IPVanish has a serious security flaw on Mac – and OpenVPN users need to take note
A newly discovered vulnerability could let attackers take full control of your Mac

Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
Update: IPVanish has released an update for its Mac app (version 4.10.3) which fixes the recent OpenVPN vulnerability.
You'll be notified in-app but you can also download the update from IPVanish's website.
IPVanish confirmed that the issue only affected users who's device had already been accessed by a hacker and who had manually changed to OpenVPN.
The VPN also confirmed that there was no intrusion into its server network, and the integrity or encryption of IPVanish VPN connections was not impacted. The scope was limited, with no users affected beyond those listed above.
A critical vulnerability has been discovered in IPVanish's Mac VPN app which impacts anyone who has used the OpenVPN protocol.
Research by cybersecurity firm SecureLayer7, published on March 4, 2026, discovered the flaw in IPVanish's VPN client on macOS.
This vulnerability would allow a local attacker to sidestep Apple’s security architecture and run code with the highest level of system privileges. The vulnerability affects IPVanish users on macOS 10.13 and later.
If you've never used the OpenVPN protocol, you're not affected.
IPVanish is a VPN veteran, and consistently challenges the best VPNs. It has a strong track record of privacy and security, and we would expect an imminent fix. There is no indication of any risk being presented to users of its other apps – including iOS, Android, and Windows.
SecureLayer7 has released a full breakdown of how the exploit works. It’s unclear whether SecureLayer7 have reached out to IPVanish before disclosing the exploit, but as of writing IPVanish has not released an update – although one is being worked on.
How the vulnerability works
IPVanish’s macOS app is split into two different parts. The first is the regular app that you interact with, which is run with user-level privileges. Basically, it can’t change system settings or do anything particularly sensitive on your Mac.
However, to carry out all of the networking on the back end that your VPN needs to keep your internet traffic private, IPVanish runs a separate helper tool with system level privileges. This tool can automatically perform admin-level tasks that you’d usually need your admin password for, like installing new software or creating new user accounts.
Ideally, this helper tool would only take commands from the IPVanish client.
However, SecureLayer7 discovered that this helper tool doesn’t confirm whether the commands it’s taking are actually from the IPVanish client.
This means that any user that’s logged into the Mac (or any piece of software already running on it) could connect to the IPVanish helper and run system-level commands without the admin password, giving them total access to your machine at the deepest level.
The vulnerability centres around the OpenVPN protocol and how it's implemented and operates on a technical level. If you're solely a WireGuard user, this flaw shouldn't pose a risk to you or your Mac.

