LastPass, 1Password and other password managers can be hacked: What to do now
Multiple password-manager flaws permit password theft
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
UPDATED March 25 with further comment from Dashlane, and on March 27 with notification from RoboForm that one of the flaws has now been patched in the RoboForm Android app.
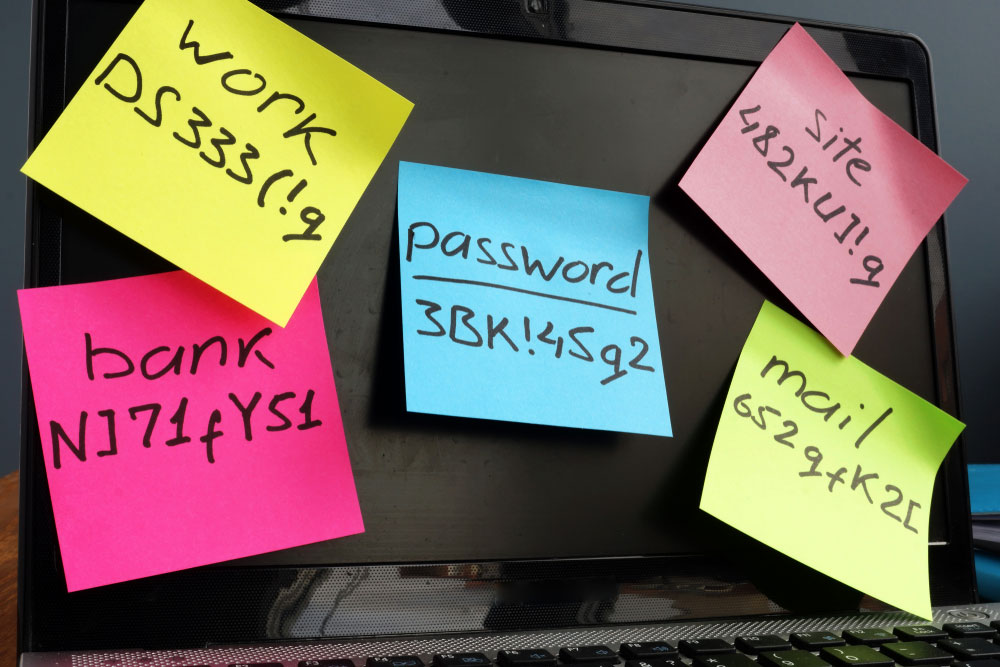
Five widely used password managers have serious flaws, some of which have been publicly known for years, a pair of researchers said in an academic paper published earlier this month. Not all of the flaws have been fixed.
Dashlane, Keeper, LastPass, 1Password and RoboForm, in the form of their Android apps and Chrome browser extensions for Windows, were analyzed by Michael Carr and Siamak F. Shahandashti of the University of York in England in 2017 and 2018.
Article continues below- The best password managers: Protect your accounts online and offline
- Free family movies and TV shows: What to watch on Amazon, Sling and more
- Plus: Zoom vs. Google Hangouts: Which video chat service is right for you?
The researchers found that each password manager had flaws that could let attackers steal passwords from either the Chrome browser extension or the Android app.
A few made it possible to guess the access PIN for the Android apps, giving an attacker full control, or even to "brute force" the master password to the account via the Chrome extension.
"Vulnerabilities in password managers provide opportunities for hackers to extract credentials," Shahandashti said in a University of York news posting. "Because they are gatekeepers to a lot of sensitive information, rigorous security analysis of password managers is crucial."
How you can make your password manager stronger
In response to queries from Tom's Guide, representatives from all five password managers pointed out that the researchers' analyses were conducted two years ago, and that many of the flaws described in the paper had since been fixed, although not all of our questions were answered.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
We still recommend that you use one of the best password managers, because it will permit you to make your passwords all unique and strong.
But make sure that the master password you choose is especially strong. Avoid using a PIN to quickly unlock the password manager's mobile app -- use your fingerprint or your face. And don't "sideload" Android or iOS apps from off-road app stores -- use the official Google Play or Apple stores.
From worst to just bad
Dashlane fared worst in the study, being vulnerable to seven different security flaws, including five that had been discovered in 2013 and 2016. 1Password had the fewest vulnerabilities with four, but in truth, none of the password managers came out with flying colors.
For its part, Keeper's Craig Lurey said in a very detailed blog post that Keeper "immediately processed and addressed all reported critical, high and medium-priority issues within 24 hours" of receiving the vulnerability reports from the researchers in 2018.
UPDATE: After this story was initially published, Dashlane sent us a similarly detailed rundown of what it had done to address the various vulnerabilities outlined in the paper. Its explanations are in italics throughout.
App phishing
LastPass and 1Password were both successfully "phished" by a phony app the researchers created that simply shared the same file name as the real Google Android app. Both password managers would see the app's file name and autofill the user's real Google credentials into the fake app.
"If a victim is tricked into installing a malicious app, it will be able to present itself as a legitimate option on the autofill prompt and have a high chance of success," Shahandashti said.
The researchers said that LastPass told them that fixing the rogue-app flaw was a low priority. But LastPass disputed that in communications with Tom's Guide, saying that in 2018 "we implemented changes to our LastPass Android app to mitigate and minimize the risk of the potential attack."
"Our app requires explicit user approval before filling any unknown apps, and we've increased the integrity of our app associations database in order to minimize the risk of any 'fake apps' being filled/accepted," LastPass told Tom's Guide. "This type of vulnerability would not only require a significant amount of effort on the side of the attacker but also a significant number of mistakes to be made by a user."
