Another Day, Three More D-Link Router Vulnerabilities
Three more flaws have been disclosed in D-Link home wireless routers. One is already patched, but the other two are still very much a risk.

It’s been a bad year to own a D-Link router. A few days after a Korean researcher revealed 10 catastrophic vulnerabilities in a single popular D-Link router model, a separate security firm has unearthed three more flaws in three more models, and even provided proof-of-concept exploits.
The similarities run even deeper, as both entities contacted D-Link before going public, but decided that the company was not able to fix router flaws on a user-friendly timescale. D-Link has already patched one of the newfound flaws, but the other two are still very much a risk, and the only surefire way to protect yourself is to use a different router.
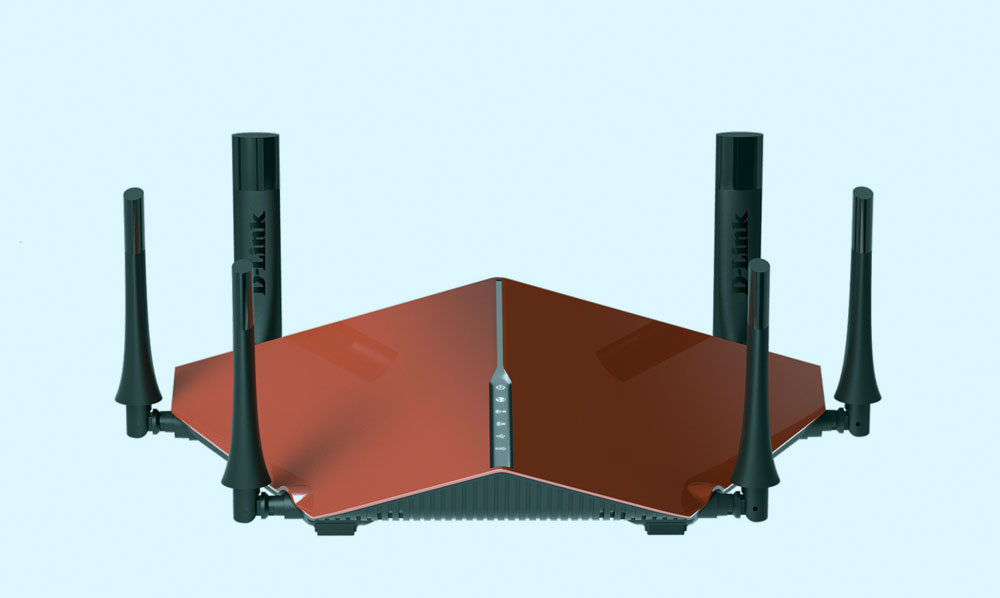
The new report comes from Embedi, a Berkeley, California-based security firm that focuses on hardware protection. Researchers at the company discovered three exploitable flaws in D-Link’s DIR-890L, DIR-885L and DIR-895L routers, but believe that other models in the DIR-8XX line are probably also "cruising for a bruising." (The separate flaw we wrote about yesterday involved the DIR-850L model.)
MORE: Best Wi-Fi Routers
First things first: Updating your D-Link router to the latest firmware will solve one problem that Embedi found. (If you’re not sure how to do this, visit the D-Link tech support site and search for your router model.)
Embedi discovered a flaw in the routers’ phpcgi protocol, which — in extremely simple terms — processes authorization requests for the router. By sending a cleverly programmed (but inauthentic) request, researchers were able to suss out a router’s username and password.
However, even though Embedi notified D-Link about the routers’ other problems three months ago, two of the flaws remain unpatched. One of them involves a stack overflow error, which basically just floods the system with nonsense data until it does what the attackers want it to do.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
The other flaw — ironically — lets an attacker hijack a router by trying to update firmware in a router’s recovery mode. So maybe it’s not worth updating your firmware just yet.
Since a router controls an entire home network’s internet traffic, it doesn’t take much imagination to expostulate what a hacker could do with these flaws. Intercepting internet traffic — including logins for email, social media and financial institutions — would be simple, as would redirecting queries for popular websites to malicious pages that could steal credentials or inject malware.
Embedi may not have helped matters, as it posted working exploits for each flaw on its Github page.
Tom’s Guide has contacted D-Link for comment on the story, but has not yet received a response.
For now, if you use a D-Link router but have a spare stashed away somewhere, it’s probably better to use your backup. Netgear and Linksys routers aren’t perfect, but they at least have a pretty good track record of patching their flaws in a timely manner.

Marshall Honorof was a senior editor for Tom's Guide, overseeing the site's coverage of gaming hardware and software. He comes from a science writing background, having studied paleomammalogy, biological anthropology, and the history of science and technology. After hours, you can find him practicing taekwondo or doing deep dives on classic sci-fi.

 Club Benefits
Club Benefits











