Facebook Data Breach Hits 50 Million Users
Facebook said nearly 50 million user accounts had been compromised in a data breach that involved possible takeover of user accounts.
UPDATED 7:30 p.m. EDT Sept. 28 with additional information about how the breach happened, and why non-Facebook accounts might be affected as well.
UPDATED 1:00 p.m. EDT Oct. 12 with Facebook revising its estimate of the number of directly affected accounts to 30 million.
Facebook said today (Sept. 28) that nearly 50 million accounts had been compromised by unknown attackers, and that more than 90 million users were forcibly logged out of their accounts this morning as a security precaution. At least for the moment, affected users will not have to change their passwords.
Article continues below 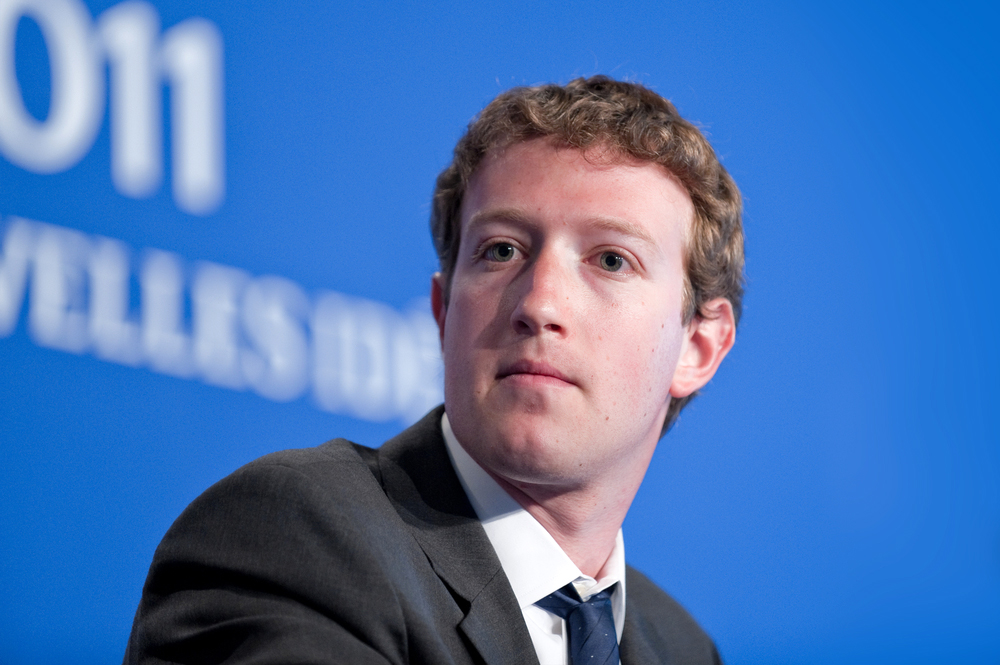
The attackers abused a flaw in Facebook's "View As" function to steal access tokens for the 50 million accounts, which would have granted them long-term temporary access to the accounts.
It's not yet known whether any Facebook accounts were taken over, whether any legitimate users were locked out of their own accounts, if any personal information was stolen, or even who the attackers were or what they wanted.
Nevertheless, just as a precaution — and only if you remember your Facebook password — it might be best to log out of your Facebook account on all devices, then log back in again. You can check on which devices you're logged into Facebook here.
MORE: How to Stop Facebook from Sharing Your Data
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
Despite Facebook's well-publicized privacy issues, the social network's internal security has been pretty good, and it's never had a data breach of this size or type before.
"We're taking it really seriously," Facebook CEO Mark Zuckerberg told reporters in a conference call, according to The New York Times. "I'm glad we found this. But it definitely is an issue that this happened in the first place." UPDATE: A full transcript of the conference call is here.
How the Facebook attack worked
Facebook vice-president of product engineering Guy Rosen gave further details in a Facebook company blog posting today.
"On the afternoon of Tuesday, September 25, our engineering team discovered a security issue affecting almost 50 million accounts," Rosen wrote. "Attackers exploited a vulnerability in Facebook's code that impacted 'View As,' a feature that lets people see what their own profile looks like to someone else."
"This allowed them to steal Facebook access tokens which they could then use to take over people's accounts," he added. "Access tokens are the equivalent of digital keys that keep people logged in to Facebook so they don’t need to re-enter their password every time they use the app."
Access tokens, also known as session tokens, access cookies or session cookies, are bits of code that keep you logged into Facebook on your computer or smartphone, even after you reboot the device. The tokens are not permanent, but will last for months or even years because companies have found that people generally want to stay logged into frequently used online services as long as possible.
Rosen said the security hole that permitted the attack had been fixed, and that law enforcement had been notified.
He said that the access tokens of the nearly 50 million accounts known to be affected were reset. So were those of an additional 40 million account that had "been subject to a 'View As' lookup in the past year."
Rosen said that if more accounts are found to be affected, their access tokens will also be reset. He also said that anyone who had trouble logging back into Facebook should visit Facebook's online Help Center.
Owners of affected accounts will have to log back into Facebook on every device they normally use to access the service, but at least for the moment, they will not have to change their passwords, Rosen said.
Access tokens are generally not tied directly to passwords, and are assigned to a user session only after the account holder has been logged in.
"This attack exploited the complex interaction of multiple issues in our code," Rosen wrote. "It stemmed from a change we made to our video uploading feature in July 2017, which impacted 'View As.' The attackers not only needed to find this vulnerability and use it to get an access token, they then had to pivot from that account to others to steal more tokens."
So who attacked Facebook?
The size of the attack hinted that at least part of it might have been automated. It would be pretty hard for humans to manually compromise 50 million accounts in a short time.
"From Facebook's description, it looks like the attackers created some kind of session cookie worm," Virus Bulletin editor Martijn Grooten wrote on Twitter. "I can't imagine you can run this reliably unless you own (or can rent) a large botnet that you can use a proxies to make the requests from."
