Software
Latest about Software
-
-

Windows 10 dies in October — 3 ways to avoid upgrading to Windows 11
By Alex Wawro Published
-

iCloud was down — live updates on Apple outage hitting Photos, Mail and more
By Dave LeClair Last updated
-

Google Earth celebrates its 20th anniversary with historical street view and new AI insights
By Scott Younker Published
-

Fixing your broken Windows 11 PC is about to get even harder — here’s why
By Anthony Spadafora Published
-

Windows parental controls are crashing Chrome — here's the workaround
By Alyse Stanley Published
-
 Usenet
UsenetThe best Usenet providers in 2025
By Richard Sutherland Last updated
-
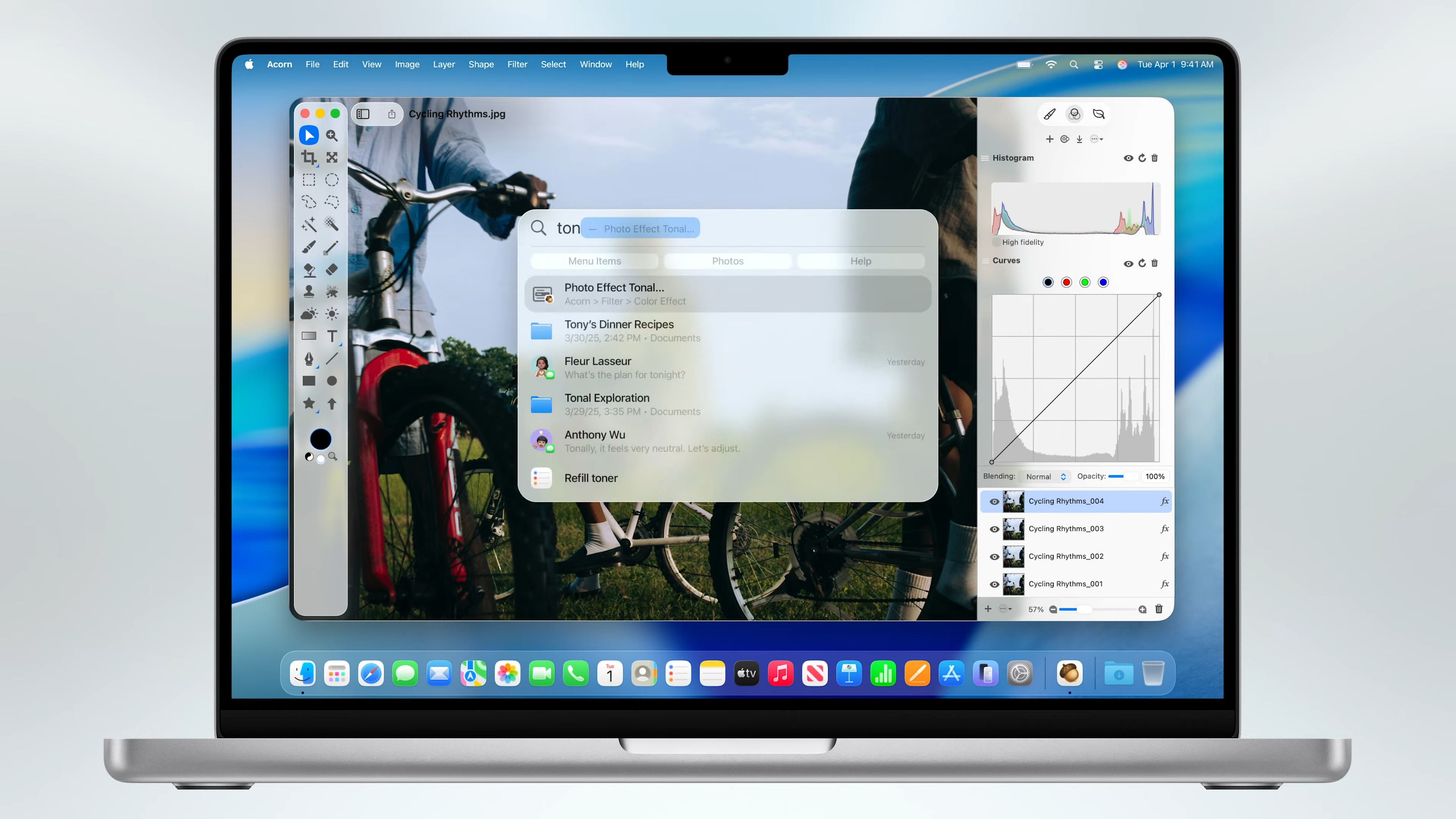
Apple is ripping a page from Microsoft with this macOS Tahoe feature — and I couldn't be happier
By Alex Wawro Published
-
Explore Software
Creative Software
-
-
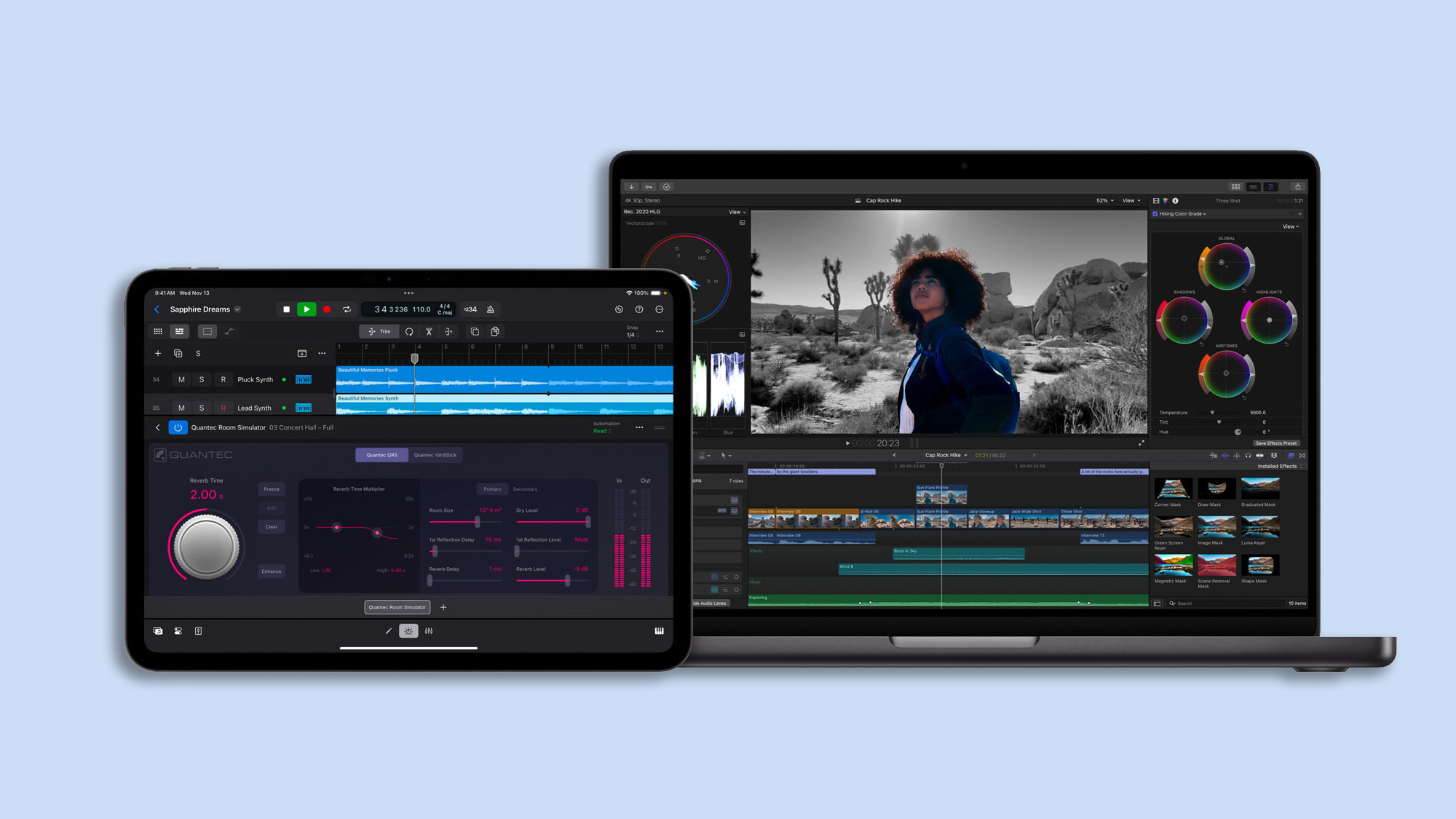
Apple releases Final Cut Pro 11 for Mac, plus iPhone and iPad updates — here's what's new
By Dave LeClair Published
-

