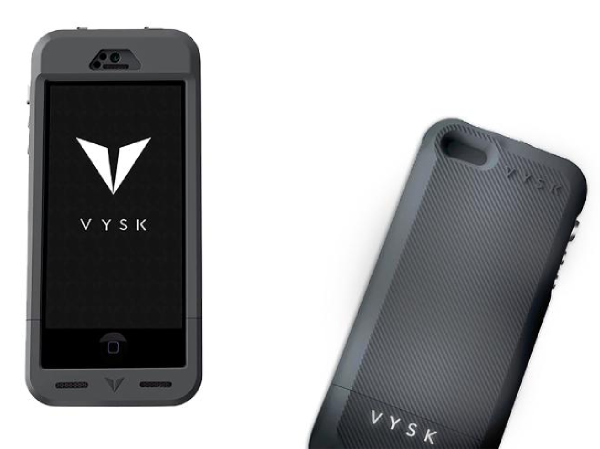
Vysk Phone Cases Provide Physical, Encrypted Security
Privacy-minded smartphone owners will want to check out the Vysk iPhone and Samsung Android smartphone cases, coming this September.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
UPDATE 7/14/2014: The EP1 case does not jam the phone's microphones in Lockdown Mode, as was originally reported. The QS1 does. The article has been corrected to reflect this.
How do you guarantee smartphone privacy? Among many app- and subscription-based solutions, San Antonio-based Vysk has a different answer: a smartphone case, for Apple and Samsung devices, that gives users the ability to encrypt their calls and texts, mute their microphones and more.
During a demonstration last month, we were impressed with Vysk's encryption and security capabilities. The consumer-targeted Vysk EP1 "Everyday Privacy" case costs $129.99, comes in gold, blue, black and gray and goes on sale this September, exclusively at Best Buy stores. An enterprise version, the QS1, costs $229.99 and launches later in 2014.
Article continues belowMORE: Best Antivirus Software 2014
The EP1 case, for iPhone 5, iPhone 5s and Samsung Galaxy S5, has a "Lockdown" mode that blocks the phone's onboard cameras with shutters. The QS1 case also jams the phone's microphones as well while in "Lockdown" mode. Mobile malware can hijack an infected phone's microphones and cameras; Lockdown mode stops that from being effective.
The EP1 case uses chat service Vysk Private Messaging and photo storage Vysk Gallery, free encryption apps that will appear in the iTunes App Store and Google Play store when the case is released. Vysk Gallery stores users' photos in an encrypted storage space, the size of which is flexible, on the phone.
A third app, the Vysk Text Line app, can be used by itself. Even if you don't own a Vysk case, you can use it to send and receive messages to other Vysk Text Lite app users.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
For encrypted calling, you'll need to spring for the more expensive QS1, which on top of its $229.99 price tag also requires a $9.99 monthly subscription fee to access the Voice over Internet Protocol (VoIP)-based Vysk Privacy Network.
Both cases plug into the Lightning port on iPhones and the microUSB port on the Galaxy S5. Because Apple won't license Lightning ports to third-party-accessory makers, iPhone owners will have to use a microUSB cable to charge the cases and the iPhones inside them.
The EP1's onboard backup battery adds up to 125 percent more battery life, and the QS1 adds up to 50 percent more battery life, Vysk says. We'll put these features to the test when we review the cases later this summer.
Vysk encryption
When using the Vysk Private Messaging on the EP1 case, or the Vysk Text Lite app alone, the encryption happens in the app itself, using a variant of the well-reputed AES-256 standard. Both apps use end-to-end encryption, with encryption keys (sort of like the passwords that "unlock" the encryption) generated in the app itself, so a message is encrypted before it leaves a phone and can't be read by man-in-the-middle snoops.
Vysk says the full Vysk Private Messaging app will include some yet-to-be-disclosed features, including what the company claims is "true anonymity."
On the higher-end QS1 case, encryption happens in the case's hardware. Hardware-based encryption is less vulnerable than software to brute-force attacks or malware, and can be more easily designed to have secure storage spaces for encryption keys and other highly sensitive data.
When two Vysk QS1 phones connect to make an encrypted call, they form a VoIP connection over the Vysk Privacy Network. Vysk's servers complete the call, but audio encryption happens on the Vysk case before the call ever leaves a device. The only conversation data Vysk receives is already encrypted and theoretically unreadable.
When the phones connect, they use a symmetric-key encryption algorithm to create a unique set of keys for encrypting that phone call and that phone call only -- a practice called "perfect forward secrecy" that discards encryption keys after the communication is terminated.
During a call, the Vysk case mutes a phone's built-in microphone and uses its own microphone to record the user's voice. That voice data is encrypted using the encryption hardware "baked in" to the onboard processor and always on.
Vysk says that its encryption-key generation does not rely on pseudo-random number generators, which can be undermined. Instead, Vysk uses a "non-deterministic, physical process" baked into the case itself to generate encryption keys, a process that Vysk says is extremely difficult for snoops to study and crack.
Vysk also says it does not keep records of call metadata, so there won't be anything to hand over to a curious government agency. When we sat down with Vysk, the Vysk Privacy Network wasn't encrypting packet headers to ensure total anonymity, but the company says that will happen in the near future.
Email jscharr@tomsguide.com or follow her @JillScharr and Google+. Follow us @TomsGuide, on Facebook and on Google+.
Jill Scharr is a creative writer and narrative designer in the videogame industry. She's currently Project Lead Writer at the games studio Harebrained Schemes, and has also worked at Bungie. Prior to that she worked as a Staff Writer for Tom's Guide, covering video games, online security, 3D printing and tech innovation among many subjects.
 Club Benefits
Club Benefits