"The fact that 50m accounts were taken over and that we haven't, as far as I'm aware, seen any massive spam campaigns suggests it may have been an information-gathering campaign by a nation state, or similar actor," Grooten added. "It's far too early to be certain of course."
Lesley Carhart, a threat hunter at security firm Dragos, cautioned against ascribing the attack to a nation-state because such attribution is often used by companies to dodge responsibility.
"The presumption that the Facebook compromise was nation-state backed (without any solid proof) merely plays to Facebook's potential defense and helps them dismiss liability," Carhart tweeted. "The 'nation state cyberattack' defense using popular misconceptions is a real thing."
Facebook's annus horribilis
This has been a dreadful year for Facebook, including the Cambridge Analytica data-sharing scandal in March that saw Zuckerberg and other top Facebook executives answering heated questions in the U.S. Congress and Britain's Parliament.
The company has also been facing heat for allowing its platform to be abused by Russian trolls attempting to influence elections in Western countries, including the 2016 U.S. presidential election, and for allegedly favoring left-wing rather than right-wing discussions on its pages.
In the past year, the founders of WhatsApp, bought by Facebook in 2014, have left the company. This week, the founders of Instagram, bought by Facebook in 2012, announced their immediate departures. Facebook's chief information-security officer, Alex Stamos, left this past summer, and his duties and team were reassigned to other departments.
Yesterday (Sept. 27), the company was accused of using mobile-phone numbers, provided by users to enable the two-factor authentication security feature, to target ads to individual smartphones, and to use members' phone numbers obtained from other members' contacts lists to do the same.
UPDATE Sept. 28: In that conference call with reporters, Rosen clarified that the vulnerability arose because the attackers were able to access the video uploader — specifically one designed to wish people a happy birthday in video form — while using the "View As" function.
"When the video uploader showed up as part of View As — which it wouldn’t do were it not for that first bug — and it generated an access token which is — again, wouldn’t do, except for that second bug — it generated the access token, not for you as the viewer, but for the user that you are looking up."
"Those attackers then, in order to run this attack, needed not just to find this vulnerability, but they needed to get an access token and then to pivot on that access token to other accounts and then look up other users in order to get further access tokens," Rosen added.
In a separate Twitter dialogue with Slate reporter Will Oremus, whoever runs the official Facebook Twitter account admitted that Instagram and Oculus accounts might be affected if they were linked to a Facebook account.
"The vulnerability was on FB but if you have a FB account that has been affected that's linked to an Oculus or IG account, you will have to unlink them and re-link them," the Facebook Twitter account said. "No WhatsApp users have been impacted."
It wasn't immediately clear whether third-party accounts that offered a "log in with Facebook" feature were affected, but Oremus hinted that they might be.
UPDATE Oct. 12: In a new statement, Facebook said the number of affected accounts was actually closer to 30 million. Of that group, 15 million had names, phone numbers and/or email addresses accessed by the attackers.
Another 14 million accounts had additional data compromised — "username, gender, locale/language, relationship status, religion, hometown, self-reported current city, birthdate, device types used to access Facebook, education, work, the last 10 places they checked into or were tagged in, website, people or Pages they follow, and the 15 most recent searches."
The remaining one million accounts had no data accessed.
"We're cooperating with the FBI, which is actively investigating and asked us not to discuss who may be behind this attack," Facebook said.
Best Identity Protection Services

Get it. IdentityForce UltraSecure+Credit is the best overall service for both credit monitoring and identity protection. It also protects your account with two-factor authentication.

It's worth it. Get LifeLock Ultimate Plus if you're very worried about having your identity stolen and you also need antivirus software. But you can get better credit monitoring for less with IdentityForce UltraSecure+Credit.

Good, but not the best. Identity Guard isn't bad, but for about the same price, IdentityForce UltraSecure+Credit offers more comprehensive personal-data and credit-file monitoring.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits










