News
Explore News
Latest News

Google and Apple's next phones could be the first to feature Samsung's latest OLED displays
By Scott Younker published
A new report claims two Samsung rivals could get the company's latest OLED display first.

Ticking time bomb bug in macOS disables network connectivity after 49 days — but there’s a fix
By Anthony Spadafora published
Newly discovered macOS bug completely disables your internet connection if your Mac is left on for 49 days without a reboot.

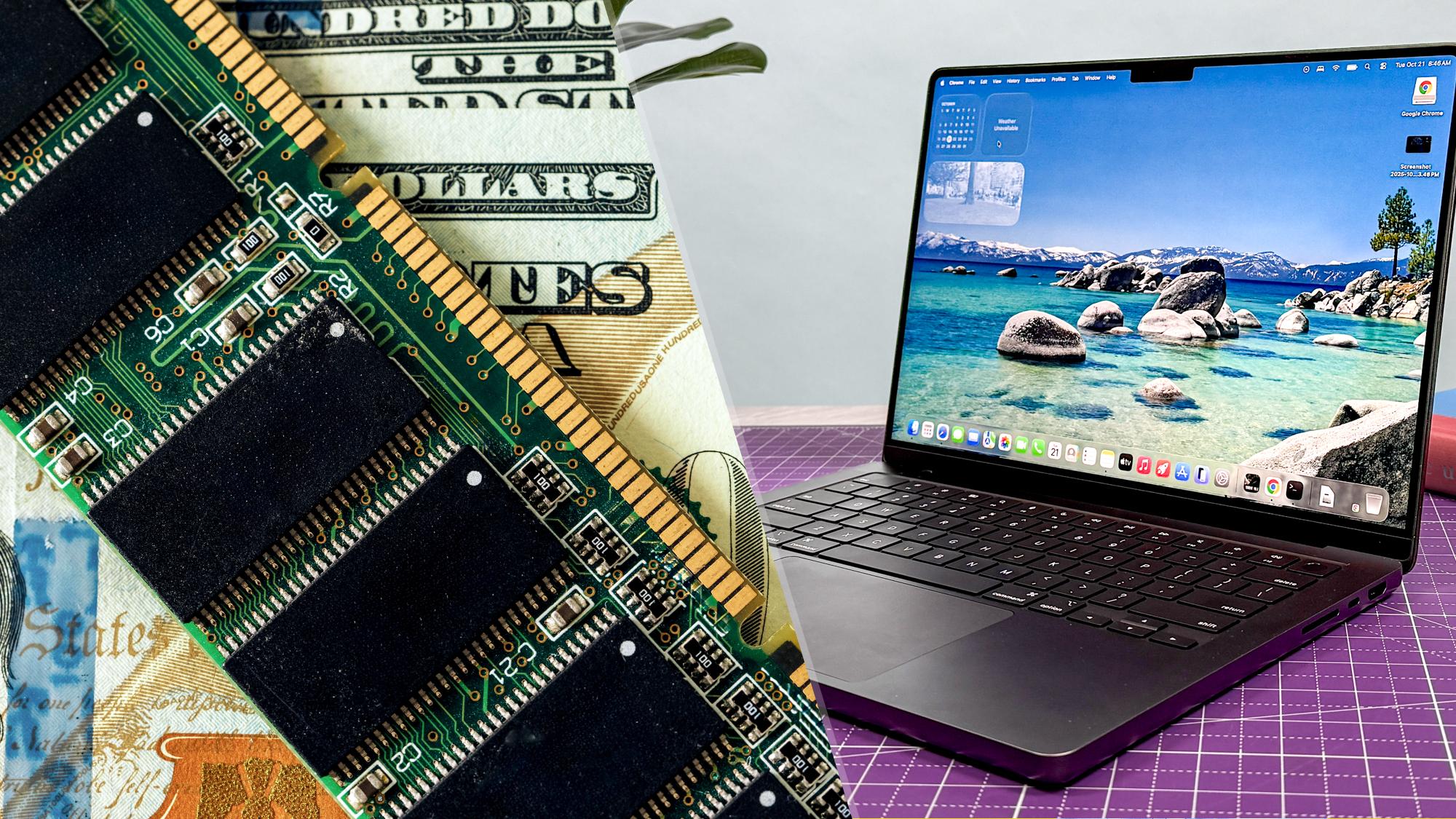
PC sales are up, but don’t be fooled — IDC report warns RAMageddon is just getting started
By Jason England published
PC sales are up, but don’t be fooled. New IDC data suggests a "red herring" boom as RAM shortages and logistics chaos threaten to send laptop prices skyrocketing.

There's a simple way to watch The Masters 2026 for FREE
By Krishi Chowdhary published
We've found an easy way to watch The Masters 2026 live streams free from anywhere in the world.

Best Garmin deals in April 2026
By Millie Davis-Williams last updated
The best Garmin deals for runners, swimmers, fitness buffs, and newbies alike.

Best Chromebook deals and prices in April 2026
By Millie Davis-Williams last updated
The best Chromebook deals ranging from budget machines to premium 4K models.

An Nvidia N1 CPU reportedly spotted on engineering motherboard — here’s what we know
By Tony Polanco published
A listing on a Chinese resale platform may offer a glimpse of an Nvidia N1. Here's what we know.
NordVPN redesigns its desktop app – here's what's new
By Aleksandar Stevanović published
NordVPN has redesigned its desktop app with a cleaner UI, unified search, and improved connection controls. Here's what's changed
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
 Club Benefits
Club Benefits