What should you do?
At the time of writing, IPVanish has not released a patch for this vulnerability. But it said it was aware of the vulnerability and its team is working on a fix to be "released as soon as possible."
The VPN company added that "all macOS users will receive an automatic prompt to update to the latest version."
IPVanish recommended removing the "OpenVPN Driver" from your IPVanish app, if you have used the OpenVPN protocol. To do this:
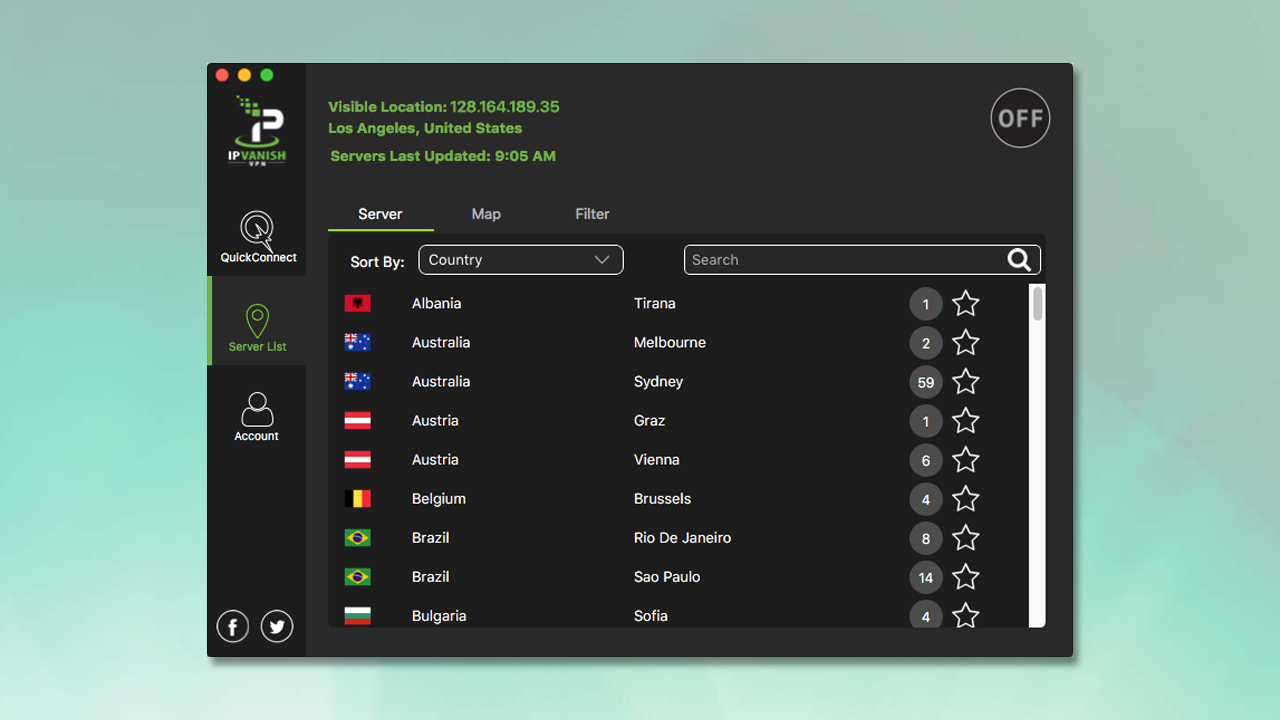
- Open the IPVanish macOS Desktop software
- Click Settings → Protocol → OpenVPN
- Look for OpenVPN Driver and select Uninstall
IPVanish said "this will solve the vulnerability before the upcoming release." As far as we know, this vulnerability only affects Mac devices, so iOS devices are fine.
WireGuard is the default protocol for new installations. If you've only used this standard configuration then you won't be impacted.
It’s important to note that this vulnerability does require attackers to have local access to your machine. It can’t be exploited over the internet unless used as part of a larger attack chain.
Essentially, a hacker would have to figure another way to get access to your computer over the internet.
Once they’re in, the IPVanish vulnerability would allow them to carry out what’s known as a local privilege escalation attack.
IPVanish said it "takes all vulnerabilities very seriously," and identifies "issues through a combination of internal testing and ongoing monitoring." It couples this with disclosures from researchers and the security community through its Vulnerability Disclosure Program.
The VPN continued by saying: "While these processes are designed to catch problems before release, complex software environments mean that some edge cases may only surface through real-world usage or external research."
"If an issue is flagged, our teams immediately assess its scope and potential impact, develop a fix, and prioritize getting that update into a release as quickly as possible. At the same time, we provide guidance to help users mitigate potential risks as the update rolls out."
We test and review VPN services in the context of legal recreational uses. For example: 1. Accessing a service from another country (subject to the terms and conditions of that service). 2. Protecting your online security and strengthening your online privacy when abroad. We do not support or condone the illegal or malicious use of VPN services. Consuming pirated content that is paid-for is neither endorsed nor approved by Future Publishing.

Sam Dawson is a cybersecurity expert who has over four years of experience reviewing security-related software products. He focuses his writing on VPNs and security, previously writing for ProPrivacy before freelancing for Future PLC's brands, including TechRadar. Between running a penetration testing company and finishing a PhD focusing on speculative execution attacks at the University of Kent, he still somehow finds the time to keep an eye on how technology is impacting current affairs.
- George PhillipsStaff Writer
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Club Benefits
Club Benefits










