News
Explore News
Latest News
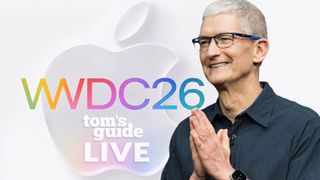
Apple WWDC 2026 Live: New Siri, iOS 27, Apple Intelligence and all the last-minute rumors
By Mark Spoonauer, John Velasco last updated
WWDC 2026 is going to introduce Apple's latest software developments, including Apple Intelligence and a new Siri that will be taking charge.

How to watch F1 2026 live online — Formula 1 streams, schedule, Barcelona-Catalunya Grand Prix
By Adam Marshall last updated
See how to watch F1 2026 live streams for free and from anywhere with information on international broadcasters and this season's Formula 1 schedule.

How to watch 'Gareth Southgate: Changing the Game for Young Men' online — it's *FREE*
By Krishi Chowdhary published
Here’s how to watch BBC documentary 'Gareth Southgate: Changing the Game for Young Men' for FREE from anywhere in the world.

5 top new shows to stream this week on Netflix, Prime Video and more (June 8-14)
By Kelly Woo published
This week’s new TV lineup is packed with drama, thrills and laughs that you can stream, including "Sweet Magnolias" season 5, "Every Year After" and "The Listeners."

Today's NYT Strands hints and answer: solutions to game #827, June 8
By Alan Martin last updated
We help you find today's Strands answers with some useful hints and tips to win.

Today’s Wordle hints and answer: June 8, 2026, solution #1,815
By Alan Martin last updated
Find out what today's Wordle hint and answer is and get some tips for it, plus see the solutions to previous games.

How to watch French Open 2026: Live Streams & TV Channels
By Dan Struthers last updated
All the ways to watch 2026 French Open live streams online and from anywhere, as Jannik Sinner and Aryna Sabalenka are top seeds for Roland-Garros.

NYT Pips today hints and answers: Monday, June 8
By Scott Younker last updated
Get clues and answers for today's NYT Pips to keep your streak going.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!

 Club Benefits
Club Benefits