Snapfish review: You can do better
By Dan Havlik Last updated
-
 Sponsored
SponsoredWondershare Filmora’s latest update streamlines video editing and content creation with new tools
By Sponsored Published
SPONSORED -

Best video editing software in 2024
By Christian Rigg Last updated
-

Best photo editing software
By Rod Lawton Last updated
-

Microsoft confirms when Adobe apps will natively run on Qualcomm Snapdragon PCs
By Scott Younker Published
-
 Sponsored
SponsoredWondershare Filmora Offers a new AI Music Generator for Video Editors at All Levels
By Sponsored Published
SPONSORED -

How to create a double exposure in Photoshop
By Peter Wolinski Published
-
 Review
ReviewAdobe Creative Cloud cloud storage review
By Ritoban Mukherjee Last updated
-
Finance Software
-
-

California bringing digital driver's licenses to Apple, Google Wallets
By Scott Younker Last updated
-
H&R Block vs. TurboTax: Comparing the top online tax services
By Melissa Perenson Last updated
-
Cash App Taxes 2022 review: Simplified free tax experience
By Melissa Perenson Published
-

FreeTaxUSA 2022 Edition review
By Melissa Perenson Published
-

TaxAct Deluxe review: Tax pro help for everyone
By Melissa Perenson Published
-

TaxSlayer Classic 2023 (tax year 2022) review
By Melissa Perenson Published
-

Intuit TurboTax Deluxe 2022 review: Tax returns with the best guidance
By Melissa Perenson Published
-

H&R Block Deluxe 2023 review (tax year 2022): Friendly, colorful, helpful tax preparation experience
By Melissa Perenson Published
-
How to add money to Venmo
By Jonathan Lesser Last updated
-
Mobile Apps
-
-

Google Earth celebrates its 20th anniversary with historical street view and new AI insights
By Scott Younker Published
-

Ads are coming to WhatsApp — here's where you'll see them (and where you won't)
By Lucy Scotting Published
-

Best photo collage apps in 2024
By Jackie Dove Last updated
-

The best photo organizer apps in 2025
By John Corpuz Last updated
-

Google Maps lets you customize your car icon on Android and iOS — here’s how to do it
By Tom Pritchard Published
-

Android phones can now play the legendary Windows XP Space Cadet pinball game for free
By Scott Younker Published
-

You can finally make Google Translate the default on iPhone and iPad
By Dave LeClair Published
-