App PIN brute-forcing
The researchers found that Dashlane and RoboForm did not adequately limit incorrect entries of the four-digit access PINs to launch their Android apps, which users can type in instead of master passwords for the sake of convenience.
Brute-force attacks against the PINs, which have a maximum of 10,000 possible combinations, could be successful in a few hours and would give attackers full control of the password managers.
"This attack has the potential to be catastrophic for the victim," the researchers wrote in their paper.
"A malicious attacker would have full access to the application, providing there is no prompt for the user to re-authenticate using something other than the PIN," they added. "Access to the application in both Dashlane and RoboForm enables the user to view, modify or delete records within the password manager's vault."
1Password was vulnerable to this flaw as well, but it apparently fixed the flaw within days of being notified by by the researchers. RoboForm told Tom's Guide that this issue would be fixed in the next Android release.
Dashlane apparently told the researchers that fixing this flaw was a low priority. Its representatives did not specifically address the issue in communications with Tom's Guide.
UPDATE: In subsequent communications with Tom's Guide, Dashlane said: "We do not enable the PIN code by default or recommend using it, although some of our customers prefer to use it. It is less secure than a proper master password, which we do recommend."
UPDATE: RoboForm told Tom's Guide on March 27 that the PIN brute-force flaw had now been fixed in the most recent version of the RoboForm Android app.
Master-password attacks in browser extensions
All the password managers except Keeper did not seem to limit incorrect guesses of the user's master password in the Chrome browser extension.
In theory, an attacker could just keep trying new entries, although successfully "cracking" the master password and getting full control of the account might take thousands of years.
RoboForm told Tom's Guide that it had "server-side protection" against this kind of attack, which could mean that a RoboForm server detects multiple incorrect guesses in the browser extension and takes countermeasures.
Taking a different approach, 1Password made a strong argument to Tom's Guide that limiting incorrect entries in a password manager's browser extension is a dumb idea.
"Lockout in the UI [user interface] doesn't offer a real defense," 1Password's Jeffrey Goldberg told us in an email. "A serious attacker is not going to try to brute-force through the app itself. Instead, the attacker will make their own copy of the local data and will use an off-line cracking tool."
"At the same time, such lockout in the UI can do real harm," Goldberg added. "It can lead to accidental or malicious lockout. More importantly, it can give the user the false impression that they can get by with a weak master password."
UPDATE: Dashlane later told us that this was "an attack vector inherent to encryption itself, although an attacker would have to have access to an encrypted vault in the first place by compromising a user’s device, either physically or at a user-level remotely."
Clipboard data theft
All the services except 1Password were vulnerable to attacks on the Windows Clipboard that would steal passwords being copied from one application to another. The attacks could be as simple as someone with unauthorized access to a computer hitting "Paste" in an open document.
RoboForm told us that in its next Windows release, "we will be implementing an option for clearing the clipboard after a set period of time."
Keeper's Lurey suggested that users use autofill instead of Clipboard to enter credentials in online services, whenever possible.
He added that an existing optional feature in the iOS and Android Keeper apps, and the Windows and Mac desktop apps, will automatically clear the operating system's clipboard after a period of time. (The desktop apps are not the same as the browser extensions.)
Malicous URLs, subdomain stacking and HTTPS confusion
In 2016, LastPass was found to be vulnerable to attacks in which specially formed URLs tricked the password manager into autofilling the credentials for one website into another website's login field.
That flaw was quickly fixed by LastPass back then, but ironically, the York researchers found that all four of the other password managers were vulnerable to this attack in 2017 and 2018.
Keeper told Tom's Guide that it "performs strict matching of the root domain prior to filling a password on any target website."
All five password managers could be fooled by domain names that appear to be subsets of other domains, and none of the five were able to distinguish between insecure HTTP and secure HTTPS connections.
In other words, "evil.foobar.com" could capture the credentials for "foobar.com," even though it's possible for the "evil" subdomain to be under someone else's control.
And a man-in-the-middle attack could capture a password being sent to "http://www.foobar.com" instead of "https://www.foobar.com", yet the password managers did not seem to distinguish between the two types of links.
Both of those flaws could easily be exploited to reveal stored passwords, and both were disclosed in an unrelated academic paper in 2013.
UPDATE: Communicating with Tom's Guide after this story was first published, Dashlane said that "we do not allow autofill on unencrypted connections to web sites. (Those that use only HTTP, not HTTPS.) If a user chooses to still use Dashlane to fill a password form, we warn them first that it is not secure."
Dashlane added that "we use the same protocol as most browsers do to establish cookie limitations, using the publicly maintained Public Suffix list (publicsuffix.org/list/) to determine which domains should be allowed to be treated as a group versus being isolated as separate sites."
Making the right design decisions
Keeper said it had fixed both of the latter flaws in its browser extension since the study was conducted, but both Dashlane and RoboForm pushed back against the researchers' conclusions, telling Tom's Guide that password managers do need to be useable as well as secure.
"I'm not sure it's a question of us 'not fixing flaws' as much making design decisions that balance realistic security needs and humane UX [user experience]," a Dashlane spokesman told Tom's Guide.
"Because sites themselves often change or have multiple login pages, users expect RoboForm to provide the ability to AutoFill on more than just a single login page for each site," a statement provided by a company representative said.
"It should be noted that RoboForm's AutoFill always requires the user to manually click submit, thus providing an opportunity for the user to give the site and URL a once over before proceeding," the statement added.
"That said, we are examining implementing an option to warn users when there is a mismatch based on the above three cases so they can decide how and if to proceed on a case-by-case basis."

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits










