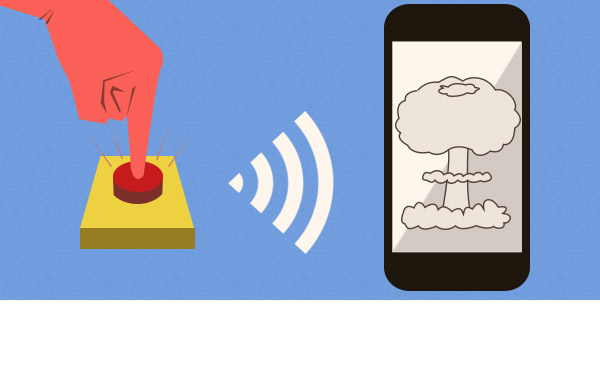
Smartphone Kill Switch: What It Is, How It Might Work
A smartphone kill switch promises to protect your smartphone if it's lost or stolen. Here’s everything you need to know.

In the past few months, politicians and law enforcement officials have demanded a smartphone "kill switch," a security feature designed to discourage theft by disabling stolen handsets. Both California and Minnesota have kill-switch bills that are close to becoming law, while Congress is considering national legislation.
At the same time, the cellphone industry has countered with its own proposal, and security experts have questioned whether a kill switch would work at all.
Unfortunately, no one seems to be quite sure exactly what a smartphone kill switch should be, or how it would work. Here's what you need to know.
What is a kill switch?
In most forms of technology, a "kill switch" is a single command or button that can shut down a complicated system almost immediately. On a smartphone, that's the "power off" command.
MORE: Best Android Security Apps
A simple power-off switch is a bit different from what the two public figures leading the smartphone-kill-switch crusade, New York State Attorney General Eric Schneiderman and San Francisco District Attorney George Gascón, originally demanded in 2013. But even their definition is different from what most politicians are asking for a year later.
What kind of kill switch do politicians want on smartphones?
There are really two different kinds of proposed kill switches for smartphones — a "hard" kill switch that permanently "bricks" a phone, and a "soft" alternative that makes a phone unusable to all but the legitimate owner.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
When Gascón and Schneiderman launched an initiative called Secure Our Smartphones in June 2013, they demanded that smartphone makers build in a "hard" kill switch, a feature that would render a stolen device permanently and completely useless — to give it "the value of a paperweight," according to the Secure Our Smartphones mission statement.
"The implementation of a 'kill switch' would render stolen devices inoperable on any network, anywhere in the world," read the mission statement. "Such a feature would disable the device even if it is turned off or the SIM card has been removed."
The current California Senate bill, SB 962, the Minnesota bill, HF 1952, and the federal bill, the Smartphone Theft Prevention Act, ask for less severe, reversible, "soft" kill switches. In other words, the newer proposals wouldn't really kill the phone.
The California bill, for example, requires that the kill switch "render inoperable" a device "to an unauthorized user," and that the feature survive a "hard reset" and be able to "prevent reactivation of the device on a wireless network except by the rightful owner or his or her authorized designee."
There are some differences among the "soft" bills. The California bill specifies that the kill switch should be enabled by default on phones, but adds that users can opt out of it. (A spokesman for Gascón said the San Francisco D.A. supported that implementation.) The federal bill states only that the feature should be "made available." The Minnesota bill says smartphones should be “equipped” with the feature. All specify that the kill switch should be free for consumers.
Why might we need a smartphone kill switch?
Its proponents believe that a smartphone kill switch would be a magic-bullet solution to the skyrocketing rate of smartphone theft. The theory is that the kill switch will kill the incentive for smartphone theft by making sure that stolen devices can no longer be factory reset or resold — anywhere in the world.
MORE: 10 Best Apps for Finding Lost Smartphones
In 2013, 3.1 million Americans had a smartphone stolen, nearly twice as many as in 2012, according to a Consumer Reports survey. Forty-five percent of those 2013 victims never recovered their stolen devices. Based on 2012 data, the FCC estimates one in three robberies involves a mobile device (including iPads stolen in home burglaries).
A separate study, conducted by IDG Research on behalf of Lookout Mobile Security, found a longer-term loss rate of 68 percent on stolen devices in the United States, United Kingdom, France and Germany. It also found roughly equal numbers of stolen Apple and Android devices. Forty-four percent of thefts were due to absent-minded owners leaving devices in public places.
A stolen smartphone is easy to pick up off a cafe table, or snatch out of a user's hand, and can be resold for up to $600 domestically and more than $1,000 overseas. Most stolen phones are quickly "factory reset" to erase the previous user's data, then resold. (There's also a wealth of personal data on almost every smartphone, but thieves don’t seem to be as interested in that.)
Demands for a kill switch got louder in mid-2013 when it became clear that an earlier anti-theft measure had failed. A year earlier, the four major U.S. wireless carriers (AT&T Mobility, Sprint, T-Mobile and Verizon Wireless), had begun to implement a comprehensive stolen-phone blacklist.
The blacklist was meant to ensure that any phone reported stolen would no longer be able to receive regular cellular service within the United States. But thieves can change a stolen phone's wireless ID so that it won't be recognized as a stolen device, or can ship it overseas where the blacklist has no bite.
There's some precedent for a kill-switch deterrent: Theft of car stereos is now half what it was in the early 1990s, according to the FBI. That's partly because many factory-installed car stereos now require an activation code to operate if they're disconnected from the car battery. (It's also because factory-installed car stereos got much better, and fewer car owners replace them with aftermarket models that are easier to steal and resell.)
How would a smartphone kill switch work?
It's not clear how a smartphone kill switch would work. None of the political proposals specify whether the "kill switch" should consist of hardware, software or both, or how a theoretical "kill" command could be transmitted to a stolen device.
MORE: 7 Ways to Stop NSA Spying on Your Phone
Instead, the proposals leave the technical details up to experts. As the federal bill states, "the mobile device industry, law enforcement, and consumer advocates are best suited to proactively develop solutions to protect consumers, drive innovation, and deter theft."
What's wrong with a smartphone kill switch?
It depends which kind of kill switch you're talking about.
The "hard" solution demanded by Gascón and Schneiderman has some major problems. It's not clear if it would even work. Only physical damage will permanently disable a smartphone; otherwise, a new operating system or new firmware could probably be installed.
Even if some way were found to remotely fry a phone's circuits, the kill switch might have to be activated by a wireless signal. That leads back to the problem with the current stolen-phone blacklist: If a phone were turned off or put into airplane mode immediately after being stolen, it might never receive the kill signal.
Furthermore, hackers or pranksters might figure out ways to hijack a hard kill signal or even generate their own kill signal, creating much opportunity for mayhem.
"Everything could go wrong, but little right," Chet Wisniewski, a security analyst for British anti-virus maker Sophos, told Tom's Guide. "Next thing you know, police will want carmakers to put kill switches in every vehicle. Totally unnecessary."
The "soft" legislative bills in play today have fewer technical issues. But since all of them demand that the kill switch be reversible if the legitimate user recovers the phone, it means the phone isn't really dead, and that thieves may figure out how to reverse the kill switch themselves.
CTIA The Wireless Association, the lobbying arm of the cellphone industry, argues that most kill-switch proposals violate an FCC regulation that requires every mobile phone to be able to call 911, no matter who's using it. (We've inquired with the FCC whether that's true and will update this article once we find out.)
How would a smartphone kill switch be different from existing smartphone security solutions?
Widely available existing security solutions, such as Apple's Find My iPhone, Google's Android Device Manager, Microsoft's Find My Phone or various Android third-party apps, are excellent at locating, locking and wiping stolen smartphones that stay connected to cellular or Wi-Fi networks. But for the most part, they can't do anything if a phone is turned off or put into Airplane Mode immediately after being stolen.
MORE: How to Enable Android Device Manager Security
Arguably, the personal data on a phone — with its ability to automatically log into the owner's email and social-media accounts — is worth more than the phone itself. It might be best for the aggrieved owner to just remotely wipe the handset, write it off as lost and get a new phone. But that benefits both the thief and the phone's wireless carrier, and potentially leaves the owner paying the bills.
What about Apple's Activation Lock or Samsung's Reactivation Lock?
Apple's Activation Lock or Samsung's Reactivation Lock are basically what the California and federal bills ask for.
Activation Lock, introduced with the release of Apple's iOS 7 in September 2013, adds an optional feature to Find My iPhone that ties a device to the owner's Apple account. If Activation Lock is enabled, a stolen phone cannot be reactivated after a factory reset without the owner's Apple ID and password.
Apple has an advantage over other smartphone makers in that every Apple device in factory-fresh condition must contact Apple servers, either via cellular data connections or over Wi-Fi, in order to be activated. That's not the case with most Android devices, which have no mothership to phone home to.
Samsung got around that problem by creating its own mothership. To use Reactivation Lock, first made available on the Galaxy Note 3 in September 2013 and now also available on the Galaxy S5, the user sets up an account directly with Samsung, not the device's wireless carrier.
