Apple's new Android app sniffs out AirTag stalkers
Non-iPhone users finally can detect rogue AirTags

Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
Congratulations, Android users: You've finally got a way to detect rogue Apple AirTags.
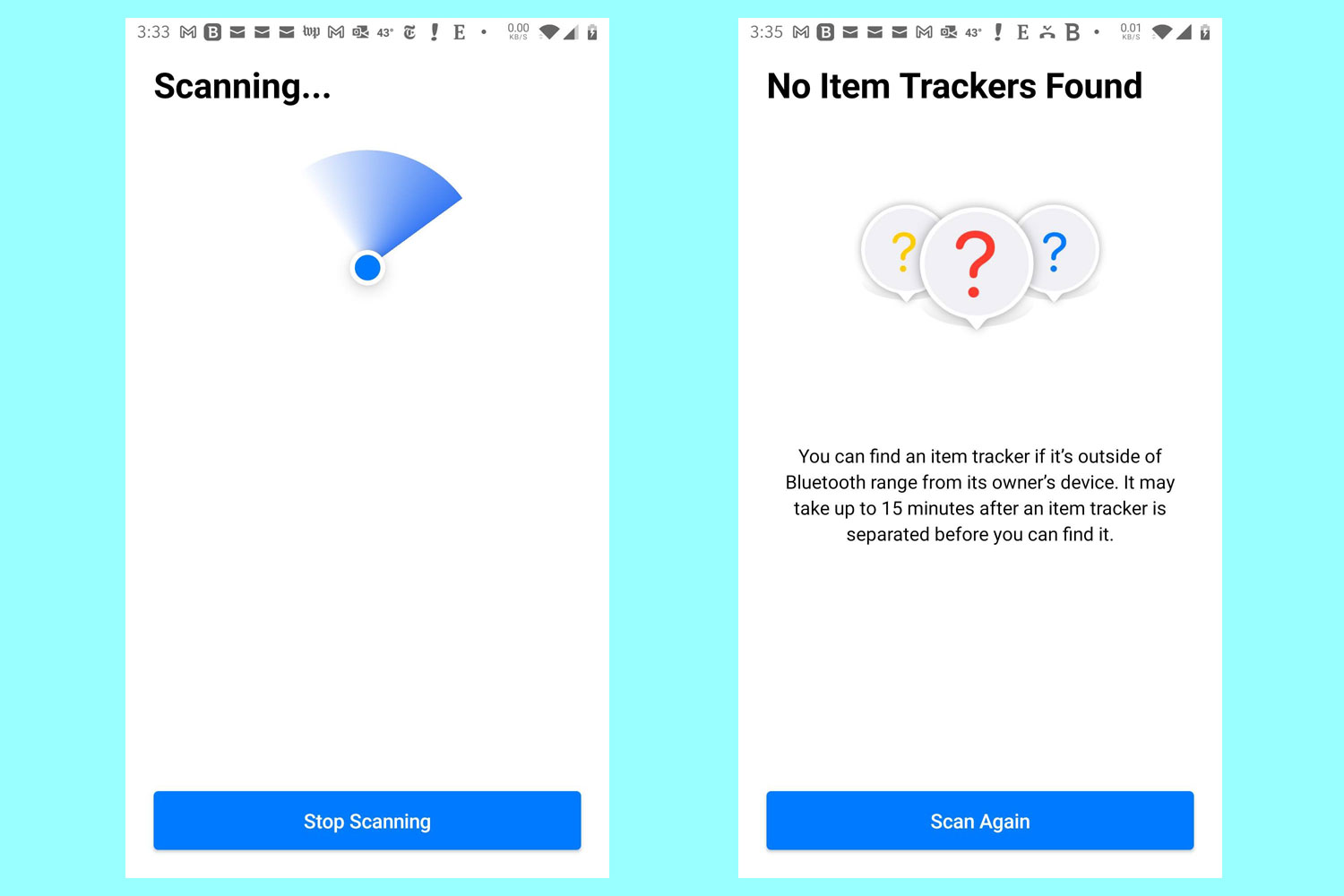
Apple this weekend released Tracker Detect, an Android app that lets you scan your general vicinity for AirTags that may have been separated from their owners. If you do detect one, the app waits 10 minutes, then lets you force the AirTag to make a sound so that you can find exactly where it is — and disable it by removing the battery.
Apple is doing this because it turns out there's a downside to having tiny devices that cost $25-$30 apiece and can be tracked almost anywhere in the world. AirTags can be used to stalk unsuspecting people or even, as car owners in the Toronto area have discovered, to track desirable vehicles back to their owners' driveways for overnight theft. (Even more possible AirTag stalking incidents were reported in late December and early January.)
Article continues belowTracker Detect doesn't do that much. Unlike the AirTag software for iPhones, it doesn't detect and alert you of the presence of a rogue AirTag all by itself. Instead, you have to start a scan manually and give the Tracker Detect app permissions to use your phone's Bluetooth and GPS connections.
(A different Android app called AirGuard, created by German researchers and recommended by women concerned about AirTag-based stalking, does scan automatically.)
Under ideal circumstances, AirTags stay close to the iPhones that they're paired with, such as on a person's keychain or a dog's collar. Having AirTags separated from their paired iPhones for long periods of time is unusual, so Apple makes sure that such "lost" AirTags start audibly chirping between eight and 24 hours after their last contact with their paired iPhones.
(However, you can now buy AirTags with their speakers removed so they don't make any sound, and there are YouTube videos showing you how to disable the speaker.)
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
However, some wayward AirTags are not lost at all. Apple can tell when an AirTag mimics the movements of an iPhone belonging to a completely different person. It might have been slipped into a handbag or a jacket pocket by accident, or deliberately.
It's a red flag for stalking, and since the "lost" AirTag's chirps might not be heard if the AirTag is buried in a bag or in a coat closet, the person being tracked might not find out about it.
To combat this, Apple iPhones running the latest versions of iOS will tell their owners that an unknown AirTag has been traveling with them when the iPhone owners arrive home. Those people can use their iPhones to find the rogue AirTag and disable it.
(In February 2022, Apple said it would make the chirps more audible, sync them with notifications sent to iPhones and let iPhone owners use Precision Finding to locate rogue AirTags.)
The fact that no corresponding Android version of this existed put Android users at a bit of a disadvantage — until now.
Again, the Android version of this doesn't start scanning automatically. It's really quite primitive compared to the iOS app, and naturally it doesn't tell you if it detects AirTags that belong to you and may be paired to an iPad or iPhone of your own. That would kind of undermine the whole point of AirTags as a selling point for iOS devices.
We tried out Tracker Detect and found that it seems to work quite well, although we didn't find any rogue AirTags in the sparsely populated Tom's Guide offices. (We did encounter the longest license agreement we've ever seen for an Android app.)
So if you have an Android phone and you're worried about being stalked, or you have a car and live in Ontario, install the app and run it every day or two. It can't hurt, but we're still waiting to see how effective the app is.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits










