Scary 'BootHole' flaw puts Windows, Linux PCs at risk: What to do
UPDATED with reports of issues with patches rendering systems unbootable.
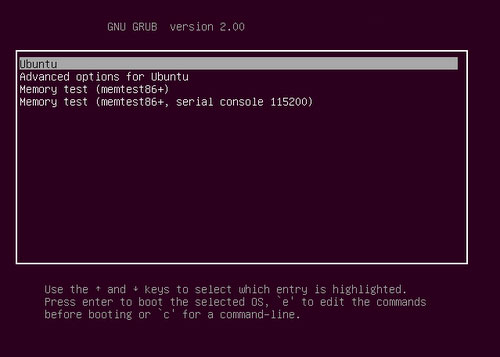
Anyone who's ever used Linux is probably familiar with the Grand Unified Bootloader, or GRUB, a simple program that loads immediately after you power up and lets you choose which operating system installed on a computer you can boot into.
GRUB has been around for ages, but a serious security flaw has been discovered in its latest iteration (GRUB2). The flaw, dubbed "BootHole," could let an attacker completely bypass the Secure Boot protections built into modern PCs and servers, permitting the installation of malware that would be nearly impossible to detect.
- The best antivirus software to detect everything above the disk level
- Best VPNs for Linux
- Latest: 386 million stolen user records being given away for free
If you've got a "dual-boot" (or triple-boot) machine set up to use either Windows or Linux, or even a machine set up to just use Linux, then you need to update your Linux distribution as soon as you can. Ditto if you're one of the (probably few) Mac users who has GRUB installed.
The well-known Linux distros Ubuntu, Debian, Red Hat and SUSE have patches available already. On its end, Microsoft is working on a patch for its Unified Extensible Firmware Interface (UEFI) that will be included in a future Windows Update bundle.
UPDATE: Or maybe you should hold off on those GRUB updates. Multiple users of Debian- and Red Hat-based Linux distributions, including Ubuntu, Fedora and CentOS, are reporting that applying the patch leaves their systems unable to boot. It might be best for now to strictly limit physical access to your Linux systems and to make sure remote access is locked down.
Pain in the BootHole
BootHole has been given a disarmingly cute logo by its discoverers at Portland, Oregon security firm Eclypsium, but fortunately the flaw can't always be carried out.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
The attacker would need to have administrative rights on a Windows or Linux PC to begin with, which in itself opens up many others avenues of attack. And despite the worm in the BootHole logo, it's pretty unlikely that malware exploiting this flaw could spread from one machine to another.
But because BootHole affects a disk-level program that runs before any operating system even loads, a successful exploit could make changes so deep and fundamental that the best antivirus software or other tampering-detection methods wouldn't be able to spot them.
We won't get into the details, except to say that exploiting BootHole involves editing the GRUB configuration file to trigger a buffer overflow and install rootkit malware. That kind of hack is so old it ought to be played on Classic Rock stations, but it achieves exactly what Secure Boot was designed to prevent.
Is my PC vulnerable to BootHole?
Most PCs set up to "dual boot" between Linux and Windows will have GRUB installed as the bootloader, as do many machines with only Linux on them. You could also set up GRUB to boot between different versions of Windows, but most people would probably just run one version of Windows in an emulator.
Macs can use GRUB as well, but because it can be a bit tricky to use due to Apple's unique disk formatting and there are easier, better methods available, it's rarely used on dual-booting (or triple-booting) Macs.
There's also the chance that an attacker with administrative rights to a PC could install GRUB on an otherwise GRUB-free machine without the primary user's knowledge and then use GRUB to exploit the BootHole flaw. Whether or not GRUB is installed, a PC will technically be vulnerable until Microsoft updates the UEFI.
If you're a bit of a Windows jockey, you can check to see whether your PC is vulnerable by running this text string in PowerShell with Administrator privileges:
[System.Text.Encoding]::ASCII.GetString((Get-SecureBootUEFI db).bytes) -match 'Microsoft Corporation UEFI CA 2011'If you get a return of "True," then your PC is vulnerable. Update your Linux distro if you have one installed on the machine. If not, then don't install Linux until Microsoft updates the UEFI.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.