MORE: How to Set Up Find My iPhone Activation Lock in iOS 7
The Samsung phones will demand the user's password to reactivate the phone after a factory reset, and, depending on the implementation, to begin a factory reset in the first place. Samsung had to push out a patch for the Galaxy Note 3 switching the default setting for Reactivation Lock from "on" to "off" -- many users, unaware of the feature, had found themselves locked out of their devices.
Reactivation Lock works because the Galaxy S5 and Note 3 have a special "secured memory storage area" in which the activation "flag" is stored, and which is immune to a factory reset. Other Android phones would have to have similar hardware features built in.
Why don't more phones have such kill-switch-like features?
Some prominent officials say solutions similar to Apple's Activation Lock and Samsung's Reactivation Lock aren't available on all smartphones because of obstructionism by the cellular carriers and, to a lesser degree, the smartphone makers.
"I seek to understand why companies that can develop sophisticated handheld electronics ... cannot also create technology to render stolen devices inoperable," New York State Attorney General Eric Schneiderman wrote in official letters sent in May 2013 to Apple, Google, Microsoft and Samsung.
New York State Comptroller Thomas DiNapoli, in charge of the state's pension funds, wrote to the same four companies in June 2013 and hinted that the state might sell the $3 billion of the companies' shares it held if cooperation was not forthcoming.
Schneiderman and DiNapoli may not have been aware that at the time of their letters, Apple and Samsung were already developing Activation Lock and Reactivation Lock.
In November 2013, San Francisco District Attorney George Gascón said he'd seen leaked emails in which a Samsung executive privately complained that the big four U.S. cellular carriers refused to implement an earlier Samsung-developed anti-theft solution because it would reduce the revenue the carriers generated from smartphone insurance premiums.
"Corporate profits cannot be allowed to guide decisions that have life-or-death consequences," Gascón told The New York Times. "These emails suggest the carriers rejected [Samsung's anti-theft solution] so they can continue to make money hand over fist on insurance premiums."
However, Gascón never produced evidence of those emails.
What does the cellphone industry propose?
In April 2014, CTIA The Wireless Association unveiled a counter-proposal called the "Smartphone Anti-Theft Voluntary Commitment." It invited device and smartphone operating-system makers to agree to "offer, at no cost to consumers, a baseline anti-theft tool that is preloaded or downloadable on wireless smartphones."
Many media outlets, including this one, took the proposal to mean that the smartphone makers and wireless carriers had thrown their support behind a kill switch. (The CTIA press release announcing the proposal used "kill switch" only in quotations from politicians, and the phrase never appears in the proposal itself.)
The proposal's voluntary participants are a who's who of the U.S. wireless industry: Apple, the insurance provider Asurion, AT&T, Google, HTC, Huawei, LG, Motorola Mobility, Microsoft, Nokia, Samsung, Sprint, T-Mobile, U.S. Cellular and Verizon Wireless.
However, close reading of the CTIA proposal revealed that it simply commits to the status quo. The features to be "offered" by its voluntary signatories — remote lock and wipe — are already part of Find My iPhone, Android Device Manager and Find My Phone, which are built into all Apple, Android and Windows Phone 8 devices, respectively.
The CTIA proposal states that the its requirements will "render the smartphone inoperable to an unauthorized user" and "prevent reactivation without authorized user's permission," but then throws in the caveat that this should be done "to the extent technologically feasible" and offers as an example "locking the smartphone so it cannot be used without a password or PIN."
In other words, the user's regular PIN or passcode lock is all that’s required to protect the phone from factory-reset attempts. That clearly doesn't work even today -- almost every smartphone model can be factory-reset without a PIN by putting it into “recovery mode.”
What happens next?
The California kill-switch bill is heading to the state Assembly. If it passes there without substantial changes, and Gov. Jerry Brown then signs it, it will mandate that a "soft" kill switch be enabled on all smartphones sold in the state after July 1, 2015. Because roughly one-eighth of all Americans live in California, and Apple and Google are based there, a California law might very well have a national effect.
Minnesota’s law would go into effect on the same date as the California one, but the state House and Senate kill-switch bills, which have both passed, differ and need to be reconciled before going to Gov. Mark Dayton.
The political wrangling over the California bill may have created a split in CTIA ranks. Apple and Microsoft, both members of the association and both signatories to the Smartphone Anti-Theft Voluntary Commitment, dropped their opposition to the California bill after it was amended to exempt tablets and extend the compliance deadline by six months.
CTIA itself continues to oppose the California bill, stating after its passage by the state Senate that if "technology mandates are imposed on a state-by-state basis, the uniformity [of anti-theft solutions] is threatened."
