Bitdefender Offers Free Anti-Ransomware Tool
The antivirus firm Bitdefender has a new version of its free anti-ransomware tool, which protects against three common ransomware strains.
Worried about ransomware locking up your Windows computer? Antivirus firm Bitdefender has a free tool that may offer some relief.
The latest version of Bitdefender's free Anti-Ransomware tool offers at least limited protection against CTB-Locker, Locky and TeslaCrypt, three of the most common strains of encrypting ransomware.
It does so by mimicking the "markers" that ransomware places on infected systems to prevent a second infection, and also limits unknown applications from launching from unusual locations on a system's hard drive.
"We had been looking at ways to prevent this ransomware from encrypting files even on computers that were not protected by Bitdefender antivirus and we realized we could extend the idea," Bitdefender's Catalin Cosoi said in a company blog posting.
MORE: Best Antivirus Software
The free tool works differently from the anti-ransomware defense built into all paid versions of Bitdefender antivirus software. That defense asks the user to designate certain directories — for examples, My Documents — as "protected" from alteration from unknown applications.
The tool installs quickly and runs mostly in the background, although you can configure it to run on computer startup and minimize the interface screen.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
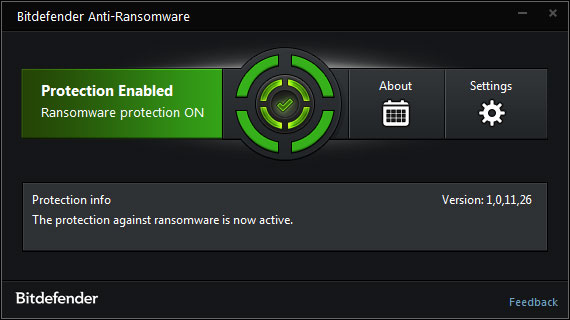
"We constantly update the tool and add support for new families of ransomware as we identify weak spots in the way they mark the system as infected," a Bitdefender representative told us via email.
An earlier version of the Bitdefender Anti-Ransomware tool protected against CryptoLocker and CryptoWall, two other well-known strains of encrypting ransomware. But those have evolved past the grasp of this tool.
Encrypting ransomware generally exploits known software flaws and infects systems through malicious email attachments, corrupted websites or weaponized online ads (aka malvertising). Windows PCs are the primary target, but Android, Linux and Mac encrypting ransomware also exists.
Certain files, or sometimes entire hard drives, are encrypted, and often the only way to recover them is by paying a ransom of between $200 and $600.
Corporate IT departments can usually defend against ransomware, as can well-protected consumer machines. But organizations such as small businesses, hospitals and local government agencies, which often run outdated software without adequate protections, are sitting ducks.
Just yesterday (March 28), a chain of 10 non-profit hospitals in the Washington, D.C., area had to shut down its computer network after infection by encrypting ransomware.
To make sure you don't become a victim of encrypting ransomware, follow a few simple steps.
1. Back up your computer's hard drive at least once a week. Daily is better, and more than one backup drive is better still.
2. Keep your computer's operating system and applications fully patched.
3. Disable Java in your Web browsers. Set Adobe Flash Player to "click-to-run", or disable it entirely.
4. Don't open any email attachments you weren't expecting. Many businesses have been infected by fake resumes and invoices; if you must view an attachment, download it to a spot on your hard drive, then browse to it, right-click it and inspect it with antivirus software before opening it.
5. Create a limited-user account on your PC or Mac and use that for your regular activities. Use the administrative account only for installing, updating and removing software.
6. Install and run robust antivirus software that includes browser and email protections, and make sure it automatically updates its malware definitions at least once a day.

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits











