10 Million People Need to Stop Using This Android App Now
The AirDroid file management app has a flaw that leaves your phone open to attack, and a fix isn't coming for a couple of weeks.
The popular AirDroid file-management app could open your Android device to attack, a security firm says. Until the flaw gets fixed — hopefully, within the next two weeks — you should stop using the app.
Researchers at San Francisco mobile-security company Zimperium have discovered a flaw in AirDroid that allows malicious hackers to overcome encryption and access potentially sensitive information. The flaw can also give hackers the ability to remotely execute code on the respective device.
According to Zimperium, which spoke to ArsTechnica about the flaw, AirDroid uses a static encryption key to safeguard some data transmitted by the app. What's worse, the researchers say, that encryption key can be easily found within the app's code by anyone with a even little know-how.
Article continues belowMORE: 25 Worst Gadget Flops of All Time
Armed with that knowledge, a hacker can launch a man-in-the-middle attack on devices using AirDroid. From there, the hackers can decrypt the mobile app's communications and even get full remote control over the smartphone through a malicious software update. The hack can only occur if both the attacker and the targets are on the same Wi-Fi network.
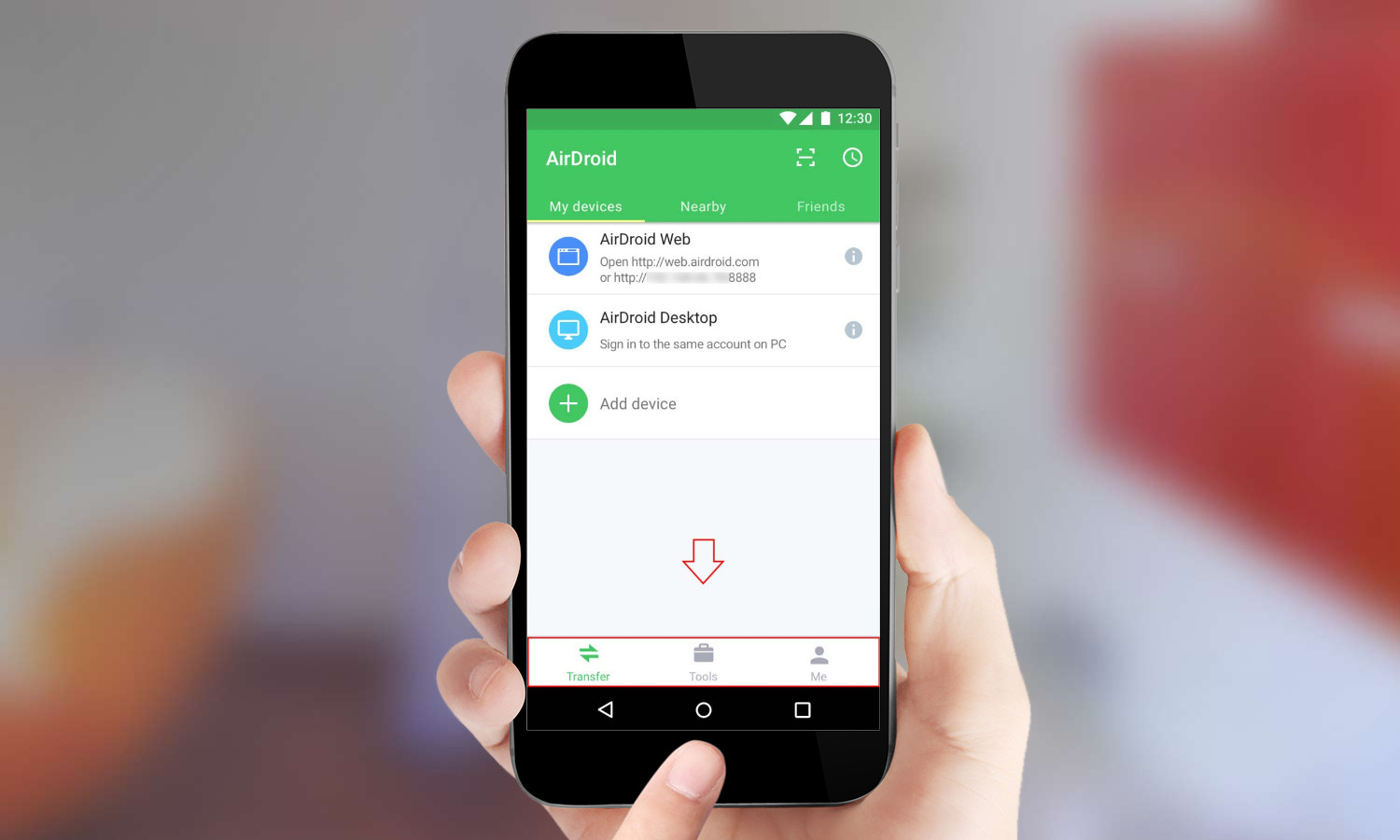
AirDroid, which was developed by Chinese company Sand Studio, is available in the Google Play marketplace for more than 30 countries. It lets users access and control their Android devices from the Web or on a PC or Mac. It also offers full backup and syncing of potentially private data such as photos and videos, and gives users access to SMS. The free-to-download app has been installed between 10 million and 50 million times, according to Google's own count on the Play marketplace.
According to Zimperium, it initially contacted Sand Studio about the flaw on May 24 and attempted to follow up with the company for a few months after the disclosure. The security firm said in its blog post that it received a response from Sand Studio about an upcoming update, but as of the Nov. 28 release of AirDroid 4.0, the flaw was still present. A second update to AirDroid on Nov. 21 also left the vulnerability in place.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
After facing outcry from some of AirDroid's millions of users on Thursday, the company issued a blog post on Friday in hopes of quelling unrest and explaining next steps. Sand Studio says that the flaw cannot be exploited on a secure Wi-Fi network. (It's not clear if that's accurate.) The company then acknowledged that it hasn't yet updated the software, blaming the delay on coding complexities. The company added that it's been working "tirelessly" to fix the problem and says it hopes to have it fixed "within two weeks as planned."
Still, the damage is done and AirDroid users are now at risk for at least another couple of weeks. To address that, Zimperium had some solutions, including telling users only to use HTTPS and additional encryption. The company also recommended users consider uninstalling AirDroid until a fix is available.
Don Reisinger is CEO and founder of D2 Tech Agency. A communications strategist, consultant, and copywriter, Don has also written for many leading technology and business publications including CNET, Fortune Magazine, The New York Times, Forbes, Computerworld, Digital Trends, TechCrunch and Slashgear. He has also written for Tom's Guide for many years, contributing hundreds of articles on everything from phones to games to streaming and smart home.

 Club Benefits
Club Benefits










