Billions of devices vulnerable to Wi-Fi 'FragAttacks' — what to do
Flaws affect pretty much anything that connects to Wi-Fi
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
Up to a dozen serious security flaws affect almost all Wi-Fi-enabled devices, including PCs, Mac, iPhones, Android phones, most routers and smart-home devices, says a Belgian security researcher. You'll want to update Windows straight away; most other devices will have to wait for patches.
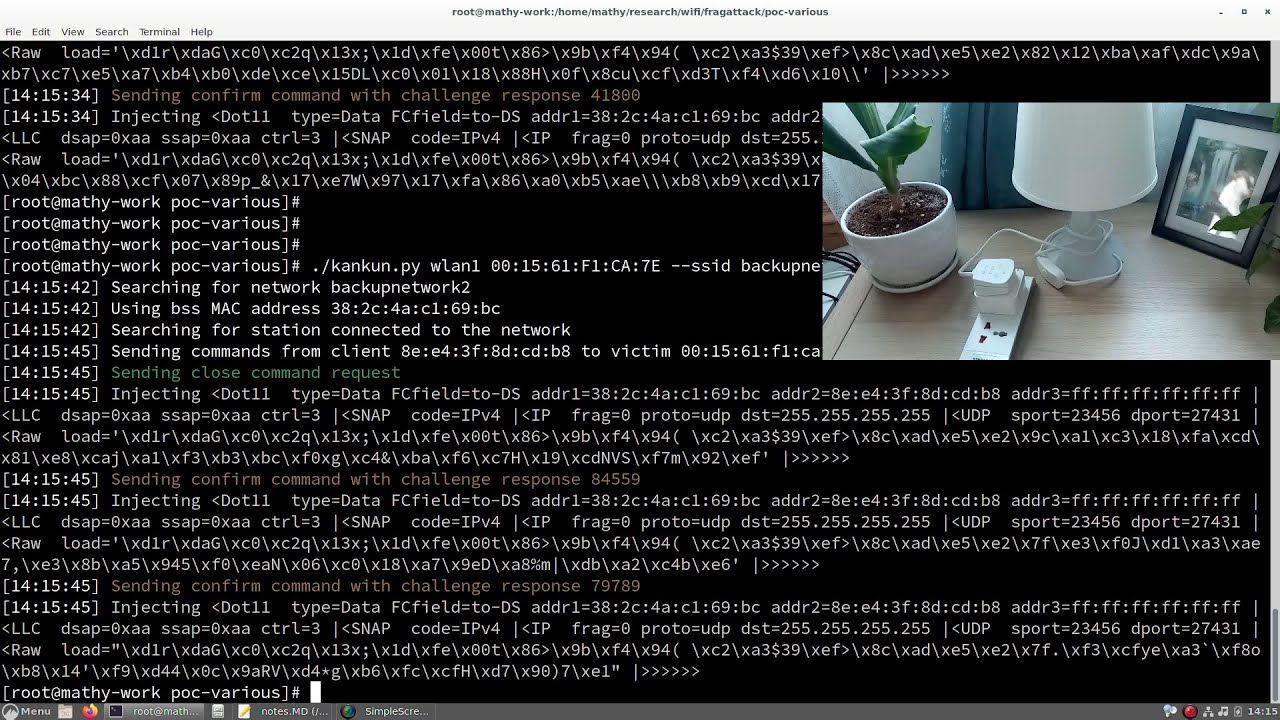
Mathy Vanhoef, who in 2017 co-discovered the widespread KRACK flaws in Wi-Fi, groups these 12 new flaws under the name "FragAttacks." He's put an impressive amount of documentation online to explain the flaws, including a dedicated FragAttacks website, an academic research paper, a presentation slideshow, two YouTube videos and a software tool to detect vulnerable devices.
- Your router's security stinks: Here's how to fix it
- The best Windows laptops you can buy right now
- Plus: Colonial Pipeline cyberattack: Everything you need to know
Simply put, the FragAttacks, some of which date back to the first version of Wi-Fi in 1997, let nearby devices "within radio range" attack your Wi-Fi network to steal information and send devices to bad places online.
Article continues belowEspecially vulnerable, Vanhoef says, are smart-home devices that have a hard time receiving software updates. All Wi-Fi security protocols can be broken by at least some of these attacks, including WEP, WPA2 and WPA3.
"Every Wi-Fi product is affected by at least one vulnerability and ... most products are affected by several vulnerabilities," Vanhoef writes on the FragAttacks website. "The discovery of these vulnerabilities comes as a surprise, because the security of Wi-Fi has in fact significantly improved over the past years."
As far as Vanhoef is aware, none of these flaws has been exploited by malicious hackers. But he can't rule out that some of the more device-specific flaws may already have been discovered and exploited.
Here's a video of Vanhoef using one of these flaws to attack a Mac, making the Mac connect to a rogue Wi-Fi network and sending it to potentially malicious websites.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
What you can do to protect yourself against FragAttacks
Microsoft patched Windows 10, Windows 8.1 and even Windows 7 against the three most common FragAttacks flaws with yesterday's (May 11) round of security updates. So update your Windows devices today.
Linux patches are slowly being pushed out, enterprise-networking-hardware makers Cisco and Sierra Wireless are planning patches, and rival Juniper Networks has already released some.
Among consumer router makers, Netgear has an advisory page that says firmware updates are already available for some routers, listed on the page. The company adds that it is "developing and testing additional firmware fixes, which we will release as they become available."
