Are you prepared for Q-day?
A privacy storm is coming - are you ready for it?

Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
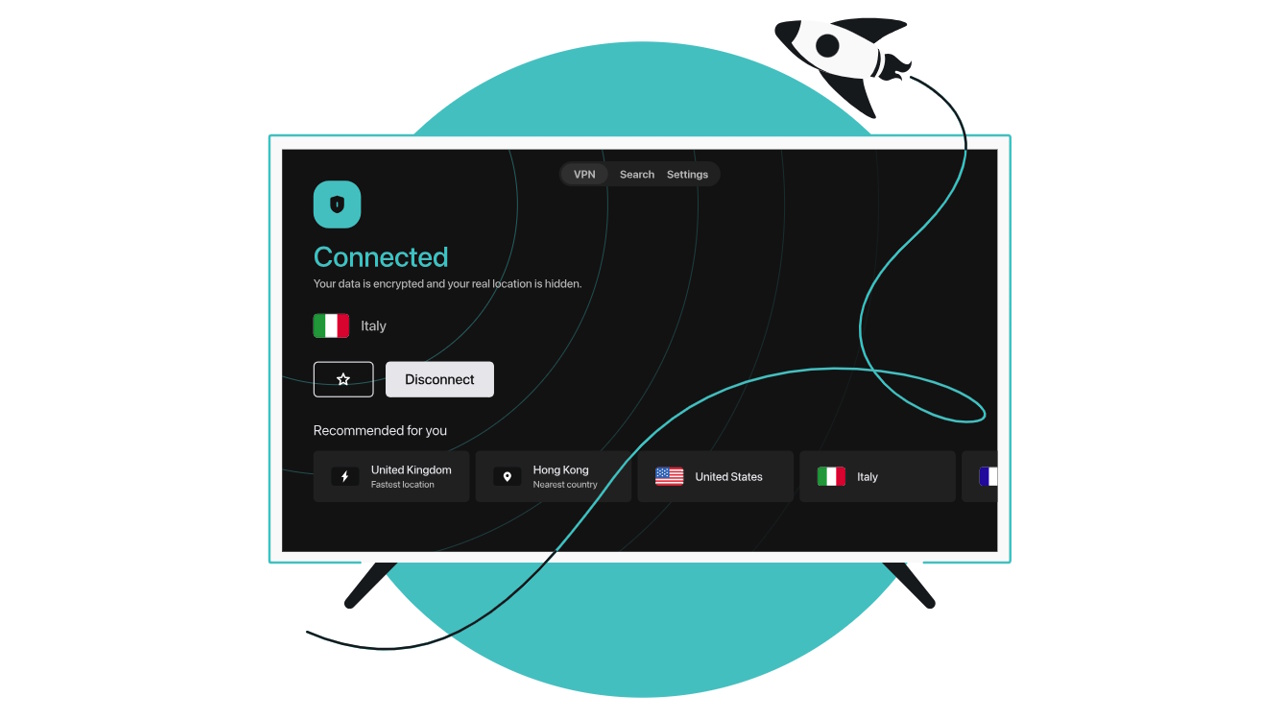
Using a virtual private network (VPN) is a fantastic way of keeping your data secure while you’re online. It works by encrypting your data so that it can’t be viewed by any third parties, such as hackers, advertisers, or government bodies.
But, while the best VPNs are some of the most reliable cyber security tools available at the moment, there might come a day when many of them are rendered obsolete. Quantum computers are incredibly powerful machines that use quantum physics to make their computations a lot more efficient than those done by the classical computers that are currently in use.
As it stands, quantum computers are only being used in research facilities, including science labs, universities, and supercomputer centers. But there will come a time when quantum computers are more widely available and strong enough to break most encryption algorithms that are being used to protect a lot of the world’s online data.
This day is known as Q-day and is predicted to happen at some point in the next five years. It could have huge ramifications across the world, as such a high percentage of online data will be rendered vulnerable to attacks.
