Think twice before scanning this QR code — it could be a phishing scam
Just like with links, QR codes can also be malicious
As online shopping has quickly become the norm over the last few years, cybercriminals now frequently use fake delivery notifications as bait in their scams.
This makes sense as those who shop online often may sometimes forget about a package or miss a call from a courier like FedEx or UPS.
According to a new blog post from the cybersecurity firm Kaspersky, a new phishing scam impersonating DHL is currently making the rounds online. However, what sets this campaign apart is how the cybercriminals behind it are using QR codes to avoid detection.
Just like with other phishing campaigns, this one begins with an email that appears to come from DHL. While the sender’s email address is a random set of words (a red flag to look out for), the body of the email is quite convincing and includes the company’s logo along with a fake order number and the receipt for a package.
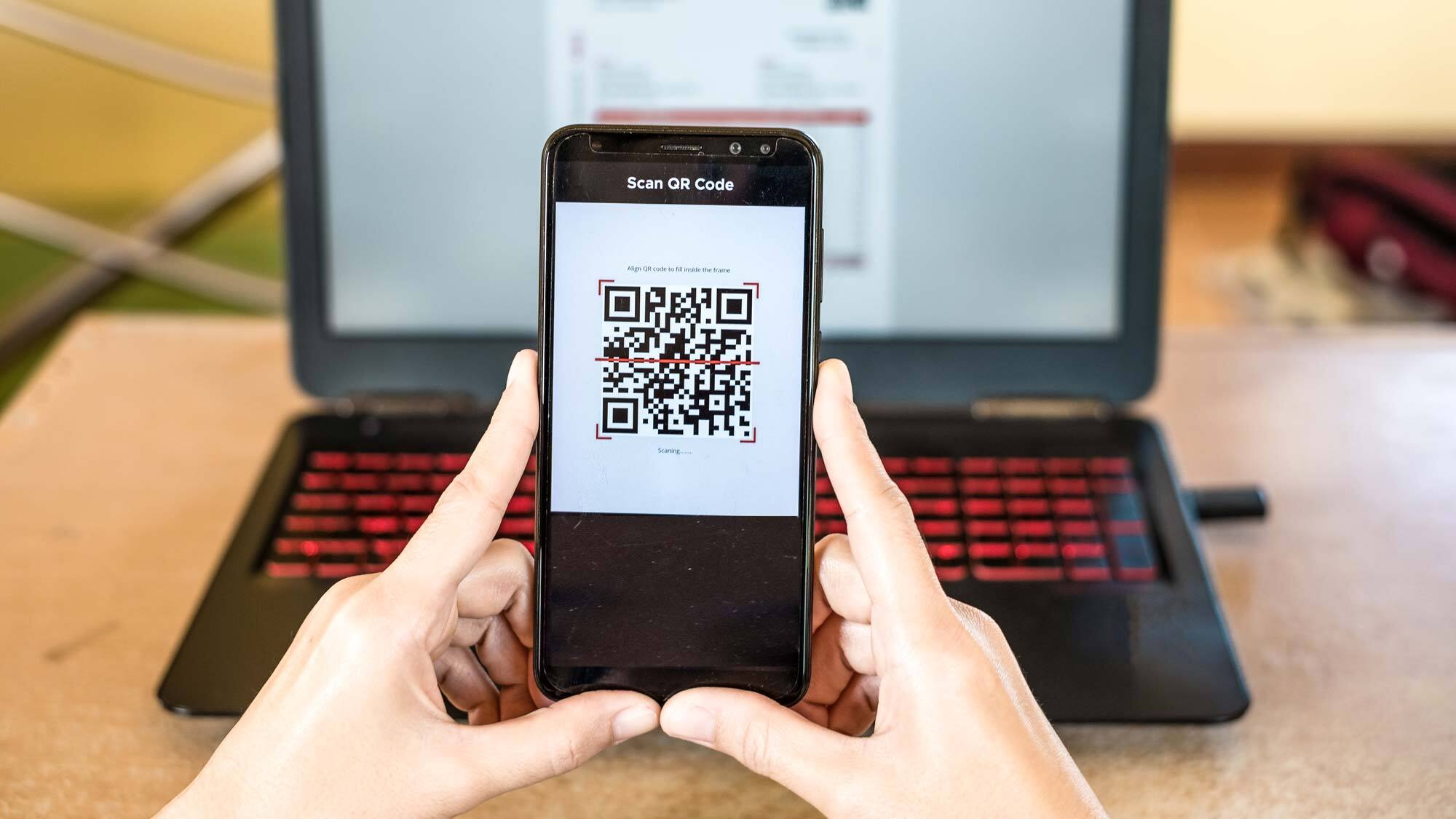
The message itself explains that an order has arrived at the recipient’s local post office but the courier was unable to deliver it in person. Usually these types of phishing emails would feature a link to “resolve the issue” but this time the cybercriminals responsible have used a QR code (complete with the DHL logo) and for good reason.
All of the best email services automatically scan for malicious links in messages that can lead to phishing sites or malware. However, many of them can’t yet scan for malicious QR codes which is why cybercriminals have begun using them more frequently in their schemes.
Switching from a bigger screen to a smaller one
Besides bypassing email security solutions, this campaign also makes use of QR codes to make it easier to trick users once they arrive on the cybercriminals’ phishing page.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
According to Kaspersky, the idea seems to be that a victim will open the phishing email on their computer and then switch to their smartphone to scan the QR code. As a result, the malicious site will open on a smaller screen where signs of phishing are harder to spot. For instance, on mobile devices, URLs are not fully visible which makes them more difficult to inspect.
If a user does scan the QR code in the fake email from DHL, they’re taken to a website with small text and informed their package will arrive in 1-2 days but to receive it, they’ll need to enter their first name, last name and address. While this doesn’t raise any suspicions, the next page asks them to share their bank or credit card details to pay for the delivery. It’s worth noting that DHL actually requires payment for deliveries in advance which makes this another red flag.
As making charges to the card after harvesting its details would be a dead giveaway, the cybercriminals behind this campaign are more likely planning to sell the payment data they’ve collected on the dark web at a later date.
How to stay safe when scanning QR codes

When Japanese engineer Masahiro Hara came up with the idea for QR codes back in 1994, he created them for use in automobile manufacturing to make it easier to keep track of car parts in factories. He never intended for them to be so ubiquitous or used for payments.
Now though, QR codes have become a popular fixture online and in the real world at places like cafes and restaurants. Despite the risk that a QR code can take you to any website online and even dangerous ones, many users don’t even think before scanning them. This phishing scam and others like it use this to their advantage to dupe unsuspecting users.
For this reason, you should always inspect the URL of a QR code before proceeding to any website. To make this easier to do, Kaspersky offers a free app for Android and iOS called Kaspersky QR Scanner that will tell you if a QR code points to a dangerous site. Likewise, competing antivirus maker Sophos has created its own QR code scanner app called Intercept X that provides the same functionality.

Anthony Spadafora is the managing editor for security and home office furniture at Tom’s Guide where he covers everything from data breaches to password managers and the best way to cover your whole home or business with Wi-Fi. He also reviews standing desks, office chairs and other home office accessories with a penchant for building desk setups. Before joining the team, Anthony wrote for ITProPortal while living in Korea and later for TechRadar Pro after moving back to the US. Based in Houston, Texas, when he’s not writing Anthony can be found tinkering with PCs and game consoles, managing cables and upgrading his smart home.

 Club Benefits
Club Benefits