There do not seem to be patches available yet for Macs, iPhones, iPads or Android devices, or other major brands of home Wi-Fi routers. (We checked their recent security advisories.) We'll update this story when we receive more information.
In the meantime, says Vanhoef, you can protect yourself by making sure you have a strong, unique Wi-Fi network password and by making sure to connect only to websites that have the HTTPS encryption protocol enabled by default.
The latest version of Chrome (and by inference, Edge and Brave) enforces HTTPS connections when possible; for other browsers, Vanhoef recommends the HTTPS Everywhere plug-in. If you're fairly technical, you can manually set your DNS on your router so that it cannot be changed by another party.
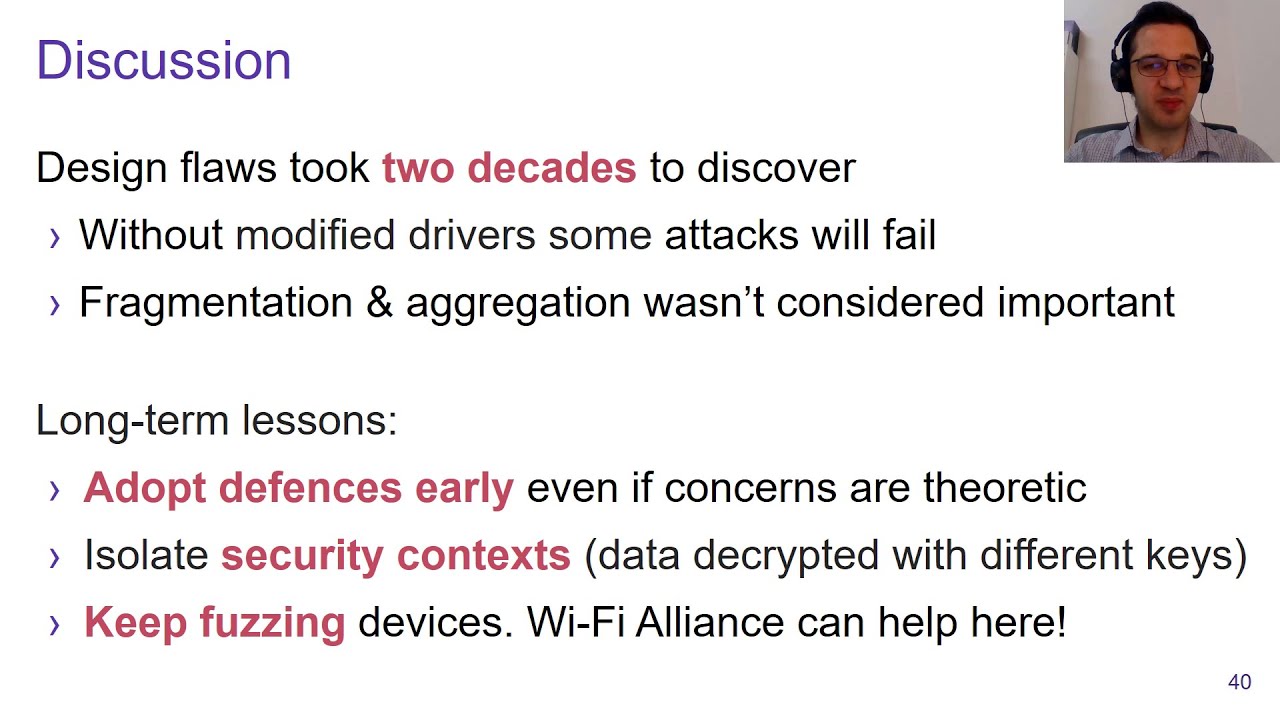
The most widespread flaws are the trickiest to exploit
The good news, says Vanhoef in his online slideshow, is that the "widespread flaws [are] relatively tricky to exploit in practice" and the easy-to-exploit flaws are "not widespread in practice."
The most serious flaws, he says on the FragAttacks website, involve "programming mistakes" in certain Wi-Fi devices and software implementations. He declines to reveal the affected products but implies that there are a lot of them.
[UPDATE: The devices affected by faulty software implementations are said to include the Samsung Galaxy S3 smartphone, Windows driver software for Alfa Wi-Fi dongles and the Linux, NetBSD and OpenBSD kernels.]
"The impact of our findings depends on the specific target," Vanhoef writes. "For some devices the impact is minor, while for others it's disastrous."
Vanhoef has been working with the Wi-Fi Alliance, the Industry Consortium for Advancement of Security on the Internet and various vendors for the past nine months to get fixes for these flaws implemented.
He will be presenting his finding at the USENIX Security and Black Hat USA conferences in August, but you can already watch his 12-minute USENIX presentation on YouTube.
- The best smart home devices you can buy

Paul Wagenseil is a senior editor at Tom's Guide focused on security and privacy. He has also been a dishwasher, fry cook, long-haul driver, code monkey and video editor. He's been rooting around in the information-security space for more than 15 years at FoxNews.com, SecurityNewsDaily, TechNewsDaily and Tom's Guide, has presented talks at the ShmooCon, DerbyCon and BSides Las Vegas hacker conferences, shown up in random TV news spots and even moderated a panel discussion at the CEDIA home-technology conference. You can follow his rants on Twitter at @snd_wagenseil.

 Club Benefits
Club Benefits