Android Phones
Explore Android Phones
Latest about Android Phones

Even more Android phones now support file-sharing to Apple AirDrop — here's a full list
By Tom Pritchard published
iPhones can now connect to select Android phones, enabling file sharing via Quick Share and AirDrop. Here's a full list of compatible phones.

Certification listing appears to confirm Galaxy Z Fold 8 Ultra as Samsung's third flagship foldable: what we know
By Scott Younker published
Leaked Japanese certifications appear to confirm the Samsung Galaxy Z Fold 8 Ultra name, plus how many models we can expect.

Android just got 'fake call detection' and lots of other upgrades — 7 new features coming to your phone
By Tom Pritchard last updated
Android's June update is rolling out now, and it's set to protect you from scammers, boost your personal fashion, keep your kids safe and more.

Leaked Galaxy S27 Ultra specs reveal a long overdue major upgrade
By Scott Younker published
A series of Samsung Galaxy S27 Ultra leaks reveal some major updates, including one long overdue spec.

Step aside, iPhone Fold — Galaxy Z Fold 8 just spotted in the real world with passport-shaped design
By Tom Pritchard published
Samsung's wide-design Galaxy Z Fold 8 has just been spotted out in the wild, which means the launch could be happening very soon.

This hidden Android feature stops people from snooping around your phone
By Tom Pritchard published
Guest Mode lets someone else use your phone without ever being able to see the rest of your phone. Here's how it works.

Samsung Galaxy Z Fold 8 may eliminate the display crease too — step aside iPhone Fold
By Tom Pritchard published
Samsung Galaxy Z Fold 8 could try to steal the iPhone Fold's thunder, and launch with a creaseless display ahead of Apple's foldable debut.

Get a free Motorola Razr Fold 2026 at T-Mobile — here's how to get yours
By Louis Ramirez published
Sponsored
Forget Samsung, the Motorola Razr Fold 2026 is our new favorite foldable. Here's how you can get one free at T-Mobile right now.
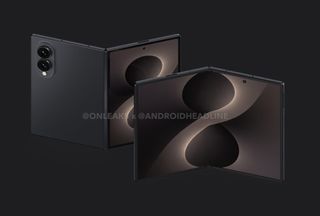
Leaked Galaxy Z Fold 8 Wide dummy unit actually made me excited for Samsung's next foldable
By Scott Younker published
A new leak reveals an alleged dummy unit of the Samsung Galaxy Z Fold 8 Wide that makes me excited for the foldable phone.

Too good to be true! New Motorola Razr Fold with Moto Buds and 4-pack Moto Tags bundle is already $1,485 off
By John Velasco published
Motorola's already giving the Razr Fold a huge discount upwards of $1,485 off with a trade in, but it's also throwing free earbuds and a 4-pack of Moto Tags.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!

 Club Benefits
Club Benefits