Even if you use a VPN, the encryption might not be strong enough to withstand an attack from a quantum computer. That is, unless you use a VPN that offers post-quantum cryptography, in which case, your data will remain hidden.
In this article, we’ll explain how to prepare for Q-day so that your level of protection is future-proofed and recommend the best VPNs with post-quantum encryption.

What is Q-day?
Q-day is the day that quantum computers become advanced enough that they can successfully break the encryption algorithms that are used to protect most online data. Experts have predicted that this will happen in the next five years and that, when it does, it’s likely to wreak havoc across the world if we’re not prepared.
The reason why the current level of encryption is more than sufficient is because it would take traditional supercomputers millions of years to break these algorithms. But a quantum computer has much more sophisticated processing power, meaning that it could crack these algorithms without any difficulties. As it stands, this would leave a huge proportion of the world’s online data exposed and vulnerable to attack.
If the world doesn’t prepare for this day, the impact will be enormous, leading to potentially devastating political, financial, and social repercussions that could cause huge damage to societies and governments around the world.
Pretty much any data you can think of, from emails, documents, and online banking to government policies and private business plans could be hacked and even made public at any time. Plus, we would see a huge rise in cases of identity theft and online scams. Phishing scams would suddenly become a lot more believable, as hackers would be able to use deeply personal information to credibly trick users.
Luckily, there are ways you can safeguard your data long before Q-day happens. Experts have already developed post-quantum encryption algorithms specifically designed to protect data from quantum computer attacks. Some VPNs are already offering this level of encryption, so signing up for one of those will ensure you’re protected no matter when Q-day hits.

How can I protect myself from Q-Day?
Thankfully, there are plenty of experts working on post-quantum encryption, and some of these algorithms are available to you right now. All you need to do is sign up for a VPN that offers this level of protection.
We’ll talk you through our recommendations for the best VPNs that currently offer post-quantum encryption in the next section. But for now, we’ll talk you through the different types of post-quantum algorithms that are available and the benefits of each, so that you’re armed with all the information you need to choose the right protection for you.
At the moment, there are a few different types of post-quantum encryption that are powerful enough to protect your data against the superior processing power of quantum computers. Here, we’ll describe each type currently on offer.
Lattice-based post-quantum encryption
Currently the most popular form of post-quantum encryption, lattice-based cryptography uses the computational difficulty of solving lattice-based problems.
In short, it means it can deliver extremely robust protection that can withstand post-quantum attacks. This is because a lattice is a geometric structure with infinite data points arranged in a periodic pattern, making it extremely difficult, although not impossible, for a quantum computer to crack.
For it to successfully break a lattice-based post-quantum algorithm, a quantum computer would need to perform a brute force search of all possibilities to find the private key that would unlock its encryption. Realistically, this would take far too much time to manage, even for a quantum computer.
This makes lattice-based cryptography one of the most efficient types of encryption to keep data safe from quantum attacks. It’s already been successfully integrated into extremely complex protocols that are designed to be able to remain unbreakable after Q-day.
Code-based
Code-based encryption stands out from other forms of cryptography schemes that use number theory or elliptic curves because it uses the principles of coding theory instead. This makes it incredibly difficult to break because it’s almost impossible to decipher the linear error-correcting codes it uses to protect data from hacks.
To achieve this, it uses a public key, which has been generated by error-correcting code, along with a private key that’s almost impossible to hack, even for a quantum computer.
Multivariate polynomial-based
As you might have gathered from the name, multivariate encryption is based on the problematic nature of solving multivariate polynomial equations. This form of algebraic equations uses a public key made from a system of multivariate equations. It also relies on a private key that’s based on being able to efficiently solve these equations.
So far, this isn’t something a quantum computer would be able to manage easily, so it’s extremely effective in protecting your data against any quantum computers.
Hash-based
This type of encryption is sometimes referred to as hash-based signatures or one-time signatures. It’s a form of digital signature encryption that uses the properties of cryptographic hash functions to deliver a highly sophisticated level of protection.
