NymVPN launches split tunneling and post-quantum encryption in hefty update
Version 2026.7 adds granular traffic control and the beginnings of quantum-resistant encryption
NymVPN has released version 2026.7, introducing two headline features: split tunneling for Windows users and post-quantum key exchange across all platforms. The update marks a significant step forward for the privacy-focused VPN, built on a decentralized network designed to protect both traffic and metadata.
Split tunneling, available on Windows in beta, lets users choose which apps route through the VPN tunnel and which connect directly to the internet, giving greater flexibility without sacrificing protection where it matters. It's a feature already common among leading VPNs, and one that NymVPN is now extending to more platforms in future releases.
The post-quantum key exchange, delivered via NymVPN's newly developed Lewes Protocol, targets a specific threat: the ability of well-resourced adversaries to record encrypted traffic today and decrypt it once quantum computers become powerful enough to do so. It's the first phase of a broader post-quantum roadmap.
NymVPN – a fast-growing decentralized VPN
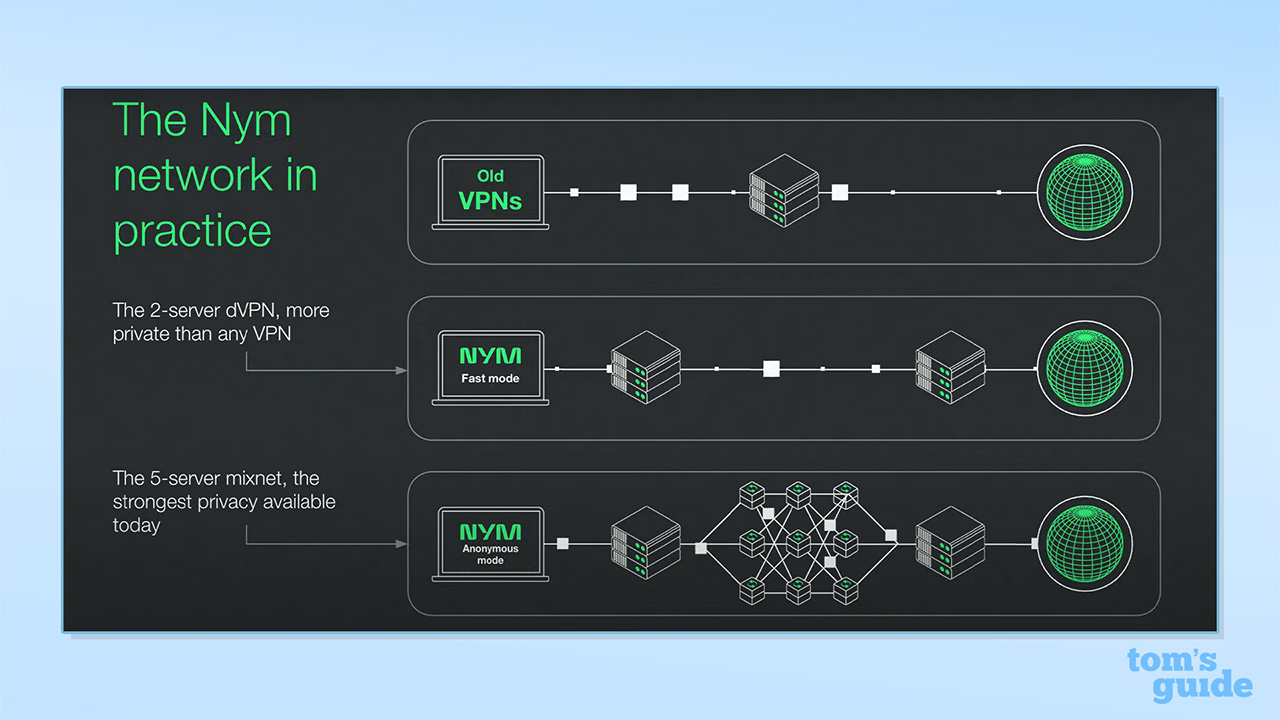
NymVPN is quite different to most VPNs, working on a decentralized "mixnet" network. This means at no point does any one node in the network know both your real IP address and your destination.
Prices start at a reasonable $2.39 per month, which also includes a 7-day free trial.
Why are these updates important?
Split tunneling is one of the most practical tools a VPN can offer. It lets you decide which apps use the VPN connection and which bypass it entirely, which is useful if you want to stream local content or access banking apps that block VPN traffic, while keeping other activity protected. With NymVPN, the feature is currently in beta on Windows, with Linux and iOS support in development.
To enable it, head to the app's settings and select which apps to include or exclude from the tunnel.
The post-quantum key exchange addresses a longer-term but increasingly urgent threat. Intelligence agencies and other well-resourced actors are known to collect encrypted internet traffic now, with the intention of decrypting it once quantum computers are capable enough to break today's encryption standards. For anyone whose data needs to stay private for years, such as journalists, activists, or anyone handling sensitive information, that window of exposure is already open.
To try the new Lewes Protocol, toggle it on in NymVPN's Settings. Note that it's optional for now, and will become the default after a short testing period.
What are post-quantum keys?
Post-quantum keys refer to cryptographic keys generated using algorithms designed to resist attacks from quantum computers. Most VPNs today rely on encryption methods, such as RSA and elliptic curve cryptography (two widely used standards), that are mathematically secure against classical computers but would be vulnerable to a sufficiently powerful quantum machine.
NymVPN's implementation targets the key exchange: think of this as the digital handshake that kicks off every VPN session, where your device and the server agree on a shared set of encryption keys before any of your traffic moves. If that handshake is compromised, the rest of the encryption doesn't matter.
The Lewes Protocol hardens it against quantum attack by layering an additional secret key on top of the existing WireGuard-based mechanism, meaning an attacker would need to break both to get in. As a bonus, NymVPN says the protocol also improves connection startup times.
It's worth noting that this isn't a complete transition. NymVPN's post-quantum rollout is a three-phase process: the Lewes Protocol covers phase one, with protection for mix node communications and the core packet routing system that underpins NymVPN's anonymous mode still to come. Nym plans to use hybrid approaches during the transition, combining post-quantum algorithms with classical encryption to maintain compatibility.
Some rivals have moved faster on this front. NordVPN and ExpressVPN have already fully implemented post-quantum protection when using certain protocols, so NymVPN is catching up rather than leading the field here.
We test and review VPN services in the context of legal recreational uses. For example: 1. Accessing a service from another country (subject to the terms and conditions of that service). 2. Protecting your online security and strengthening your online privacy when abroad. We do not support or condone the illegal or malicious use of VPN services. Consuming pirated content that is paid-for is neither endorsed nor approved by Future Publishing.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
You must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.

 Club Benefits
Club Benefits











