Macs under threat from CloudMensis spyware — what you need to know
Apple’s Lockdown Mode can’t come soon enough

A previously unknown backdoor has been discovered in macOS that is currently being exploited in the wild to spy on users of compromised Macs.
First discovered by researchers at the cybersecurity firm ESET, the new malware has been dubbed CloudMensis. The capabilities of CloudMensis show that its creators designed it to gather information from victims’ Macs and the malware is able to exfiltrate documents and keystrokes, listing email messages and attachments, listing files from removable storage and screen captures according to ESET.
While CloudMensis is certainly a threat to Mac users, it's incredibly limited distribution suggests that it is meant to be used as part of a targeted operation. Based on what ESET’s researchers have observed so far, the cybercriminals responsible deploy the malware to target specific users that are of interest to them.
Article continues belowESET researcher Marc-Etienne Léveillé provided further insight on his analysis of CloudMensis in a press release, saying:
“We still do not know how CloudMensis is initially distributed and who the targets are. The general quality of the code and lack of obfuscation shows the authors may not be very familiar with Mac development and are not so advanced. Nonetheless, a lot of resources were put into making CloudMensis a powerful spying tool and a menace to potential targets.”
Using cloud storage services to collect information
One thing that sets CloudMensis apart from other malware families is how it utilizes cloud storage services to boost its capabilities.
After gaining code execution and administrative privileges on a compromised Mac, it runs a first-stage malware that retrieves a second stage with additional features from a cloud storage service according to ESET.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
The second stage is a much larger component that is packed with features to collect information from the compromised Mac. While there are 39 commands currently available, CloudMensis’ second stage is intended to exfiltrate documents, screenshots, email attachments and other information from victims.
CloudMensis uses cloud storage to both receive commands from its operators and to exfiltrate files. Currently, it supports three different providers: pCloud, Yandex Disk and Dropbox.
Based on metadata from cloud storage services used with the malware, it appears that the operation first began transmitting commands to bots at the beginning of February of this year.
Lockdown Mode to the rescue but not just yet
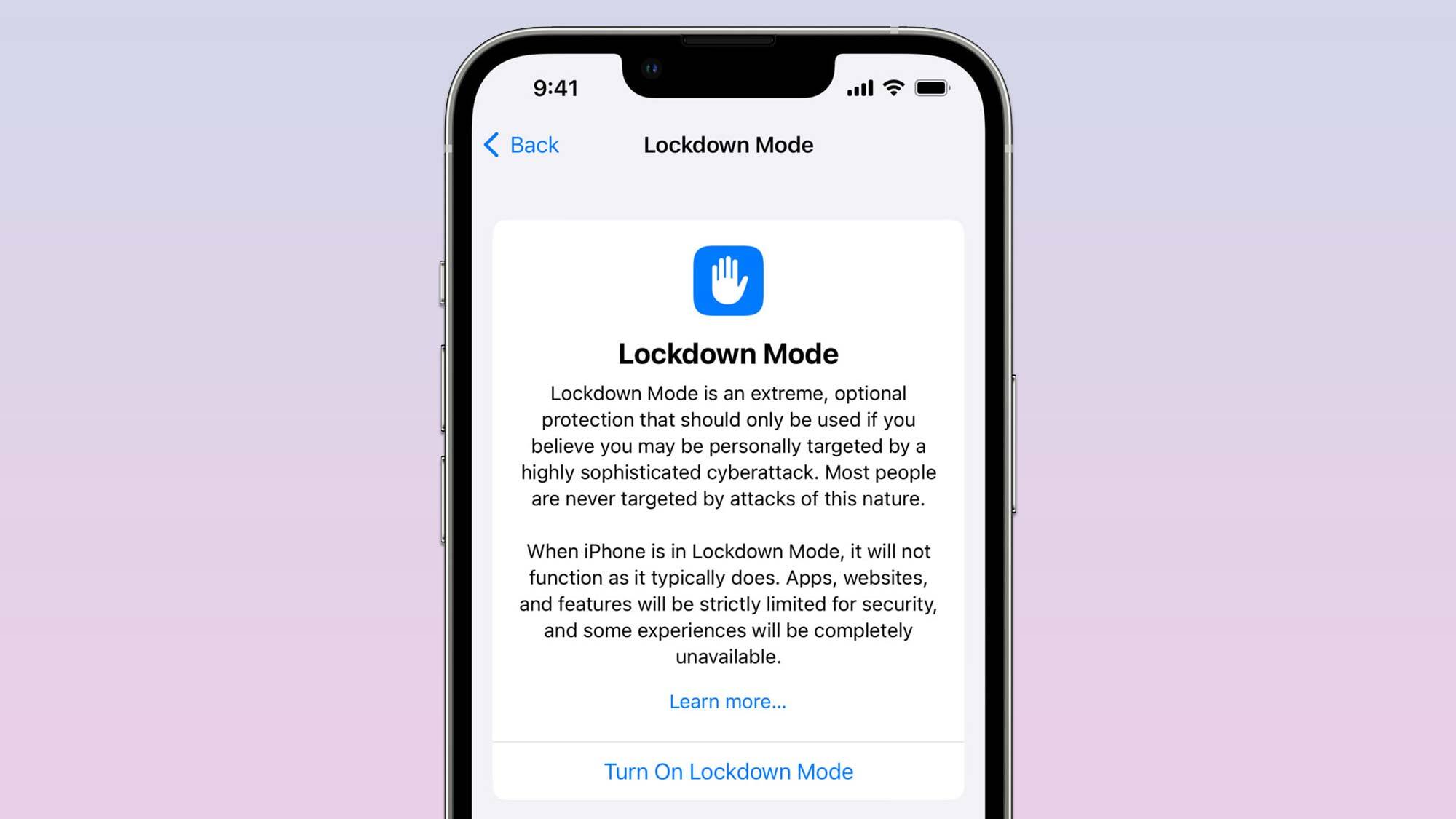
Although it’s not yet available, Apple’s new Lockdown Mode for iPhones, iPads and Macs will help users of the company’s devices avoid being infected with malware when it launches this fall alongside iOS 16, iPadOS 16 and macOS Ventura.
Lockdown Mode is able to prevent these types of infections by disabling many of the features frequently used by cybercriminals to gain code execution and deploy malware.
As no undisclosed vulnerabilities or zero days were found to be used by the group behind CloudMensis in ESET’s research, the best thing you can do to protect yourself from it at the moment is to ensure your Mac and other Apple devices are running the latest software.

Anthony Spadafora is the managing editor for security and home office furniture at Tom’s Guide where he covers everything from data breaches to password managers and the best way to cover your whole home or business with Wi-Fi. He also reviews standing desks, office chairs and other home office accessories with a penchant for building desk setups. Before joining the team, Anthony wrote for ITProPortal while living in Korea and later for TechRadar Pro after moving back to the US. Based in Houston, Texas, when he’s not writing Anthony can be found tinkering with PCs and game consoles, managing cables and upgrading his smart home.

 Club Benefits
Club Benefits