It differs from elliptic curve and number theory schemes by utilizing one-way properties and collision resistance to guard against the hacking abilities of quantum computers.
Despite the fact that hash-based cryptography is actually pretty simple, it’s also incredibly effective in keeping data safe from quantum computers. They’re also really easy to roll out. Hash-based signatures are pretty small, which means they can be used to protect most apps and devices without using up too much processing power.
Additionally, the verification processes are fairly fast compared to other forms of post-quantum encryption. So, it’s an efficient and scalable option.
Isogeny-based
Supersingular elliptic curve isogeny cryptography (SIDH) is based on the mathematics of isogenies and elliptic curves. It relies on secure key exchange protocols that are strong enough to withstand both classical and quantum computers. Therefore, it’s a safe choice for futureproofing your cybersecurity.
How can VPNs help against Q-day?
Currently, using a VPN that offers post-quantum encryption is the best way to protect your data against the impact of Q-day. As the name suggests, these post-quantum algorithms are resistant to attacks from both classical and quantum computers, thereby providing you with a vital extra layer of security that should futureproof your online security through Q-day and beyond.
Unfortunately, not all VPN providers offer this level of encryption yet. So even if you use a reputable VPN, it might not be sufficient to give you that extra protection against Q-day.
Of course, there’s still time to sign up for a VPN that has this level of security. At the moment, quantum computers aren’t a huge cyber security risk, as they’re mostly being used for research in universities and science labs.
However, experts predict that at some point in the next five years, these highly sophisticated machines will gain enough processing power and become widely available enough to become a serious security threat. Plus, if there isn’t sufficient protection from post-quantum cryptography being rolled out, the majority of the world’s data could be vulnerable to being hijacked.
Given that post-quantum encryption isn’t widely used yet, the best thing you can do to protect your data is to sign up for a VPN that offers this level of security. Although the danger isn’t imminent, it’s a sensible idea to make sure your provider offers this before you sign up for a lengthy subscription.
Which VPNs use post-quantum encryption?
We’ve researched a wide range of providers to check what level of encryption they offer and have recommended the following five VPNs with post-quantum encryption:
ExpressVPN
Currently ranked as one of our top VPN services, ExpressVPN is a fantastic choice for anyone who’s concerned about cyber security, as it comes with post-quantum protection. While it uses the industry standard AES 256-bit encryption to guard against traditional cyber attacks, it also has created its own open-source Lightway protocol, which has post-quantum algorithms to keep your data secure from quantum computers.
To further put your mind at rest, ExpressVPN’s Lightway protocol has been successfully audited two years in a row by Cure53. This means that Cure53, an independent company, tested it and found that it’s every bit as good at protecting your data as ExpressVPN claims.
Despite its highly sophisticated security, the Lightway protocol delivers fast and consistent speeds that won’t slow you down. In our recent speed tests, it came in at an impressive 410 Mbps, which means that you’ll be able to enjoy lag-free gaming, streaming, and conference calls. Considering that ExpressVPN’s other protocol is OpenVPN, which is over 20 years old, we’d strongly suggest using Lightway for a faster, smoother, and more secure experience.
As we’ve already mentioned, ExpressVPN scored very highly in all our VPN tests and is a great all-round choice. It has a huge range of secure servers to connect to and can unblock all the most popular region-restricted streaming services. It’s also really easy to use and has excellent 24/7 customer support, so it’s ideal for beginners. You can test it out risk-free by taking advantage of its 30-day money-back guarantee.
QSTVPN
Advertised as a post-quantum VPN solution, QSTVPN uses post-quantum algorithms to keep its VPN connections secure enough to withstand attacks from classical and quantum computers. This means that it will keep your data safe in the short-term and the long-term, keeping you protected from the impacts of Q-day.
Despite the strong security measures, QSTVPN offers fast speeds, so you shouldn’t notice any lag in performance when you connect to one of its servers.
