News
Explore News
Latest News

Nintendo Direct confirmed for June 9 — here’s where to watch and what to expect
By Tony Polanco published
A June Nintendo Direct will happen on June 9 at 10 am ET. Directly after, a Nintendo Treehouse event will showcase some of the games. Here are all the details.
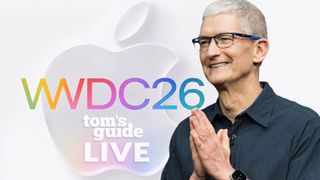
Apple WWDC 2026 Live: New Siri, iOS 27, Apple Intelligence and all the news as it happens
By Mark Spoonauer, John Velasco last updated
WWDC 2026 is going to introduce Apple's latest software developments, including Apple Intelligence and a new Siri that will be taking charge.

Stop bringing ants into your home: The simple mistake I made with my cut flowers
By Camilla Sharman last updated
The surprising reason your home could suddenly be full of ants.

How to watch 'Love Island USA' season 8 online from anywhere — stream 2026 episodes, full cast, first dumping of the season
By Adam Marshall last updated
Here's how to watch "Love Island USA" season 8 online wherever you are in 2026 as Ariana Madix and a new throng of love seekers head to Fiji.

How to watch 'Love Island U.K.' season 13 online from anywhere — Stream 2026 episodes for FREE, boys are in the doghouse
By Adam Marshall last updated
Here's how to watch "Love Island U.K." 2026 wherever you are, with free options explained. Will the contestants of season 13 be lucky in love?

Why gardeners are sprinkling grill ash on their plants (it's not as surprising as it sounds)
By Cynthia Lawrence published
Forget fertilizer — this unexpected grill waste could give these popular plants a healthy boost and help them thrive all season.

5 new Netflix movies and shows you need to stream this week (June 8-14)
By Malcolm McMillan published
Dig into all the new Netflix movies and shows this week, including "Song Sung Blue," "Sweet Magnolias" season 5 and more.

How to watch F1 2026 live online — Formula 1 streams, schedule, Barcelona-Catalunya Grand Prix
By Adam Marshall last updated
See how to watch F1 2026 live streams for free and from anywhere with information on international broadcasters and this season's Formula 1 schedule.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!

 Club Benefits
Club Benefits