On the federal level, neither the Senate nor House bills have yet to be recommended by their overseeing committees for a full floor vote. Another Senate bill, which would make it a federal crime to tamper with a phone's wireless ID, is also stuck in committee.
But whether the legislative solutions succeed or die, technology may pass them by. By the time the California law would take effect 14 months from now, all Apple and most Samsung smartphones sold in the United States will have an optional "soft" kill switch built in.
If those voluntary kill switches contribute to a sharp dropoff in smartphone theft, consumers will demand their inclusion on all smartphones. Opponents of a smartphone kill switch will continue to lobby against it, but they may have to yield to the unavoidable force of popular demand.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.
-
gm0n3y Having a way to brick your phone if it is stolen would be great, but seems technologically unlikely to happen. Short of physically breaking the device (which would be extremely difficult), any software attempts will be thwarted by criminals. Of course just making it more difficult may be enough to put off common criminals from stealing cell phones.Reply
I'm actually surprised by the 3 million phones stolen statistic. I can't think of anyone I know having their phone stolen. -
Jerky_san "Why do you need a kill switch?" - So when a large protest starts happening in this country they can kill everyone's cellphone stopping the spread of information.. Look what happened at the Bart station in california..Reply -
BMAuEagle I think this is a waste of time and resources. It's crazy to force companies to make a product that is ultimately the individual's responsibility a certain way to prevent it from being stolen with legislation. It's nice have it on Apple and Samsung products, but those are premium products. The added security is a feature of the premium product that people pay for. If you are worried about your phone being stolen, then be aware that you are holding a device in the palm of your hand that is worth 100's of dollars to someone out there who will take it if the opportunity arises. Else, buy a cheap phone that nobody will think twice about stealing.Reply -
derekullo Let's say the smartphone companies came up with a way to hard kill a phone. It would have to either be sent through the cellular tower or wifi. Both of which are well known vectors of attack.Reply
What happens when a hacker gets a hold of said technology and starts a phone bricking party? -
none12345 Actually a hardware kill switch is really easy. All they have to do is over current a chip, or section of a chip and fry it out. Its easy to add that in if they want. Its not like you can repair 1 fused transistor among billions of others in a processor.Reply
They shouldn't ever do this tho. If they can fuse hardware remotely. Hackers WILL find a way to do it, and there WILL be millions of bricked phones. Guaranteed to happen. Can you imagine the chaos frying 50 million phones on one day would cause? You can bet there will be thousands of people trying to do it, for that badge of honor(or shame, however you want to look at it); and they will most certainly succeed.
If you want a conspiracy theorist viewpoint. What happens when the government decides to turn off all phones for whatever reason. Sure, it probably wont ever happen. But that is FAR too much power to have.
Or the far more likely. What happens when they accidentally fry your phone instead of someone else's because they typed in the serial number wrong. Oops too bad, we killed all your data, so sorry, have a nice day.
-----------
Even the soft kill switch is an extremely bad idea. Its too much power to have the ability to turn off every phone at will. Sure sure, its not going to happen, untill it does.
Even with a soft kill switch, think of how long it woudl take to reauthorize 300 million phones, if someone decided to kill them all for fun. -
dro2 Hence why I switched Apple products. Apple dictates to the cellular carriers unlike Samsung who simply says yes masta yes masta.Reply -
thxext I think there is less care about theft then the number of individuals that have been attacked so their phone can be taken from them. No phone is worth your life or harm. Unfortunately, I don't think this is the solution. I am not expert, but it would seem a hard-coded S/N and some sort of black list may work better.Reply -
cats_Paw Another reason not to have a smartphone at all (now maybe they say its for your own good, but lets see how they would actually use the technology... I still remmber when Paul Denton got his kill switch activated).Reply -
Akizu ReplyI think there is less care about theft then the number of individuals that have been attacked so their phone can be taken from them. No phone is worth your life or harm. Unfortunately, I don't think this is the solution. I am not expert, but it would seem a hard-coded S/N and some sort of black list may work better.
Phones already have IMEI numbers... All that is needed is ensuring that its impossible to change that number and making phones report that number to the network while connecting to it. Then network providers would just need to make a black list, so if you would report a phone as stolen it would get blacklisted by all operators. If a stolen phone would have to be shipped to different country to work that would make phone theft way less profitable and an international blacklist would make such phones worthless. If such system would be implemented on all new phones then within 2~3 years (when all models that don't support this would go down in price) phone theft would go down considerably. (as long as it would be impossible to change IMEI or make phone report itself to the network as some older model)

 Club Benefits
Club Benefits











