, and we will update this story when we receive a reply.
UPDATE: Planned Parenthood gave Tom's Guide a statement regarding its Spot On app.
"The Spot On app was developed with Planned Parenthood's healthcare experts, with information from our medical standards and guidelines," the statement said in part. "The data in the Spot On app is stored locally on each user's phone, so you're the only one who has access to it."

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits










