Plenty of Fish Hooks Up Users with Malware
If you've recently visited the online dating website Plenty of Fish, it's time to do a system scan for malware, thanks to a malicious ad.
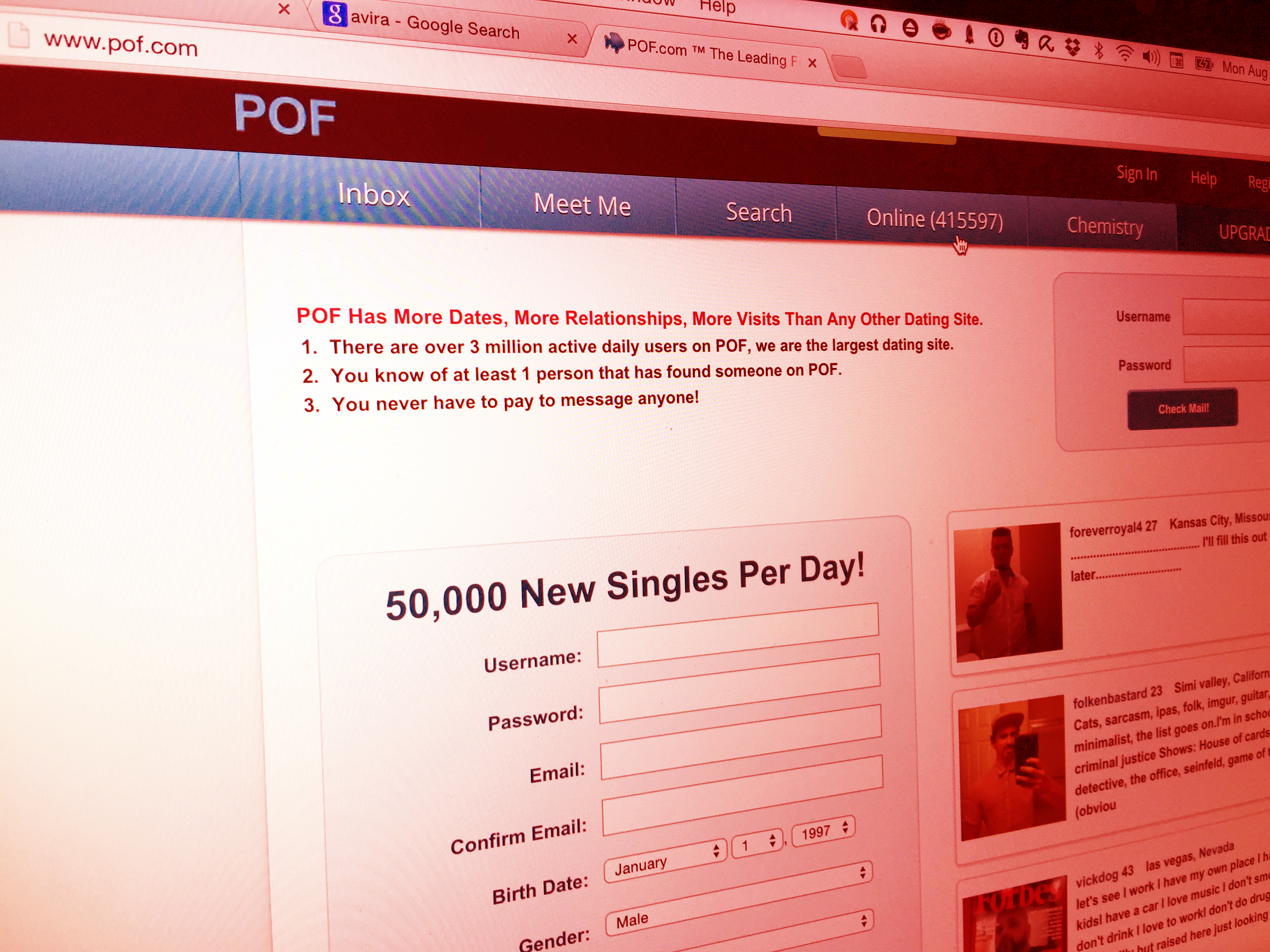
An ad that ran last week on the website of online matchmaking service Plenty of Fish (PoF.com) may have muddied the waters of the dating pool by dropping malware on users' computers. Plenty of Fish claims to be the largest online dating site with more than 3 million daily active users; if any of those users did not have antivirus software installed, they are at risk of malware infection.
The malicious advertisement was distributed by an ad network placing ads on PoF.com, and used Google's URL shortener to redirect visitors to a series of websites that ended with the Nuclear browser exploit kit, which infects systems (mostly Windows PCs) through vulnerabilities in widely used browser plug-ins such as Adobe Flash Player, Silverlight, Adobe Reader and Java.
MORE: Best Antivirus Protection for PC, Mac and Android
The security firm Malwarebytes brought this covert malware installation to light, but it has not been able to capture the payload of the attack. A day before Malwarebytes discovered this attempt, though, it found an online banking Trojan known as Tinba that was also being distributed by the same ad network that (almost certainly unwittingly) placed the malware on Plenty of Fish.
Unlike the recent hack of online discreet-arrangement service Ashley Madison, it does not appear that user data of Plenty of Fish users is at risk. But infection by a malicious ad could be just as bad; other browser exploit kits have infected Windows PCs with encrypting ransomware, which locks up some or all the data on a computer until the user pays several hundred dollars to free it.
Malvertising is an unsavory byproduct of the decentralized, lightning-fast online-ad ecosystem. At least five intermediaries, and often many more, separate the operators of a website from the people running ads on it. It's all too easy for dodgy-ad creators to inject malicious ads into the whirlpool of online-ad bidding, then sit back and profit as others distribute the ads far and wide.
Those who have recently visited Plenty of Fish, as we did to report this story, should scan their systems for any malware, and make sure they use a robust, self-updating antivirus product that screens websites for malicious software.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.

Henry was a managing editor at Tom’s Guide covering streaming media, laptops and all things Apple, reviewing devices and services for the past seven years. Prior to joining Tom's Guide, he reviewed software and hardware for TechRadar Pro, and interviewed artists for Patek Philippe International Magazine. He's also covered the wild world of professional wrestling for Cageside Seats, interviewing athletes and other industry veterans.

 Club Benefits
Club Benefits











