How To Scan an Android Device for Stagefright Vulnerability
A whopping 95 percent of Android devices are at risk of hijack-via-text message from the Stagefright Vulnerability. Here's how to find out if your phone or tablet is still vulnerable.

The Stagefright vulnerability is a flaw in how the Android platform handles multimedia files, and it's found across a wide variety of Android devices. Those devices with the security hole are at risk of hackers hijacking access to their phone by texting a code to the device's telephone number.
While the bug was revealed to the public on July 27, it's likely to still be on your device, unless it's a currently supported Nexus phone or running a custom ROM. That may be because some cellular providers aren't rushing to push Google's patch to users, or because your device is so old that patches are unlikely to be sent. According to Zimperium, the digital security film that discovered the flaw, devices that have been around for longer than 18 months are simply unlikely to get any patches at all.
MORE: Mobile Security Guide: Everything You Need to Know
For those who are worried their phones are still exposed, security firm Zimperium has released a Stagefright Detector App to the Google Play Store.
How To Scan an Android Device for The Stagefright Vulnerability
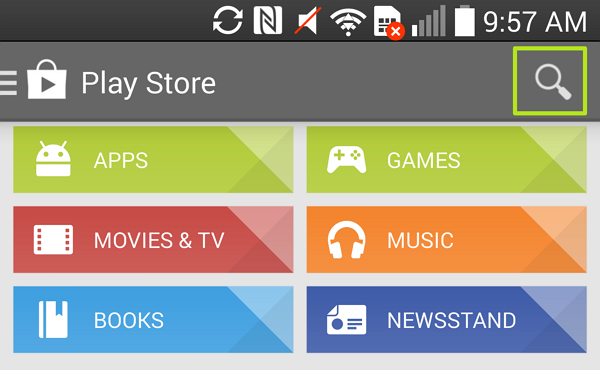
1. Open the Play Store app, and select the Search icon in the upper-right corner.
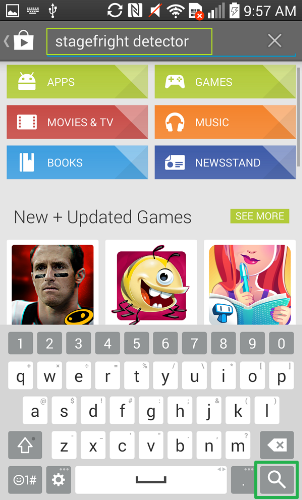
2. Type "stagefright detector" into the search field, and tap the Search icon in the bottom right corner.
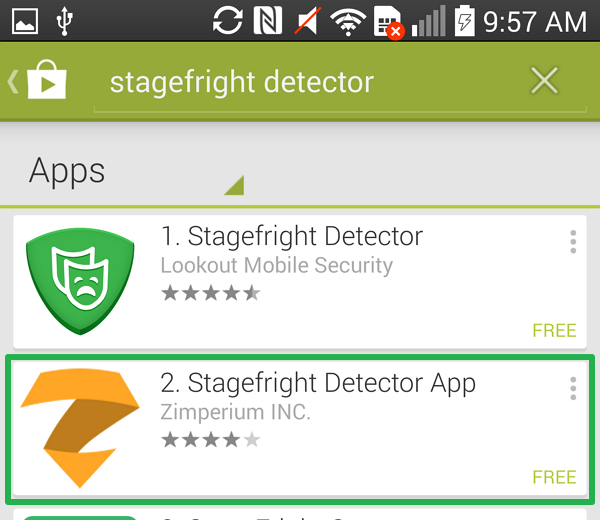
3. Select "Stagefright Detector App" by Zimperium INC.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
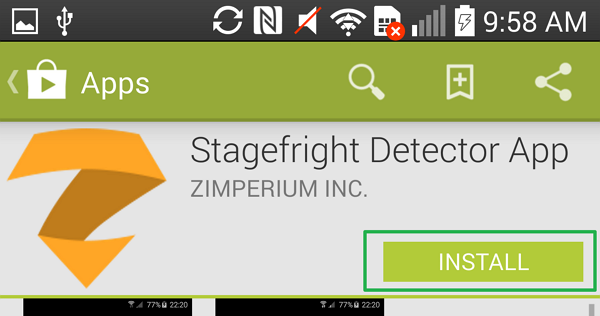
4. Tap the Install button.
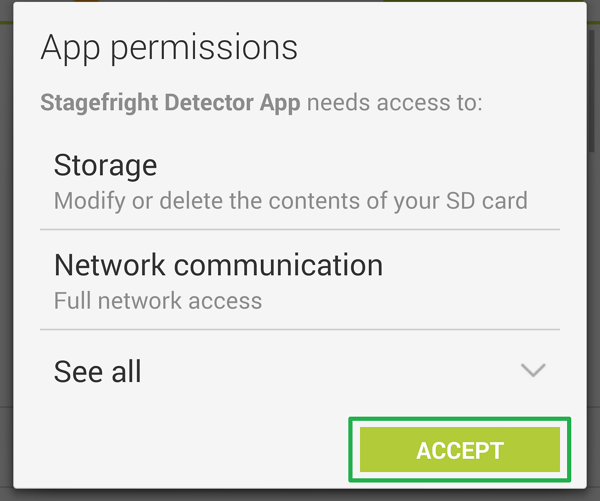
5. Tap the Accept button.
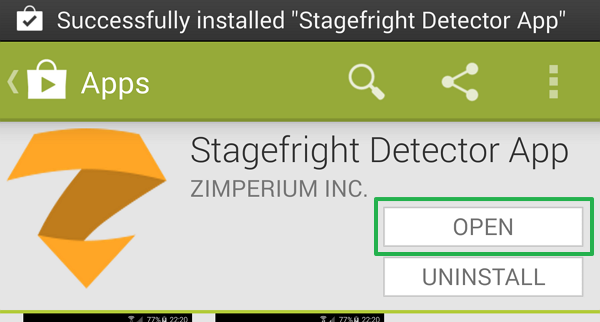
6. Once the app has installed, select Open.
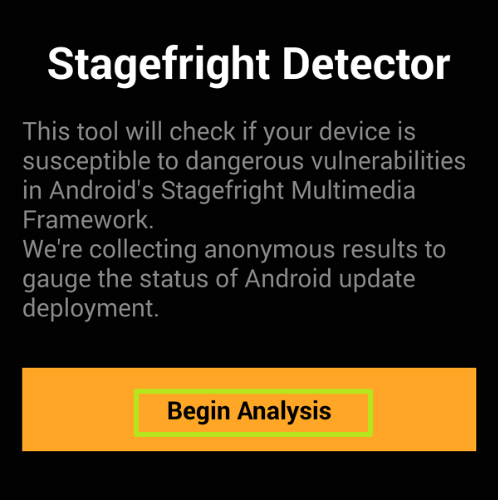
7. Tap "Begin Analysis."
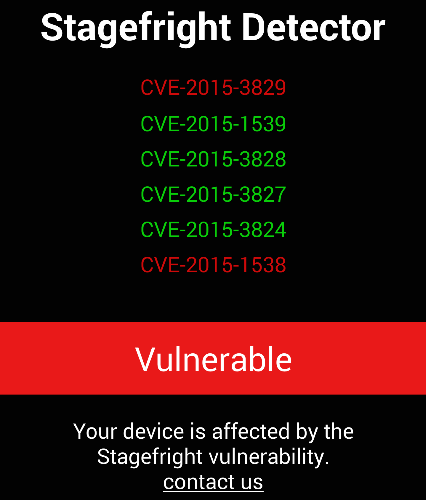
Now you know if you have a vulnerable phone, like the LG G3 we used to run the app. While knowing is half the battle, users who are vulnerable should install all available system updates from their cellular service provider. If that still doesn't work, contact your provider's customer support to demand that Google's patch be pushed down.
- 10 Worst Data Breaches of All Time
- Best Antivirus Protection for PC, Mac and Android
- Your Router's Security Stinks: Here's How to Fix It
Henry T. Casey is a staff writer at Tom’s Guide covering security and music. In his personal time, you can find him at local concerts or tinkering with his cold-brew coffee method. Follow him at @henrytcasey.

Henry was a managing editor at Tom’s Guide covering streaming media, laptops and all things Apple, reviewing devices and services for the past seven years. Prior to joining Tom's Guide, he reviewed software and hardware for TechRadar Pro, and interviewed artists for Patek Philippe International Magazine. He's also covered the wild world of professional wrestling for Cageside Seats, interviewing athletes and other industry veterans.

 Club Benefits
Club Benefits











