WannaCry Ransomware Outbreak Isn't Over Yet
The WannaCry ransomware attack hit China especially hard Monday, and experts warned that new strains were about to appear.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
Monday saw a subdued but significant repeat of Friday's global ransomware attack, as the WannaCry worm, also known as WanaCrypt, WanaCrypt0r or WCry, infected a new wave of Windows PCs in areas that it had partly missed on Friday.
Reports came in of hundreds of organizations, including many universities, hit by WannaCry in China, where software piracy is commonplace and where tens of millions of computers still run the outdated Windows XP.
MORE: Best Antivirus - Top Software for PC, Mac and Android
Article continues belowHowever, Australia and New Zealand, which had prepared for a WannaCry onslaught as their workweek started Monday morning, seemed to be largely spared. It may be that more computers in those countries had installed the Windows patch, released in March, that prevents WannaCry infection.
After a 22-year-old English security researcher accidentally shut down the initial WannaCry wave Friday, experts warned that it was only a matter of time before new variants appeared. Two showed up Saturday, although one had a similar "kill switch" and was quickly shut down as well. The other lacked a kill switch but had a malformed payload: It infected computers, but failed to encrypt any files.
It remained unclear how WannaCry initially infected computers. Contrary to many media reports, no phishing emails bearing WannaCry had been found, an unusual development for such a widespread attack.
How to protect yourself from WannaCry
To protect yourself from WannaCry infection, run Windows Update as soon as possible, and install all available patches marked "Important." You can start Windows Update from the Control Panel in Windows 7, from the Settings screen (the gear icon) in Windows 10, or by simply opening the Start menu, typing in "Windows Update" into the search field and hitting the Enter key.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
Microsoft has taken the very unusual step of creating patches for Windows XP and Windows 8 as well, despite the fact that those platforms are no longer supported. If Windows Update doesn't grab the patches automatically for such machines, you have may have to install them manually — links to those updates, including instructions for installation, are at the bottom of this Microsoft security advisory.
What to do if you're infected with WannaCry
Unfortunately, if your machine has already been infected by WannaCry and you're seeing the ransom demand, there's not much you can do. WannaCry locks image, email, office, movie and database files with a 2048-bit encryption algorithm, which would take thousands of years for even the strongest supercomputer to crack.
If those files are worth more to you than $300, you may want to consider simply paying the ransom. There's no guarantee that the criminals behind WannaCry will honor their end of the bargain, and security experts generally advise against paying ransoms, but dozens of people have already paid off the WannaCry operators, and we're not hearing reports that their files haven't been unlocked after the ransom payment. UPDATE: We are now indeed seeing second-hand reports of files left encrypted despite ransoms being paid. If that's true, then paying off the ransom will not help.
You may be able to recover some files using a free utility called ShadowExplorer, which locates "shadow" backups made as part of normal Windows processes. Common undelete tools may recover files that WannaCry deleted after making encrypted copies, but Symantec's analysis of the malware code indicates that files in the Desktop and My Documents folders will have been completely overwritten.
WannaCry's evolution
Some experts theorized that WannaCry was spreading as a true computer worm, jumping from one corporate network to another as it scanned the internet for corporate servers that had erroneously left the Microsoft SMB resource-sharing protocol activated on network port 445.
Other experts noted that many enterprise networks may have already been quietly infected with NSA-developed malware called DOUBLEPULSAR, which installs a "backdoor" in Windows PCs and servers. Backdoors can be kept in reserve for later infections, and DOUBLEPULSAR was stolen from the NSA at the same time as ETNERNALBLUE, the NSA software exploit that punches a hole through Microsoft's SMB protocol.
Whatever the case, as soon as WannaCry infects a single machine in an enterprise or small-business network, it tries to use ETERNALBLUE to quickly spread among all Windows machines connected to that network. Any machine that has not installed Windows security patches for at least three months, or is running expired versions such as Windows XP or Windows 8, will be vulnerable.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.
-
Avast-Team You're right -- on Friday, at the time of our threat team's initial post, we had seen about ~50,000 detections.Reply
https://blog.avast.com/ransomware-that-infected-telefonica-and-nhs-hospitals-is-spreading-aggressively-with-over-50000-attacks-so-far-today
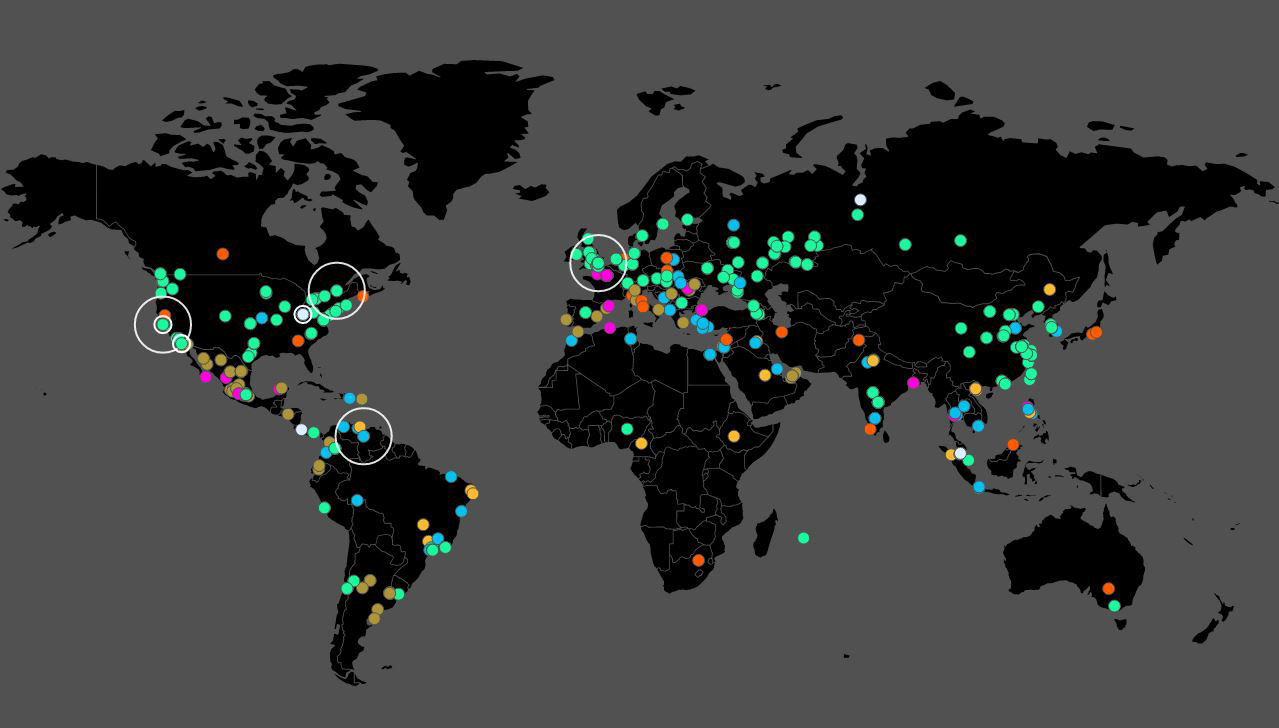
As of today, we're up to 213,000 detections across 112 countries. -
Paul Wagenseil Reply19697488 said:wait..... does it mean those using windows 10 are safe?
Windows 10 machines are vulnerable to WannaCry if they have not installed the March, April or May Windows Update packages from Microsoft. This story has video of a Windows 10 virtual machine being infected by WannaCry: http://www.tomsguide.com/us/wannacry-infection-video,news-25094.html
 Club Benefits
Club Benefits