As you might expect, QSTVPN is an incredibly safe option, with plenty of security features, including two-factor authentication, connection mode, and automatic connection.
QAL VPN
If you’re concerned about security, QAL VPN is a fantastic solution, as it uses a number of post-quantum algorithms to bring you robust data protection long past Q-day. Three of its main algorithms use lattice-based encryption. There’s also its SPHINCS+ algorithm, which uses hash functions to guard against quantum computers.
QAL VPN is primarily designed for large businesses, so it might not be the most practical choice for individual use. However, if you’re looking for a VPN to protect your business from Q-day, we’d suggest getting a quote from QAL VPN, as this will keep your business safe long into the future.
Mullvad
Mullvad is starting to roll out quantum-resistant tunnels across its apps. It’s already available for all WireGuard protocols on the Mullvad desktop app. So if you’re primarily a desktop user on Mac, Windows, or Linux, Mullvad will offer you instant post-quantum protection. Mullvad also has plans to roll out its quantum-resistant tunnels across its Android and iOS apps. So it shouldn’t be too much longer before you can get this level of protection across all your devices.
Mullvad is using a WireGuard tunnel to offer this level of protection by sharing a secret in such a way that even a quantum computer wouldn’t be able to decipher it. Once it’s been shared, Mullvad will then disconnect and start a different WireGuard tunnel with the new shared secret. It achieves this by using Kyber and Classic McEliece post-quantum algorithms.
In a nutshell, Mullvad offers sophisticated post-quantum encryption. On top of this, it also allows customers to sign up with total anonymity, as it doesn’t request any personal details when you create an account. It’s also a good all-rounder, with fast speeds and responsive customer support.
Windscribe
Just like Mullvad, Windscribe uses the WireGuard protocol to deliver post-quantum cryptography. It achieves this by generating a completely unique pre-shared key for each of its users.
This, combined with the public and private keys used by WireGuard adds a significant level of security that will keep your data safe from quantum computers. In short, even if a quantum machine could crack the keys (which is highly unlikely), it would be unable to successfully decrypt the traffic. Therefore, your data would remain completely safe.
As if this wasn’t good enough, Windscribe also offers fast and reliable speeds, as well as 24/7 live chat customer support. It’s also capable of unblocking a huge range of region-restricted content.
Q-day FAQs
What is Q-day?
Q-day is when quantum computers have sufficient processing power and are widely available enough to crack the encryption algorithms used to protect most of the world’s online data. This currently includes banking apps, government files, and private emails.
Experts are predicting that Q-day is likely to happen at some point in the next five years and that when it does, it will leave most people’s photos, documents, and emails vulnerable to attack. Perhaps more troublingly, it could also see government secrets, medical records, and business strategies exposed.
Thankfully, there are already some forms of post-quantum encryption that will protect data against Q-day. You can access that level of protection right now by signing up for a VPN that offers this, such as ExpressVPN, Mullvad, or Windscribe.
What is post-quantum encryption?
As the name suggests, post-quantum encryption refers to a level of cryptography that’s too strong to be cracked by a quantum computer. By its very nature, it offers protection against quantum attacks, leaving your data safe and secure, even after Q-day. There are several VPNs that currently offer post-quantum protection, including ExpressVPN, Mullvad, or Windscribe.
Do quantum computers pose a threat to VPNs and encryption?
As it stands, many VPNs on the market don’t use post-quantum algorithms and would therefore not be strong enough to protect user data from a quantum computer attack. However, there are some providers, including ExpressVPN, Mullvad, or Windscribe., that offer this level of protection.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.

Olivia joined Tom's Guide in October 2023 as part of the core Tech Software team, and is currently VPN Commissioning Editor. She regularly uses VPNs to make sure they deliver what they promise, and specializes in testing VPNs with streaming sites.
- Catherine HileyFreelance Writer
 Club Benefits
Club Benefits