Apple Pay was down — live updates on the outage
By Scott Younker Last updated
-
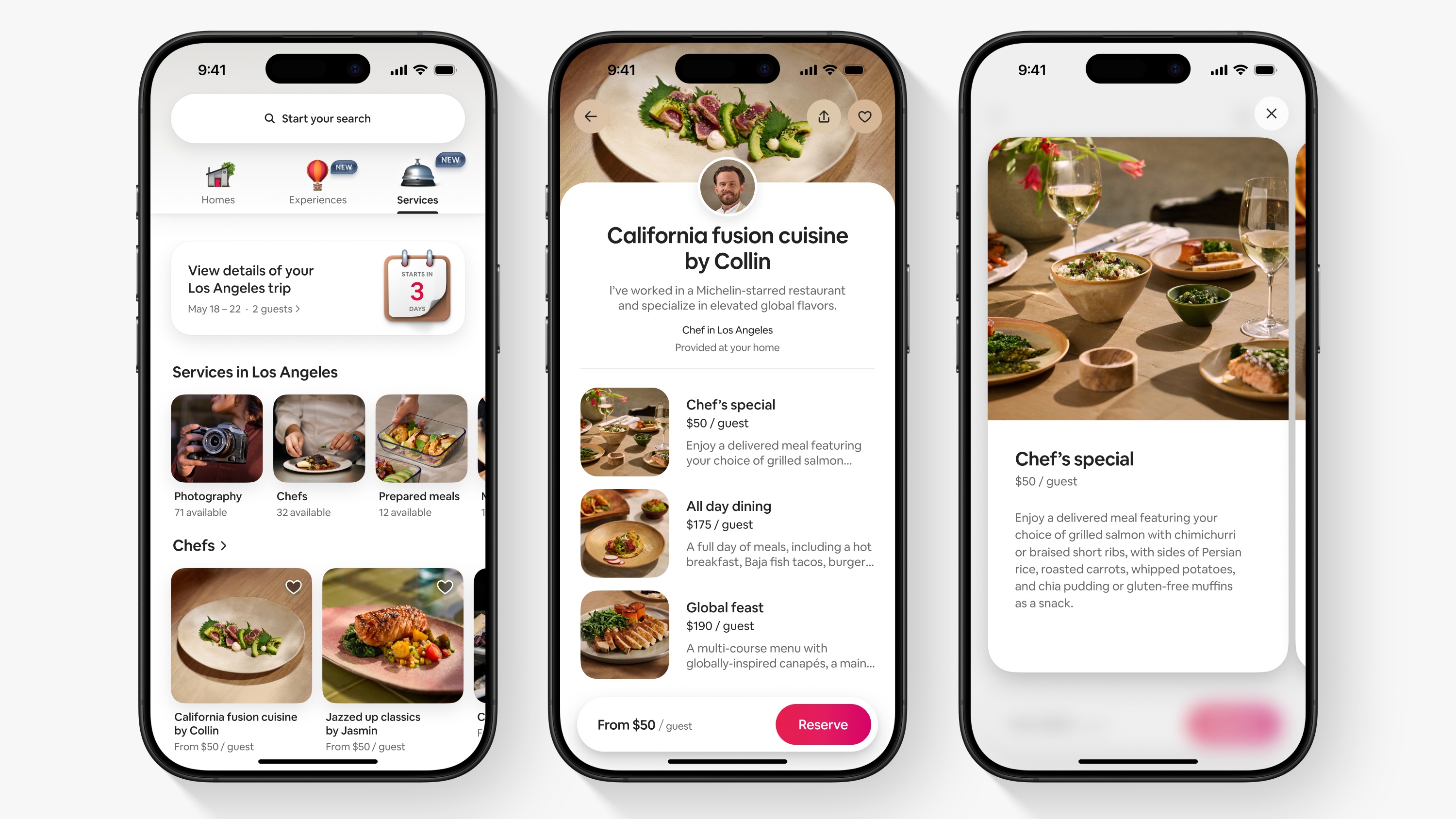
I’m not on vacation, but Airbnb’s latest update makes me want to plan one — here’s why
By Kate Kozuch Published
-
Office Software
-
-

Best PDF editors in 2025 — both free and paid options
By Anthony Spadafora Last updated
-

Hate subscriptions? Microsoft Office 2024 is out now for a one-time fee
By Dave LeClair Published
-

UPDF exclusive deal means you can edit PDFs for less
By Sponsored Published
-

Where to buy Microsoft Office — best deals in March 2023
By Louis Ramirez Last updated
-

How to do a hanging indent in Google Docs
By Andy Sansom Published
-
 Sponsored
SponsoredAll your office apps are in one spot with Microsoft 365 Personal and Family plans
By Sponsored Published
-

How to Insert text box in Google Docs
By Andy Sansom Published
-

How to change margins in Google Docs
By Andy Sansom Published
-

How to do a strikethrough in Google Docs
By Peter Wolinski Published
-
Operating Systems
-
-

Windows 10 dies in October — 3 ways to avoid upgrading to Windows 11
By Alex Wawro Published
-

Fixing your broken Windows 11 PC is about to get even harder — here’s why
By Anthony Spadafora Published
-

