Android Phones
Explore Android Phones
Latest about Android Phones

Samsung Galaxy Z Fold 8 may eliminate the display crease too — step aside iPhone Fold
By Tom Pritchard published
Samsung Galaxy Z Fold 8 could try to steal the iPhone Fold's thunder, and launch with a creaseless display ahead of Apple's foldable debut.

Get a free Motorola Razr Fold 2026 at T-Mobile — here's how to get yours
By Louis Ramirez published
Sponsored
Forget Samsung, the Motorola Razr Fold 2026 is our new favorite foldable. Here's how you can get one free at T-Mobile right now.
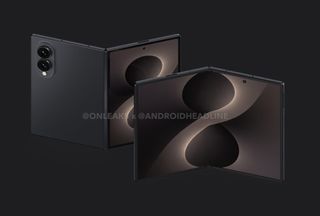
Leaked Galaxy Z Fold 8 Wide dummy unit actually made me excited for Samsung's next foldable
By Scott Younker published
A new leak reveals an alleged dummy unit of the Samsung Galaxy Z Fold 8 Wide that makes me excited for the foldable phone.

Too good to be true! New Motorola Razr Fold with Moto Buds and 4-pack Moto Tags bundle is already $1,485 off
By John Velasco published
Motorola's already giving the Razr Fold a huge discount upwards of $1,485 off with a trade in, but it's also throwing free earbuds and a 4-pack of Moto Tags.

Samsung Galaxy Z Fold 8 could get a weird name change to fight iPhone Fold — and it's a terrible idea
By Tom Pritchard published
Samsung foldables are about to get serious competition with iPhone Fold, and this rumor suggests Samsung may have some sneaky tricks planned to fight back.

Samsung Wallet just matched Apple Wallet and Google Wallet on digital passports
By Tom Pritchard published
You can finally use your Samsung Wallet to bypass airport security with your passport — here's what you need to know.

How to use Galaxy AI to become more organised
By Sponsored published
Sponsor Content Created With Samsung
Use Galaxy AI to stay on top of things

Samsung Galaxy Z Flip 8 — everything we know so far
By Tom Pritchard published
Samsung's next wave of foldables is coming, and this is everything we know about the Galaxy Z Flip 8 so far.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!

 Club Benefits
Club Benefits












