Dozens of Android Apps Infected with Korean Adware
A well-hidden strain of adware wound up in the Google Play Store, and it could compromise your phone’s performance.
One of the easiest ways to avoid malicious software on Android phones is to install apps only from the Google Play Store. Google vets every program that crosses into its storefront, and the vast majority of them are perfectly safe. (Even if the vast majority of them are also perfectly banal.)
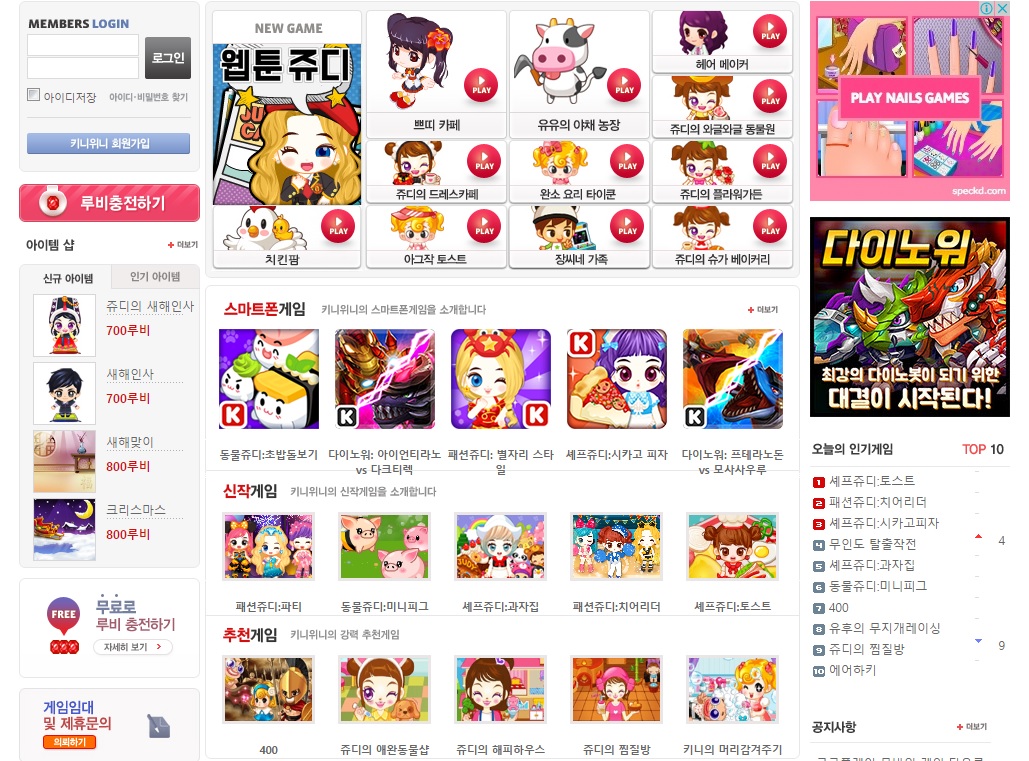
Still, a clever developer can sneak something dangerous into otherwise innocuous code, and that’s just what Korean game-maker Enistudio Corp., part of a larger Korean company called KiniWini, may have done. "Judy" isn’t only the mascot for the company’s casual games; it’s also the name that security researchers have given to a well-hidden strain of adware that could compromise your phone's performance. If you've got an app from Enistudio, you might want to delete it.
Israeli security firm Check Point investigated what it called "The Judy Malware," although the "malware" label is debatable. While the Judy apps do indeed install shady software on your phone and do so without your knowledge or explicit permission, they don't actually harm your phone, steal your data or compromise your privacy. Rather, the Judy apps are adware — programs that hog your phone’s resources to generate ad-click revenue for dubious paymasters in distant corner of the world.
MORE: Best Android Antivirus Apps
The good news is that Google has already removed the Judy apps from the Play store — all 50 or so of them. While the vast majority of Judy apps were casual games from Enistudio starring the eponymous pink-haired mascot, a handful were finance, music, calendar or fashion apps from other Korean developers.
You can scrutinize Check Point’s blog post for a full listing of the offending apps, but even if you’ve installed one, you don’t have to worry. Simply uninstalling the program will take the adware with it.
Avoiding similar apps in the future may be a more difficult proposition. Check Point explains that some Judy apps had been in the Play Store for years, and up to 18.5 million people may have downloaded the various programs. Most of the apps had positive, organic user reviews.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
The adware may have been part of a recent update, or it may have been part of the software since the beginning — Check Point can't tell for sure. (It appears that the malicious code was added to each app after installation.) The episode is a dismaying reminder that while Google Play’s security protocols may be good, they’re not perfect, and even a minor breach can affect millions of users.
The best way to avoid malicious Android apps is to install them only from legitimate sources, such as the Google Play Store, but that would not have helped in this case. An Android antivirus program may have caught the programs’ suspicious behavior — or not, since the programs weren’t technically compromising the phone or the information on it in any way.
The sad truth is that there’s no surefire way to avoid every piece of unwanted software on the internet. Sometimes, all you can do is use common sense, install an antivirus program and hope for the best.

Marshall Honorof was a senior editor for Tom's Guide, overseeing the site's coverage of gaming hardware and software. He comes from a science writing background, having studied paleomammalogy, biological anthropology, and the history of science and technology. After hours, you can find him practicing taekwondo or doing deep dives on classic sci-fi.

 Club Benefits
Club Benefits