Windows parental controls are crashing Chrome — here's the workaround
By Alyse Stanley Published
-
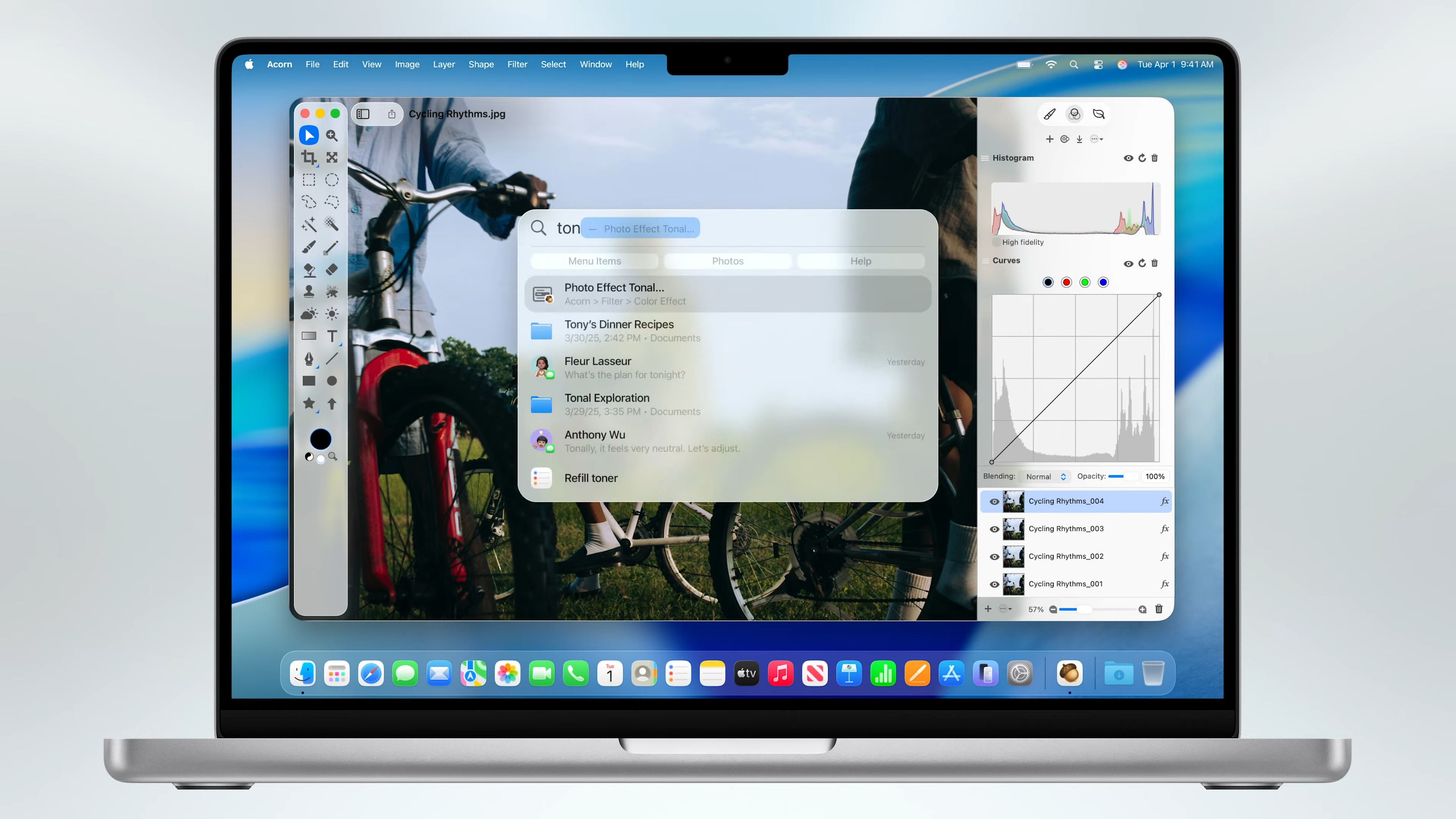
Apple is ripping a page from Microsoft with this macOS Tahoe feature — and I couldn't be happier
By Alex Wawro Published
-

Finally! Steam runs natively on Mac with Apple Silicon — here's how to try it
By Darragh Murphy Published
-

I review MacBooks for a living: 3 macOS Tahoe 26 features I'm most excited about
By Alex Wawro Published
-

Apple is ending support for all Intel-based Macs next year — here's what's getting cut
By Darragh Murphy Published
-

macOS Tahoe 26 is ready to try out — here’s how to download the developer beta
By Alex Wawro Published
-

