Macs under threat from malicious ads spreading malware — don’t fall for this
Clicking on these ads could leave you with a nasty malware infection

Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
Malvertising or malicious advertising has long been a threat for Windows PCs but hackers are increasingly targeting the best MacBooks and other Apple computers by using bad ads to spread Mac malware.
According to a report from Malwarebytes, a new malvertising campaign is being used to infect vulnerable Macs with the Atomic Stealer malware. First advertised on dark web forums back in April of this year, Atomic Stealer is a powerful malware strain which can not only steal crypto but also passwords from web browsers and even Apple Keychain.
Up until now, the cybercriminals who have paid for access to this Malware-as-a-Service offering have mostly used pirated software to distributed Atomic Stealer, However, that appears to be changing according to Malwareybtes who discovered a malvertising campaign that uses bad ads to infect unsuspecting Mac users with the malware.
Gaming Google Search

When downloading a new program or app for their Mac, many users often type its name into Google and click on the first search result as they believe this will lead them to what they’re looking for. Unfortunately, this is exactly what you shouldn’t do.
You see, Google Search displays ads at the top of the page and you need to scroll down to get to the actual search results. Many people have likely figured this out by now but many haven’t and this is how hackers game Google Search in their malvertising campaigns.
By buying ads that match well-known and established brands, hackers are able to trick potential victims into visiting their phishing sites as if they were an official site. This is a lot easier than using phishing emails or other tactics that could be spotted and stopped by security software.
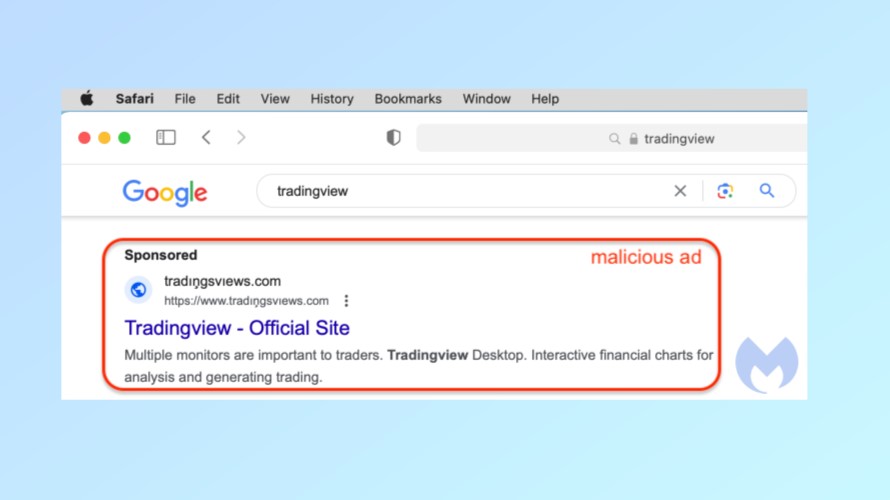
In the example above from Malwarebytes, the ad itself impersonates the financial charting platform TradingView. However, if you take a closer look at the address the ad points to, you’ll notice that there are special font characters that make it appear like the company’s actual website to the untrained eye.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
Clicking on this ad takes potential victims to a phishing site with download buttons for Windows, Mac and Linux. While the Windows and Linux buttons download the NetSupport RAT, the Mac one downloads the Atomic Stealer malware.
Bypassing GateKeeper
Instead of needing to be copied into the Apps folder on your Mac, the downloaded app impersonating TradingView comes with special instructions on how to open it in order to bypass Apple’s GateKeeper security software. GateKeeper is designed to enforce code signing so that only apps signed with an Apple developer signature can be installed on macOS.
Since this installation file containing the Atomic Stealer malware isn’t signed correctly, it’s actually bundled in an ad-hoc signed app so its permissions can’t be revoked. Once launched, it will keep prompting victims for their user password in a never ending loop until they finally give in. With your Mac’s user password in hand, the hackers behind this campaign can steal all sorts of personal and financial data from your computer.
Once this is done, the malware sends this stolen data back to a command and control (C&C) server controlled by the hackers behind this campaign. This data can then be used to commit fraud or even identity theft.
How to stay safe from Mac malware

Although your Mac comes with Apple’s own malware scanner in the form of xProtect, you still need to be careful online.
For instance, you should only download new programs or apps from established companies — or to really be on the safe side, only from the Mac App Store. Likewise, when searching for a program on Google Search (or any other search engine for that matter), you’re going to want to scroll down until you find the official website instead of clicking on the ads that appear first in the search results.
While GateKeeper and xProtect do a good job of keeping you safe, for additional protection, you may also want to consider investing in one of the best Mac antivirus software solutions. These paid antivirus programs are updated more regularly and often contain useful extras like a VPN or a password manager.
In a statement to Tom's Guide, senior director of threat intelligence at Malwarebytes, Jérôme Segura provided further insight on the false sense of security that many Mac users have and how the threat landscape has now changed, saying:
"For a long time many Mac users have had this idea that they are somehow protected from viruses and other threats that affect their Windows counterparts only. We know this is not true, but yet that misconception still persists. This malvertising campaign is actually a great example of how easy it is for criminals to devise not only delivery methods (malicious ads) but also malware payloads (stealers) targeting Macs. I would go even further by saying that infection rates for Mac-specific campaigns might be higher than Windows ones because users are unaware and likely aren't running security software at all."
Malvertising has been going on for years but it’s only recently that we’ve seen hackers and other cybercriminals shift their tactics to target Macs in addition to Windows PCs. Regardless of what platform you’re using, you always need to be careful before you click and especially so when downloading files or programs online.
More from Tom's Guide
- You should think twice before clicking on ads — even on Google Search
- These Mac apps are secretly spreading malware — delete them now
- This mysterious malware uses Wi-Fi to give hackers your exact location

Anthony Spadafora is the managing editor for security and home office furniture at Tom’s Guide where he covers everything from data breaches to password managers and the best way to cover your whole home or business with Wi-Fi. He also reviews standing desks, office chairs and other home office accessories with a penchant for building desk setups. Before joining the team, Anthony wrote for ITProPortal while living in Korea and later for TechRadar Pro after moving back to the US. Based in Houston, Texas, when he’s not writing Anthony can be found tinkering with PCs and game consoles, managing cables and upgrading his smart home.
 Club Benefits
Club Benefits










