This is the one thing to look out for in scam emails
Beware of blank subject lines

Cybercriminals and scammers use a wide variety of social engineering techniques to get you to open their malicious emails though one in particular is a dead giveaway and worth looking out for in your inbox.
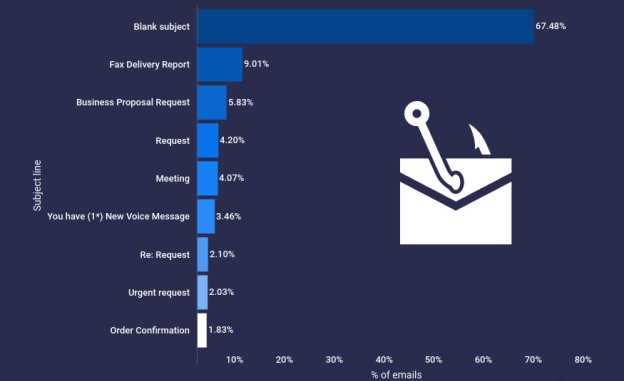
According to a new blog post from Atlas VPN based on data from the Expel Quarterly Threat Report Q1 2022, two thirds (67%) of scammers leave the subject line empty in their malicious emails. While other frequently used subject lines can also indicate that an email is likely a scam, a blank one is a major red flag.
By leaving an email’s subject line blank, scammers hope to peak the interest of potential victims that are interested in finding out why they received this email in the first place. As a blank subject line may have already thrown them off, users are more likely to click on links in the body of the email or to respond to it.
Article continues belowOther subject lines to look out for
Although blank subject lines are the most common, other subject lines frequently used in malicious emails are business related or try to instill a sense of urgency.
Of the subject lines examined by Expel’s security operations center, Fax Delivery Report was the second most common at 9.01 percent followed by Business Proposal Request (5.83%) and Request (4.20%).
With more employees working from home, cybercriminals have also begun using “Meeting” (4.07%) as a subject line in their malicious emails. When it comes to targeting consumers, “You Have (1*) New Voice Message” (3.46%) and “Order Confirmation” (1.83%) are frequently used subject lines.
All of these tactics used in phishing and scam emails are designed to get you to click on an email or the links contained within it without much thought. This is why you should always exercise caution when opening and responding to emails from unknown senders.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
How to spot a phishing email

Besides a blank subject line, poor grammar and spelling are another way to quickly identify phishing emails.
Since many cybercriminals and scammers are not from English-speaking countries, their writing may contain grammatical errors that native speakers wouldn’t normally make. At the same time though, some attackers make errors on purpose in order to filter out less observant people as they are likely easier targets.
Carefully examining the domain of an email address is another useful trick when it comes to spotting phishing emails. As a general rule of thumb, no legitimate organization will send out emails from a public email domain like Gmail as they all have their own email domains and company accounts. This can be quite useful when it comes to brand impersonation as emails from Amazon only come from @Amazon.com, so if an email uses any other domain, it’s likely a fake.
Finally, no company will ever ask you to send sensitive information like your payment details over email. If an email contains a link or attachment that requires you to provide personal data, it’s likely a scam.

Anthony Spadafora is the managing editor for security and home office furniture at Tom’s Guide where he covers everything from data breaches to password managers and the best way to cover your whole home or business with Wi-Fi. He also reviews standing desks, office chairs and other home office accessories with a penchant for building desk setups. Before joining the team, Anthony wrote for ITProPortal while living in Korea and later for TechRadar Pro after moving back to the US. Based in Houston, Texas, when he’s not writing Anthony can be found tinkering with PCs and game consoles, managing cables and upgrading his smart home.

 Club Benefits
Club Benefits