Apple's stunning 'Liquid Glass' design could change everything — here's what's new
By Dave LeClair Last updated
-
More about Software
-
-
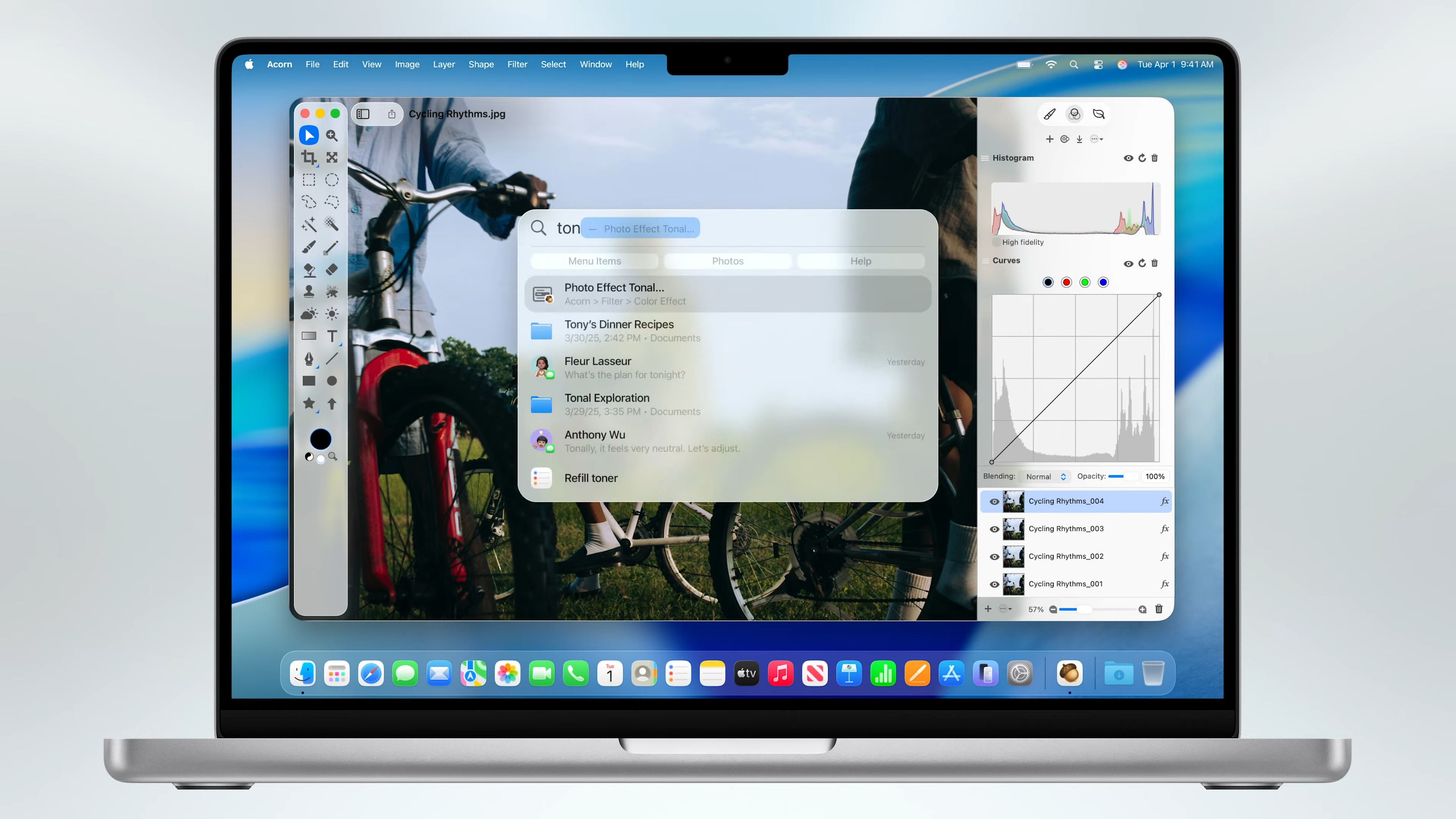
Apple is ripping a page from Microsoft with this macOS Tahoe feature — and I couldn't be happier
By Alex Wawro Published
-

Apple just announced 5 big upgrades to protect your kids online — here's what's coming
By Philip Michaels Published
-

Ads are coming to WhatsApp — here's where you'll see them (and where you won't)
By Lucy Scotting Published
-