Hackers can steal your credit card details in the real world — how to stay safe
Think twice before you swipe your credit card

Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
Even if you’re the type of person who rarely shops online to protect your security, hackers can still steal your credit card details by infecting point-of-sale (POS) terminals at stores, gas stations and other retail locations with malware.
According to a new report from Cybernews, hackers were able to steal 167,000 credit card numbers and other payment records from unsuspecting customers by using PoS malware. While this financial data could be used to commit fraud, the cybersecurity firm Group-IB estimates the hackers responsible could make as much as $3.3 million just by selling these stolen credit card numbers on the dark web.
Back in April 2022, the firm’s researchers discovered a Command and Control (C2) server used by the MajikPOS malware. However, the C2 server’s administrative panel also contained data on another POS malware strain called Treasure Hunter.
Article continues belowEven though the C2 server and its admin panel remain active at the time of writing, Group-IB shared its findings with a US-based financial threat-sharing organization and law enforcement agencies within the unit.
What is POS malware?
Unlike traditional malware that infects PCs or mobile malware that infects smartphones and tablets, POS malware is specifically used to infect POS devices like credit card readers that are used by retailers worldwide.
This kind of malware aims to steal the data stored on a credit card’s magnetic stripes or magstripes. However, as credit and debit cards with chips and tap to pay have become more popular, POS malware is now being used less by hackers and other cybercriminals than it was in the past.
When data is stolen off a credit card by POS malware, it’s sent back to a C2 server controlled by an attacker. Fortunately, this stolen information can’t be used to make purchases online since the magnetic strip doesn’t contain a card’s CVV or Card Verification Value number which is usually found on its back underneath the magnetic stripe.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
The states with the most infected POS devices
After finding the C2 server used by the hackers behind the MajikPOS and Treasure Hunter POS malware, Group-IB’s researchers used IP addresses contained on the server to find which states had the most instances of infected POS devices.
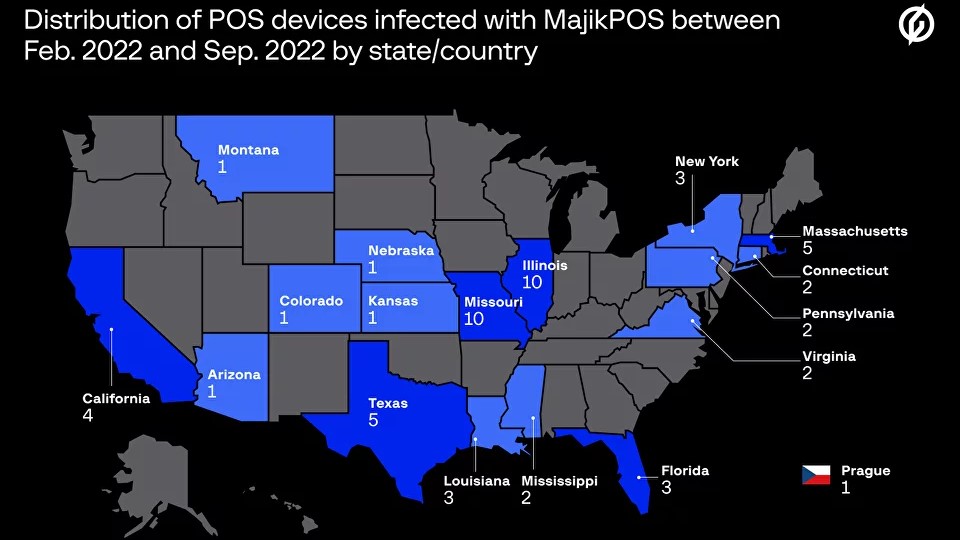
According to a blog post, between February and September of this year, Illinois and Missouri had the most devices infected with MajikPOS at 10 each followed by Massachusetts and Texas with 5 infected devices each and Florida, New York and Louisiana with three infected devices each. When it came to the Treasure Hunter POS malware, Texas had 12 infected POS devices followed by Florida with 10 and New York and South Carolina with five each.
Based on threat intelligence data from Group-IB, hackers made $908 million between April 2021 and April of this year selling compromised credit card data with the average price of each credit card dump at $20 a piece.
How to stay safe from POS malware and credit card skimmers
While you can install one of the best antivirus software solutions to stay safe from malware on PC and one of the best Android antivirus apps to protect your Android smartphone from malware, staying safe from POS malware is harder to do since businesses and not customers are in charge of securing POS devices.
As such, Trend Micro recommends in a blog post that consumers regularly monitor all of their financial accounts for any signs of suspicious activity. It’s also worth investing in one of the best identity theft protection services as they can help you recover any lost funds and restore your identity should it be stolen.

To avoid credit card skimmers which are often installed at gas stations or ATMs to steal card data, it’s best to fill up your vehicle at well-lit gas stations with plenty of security and the same goes for when you withdraw money from the bank. Before using any machine, you should take a quick look to make sure it hasn’t been tampered with. You want to make sure the card reader doesn’t seem loose or damaged and that part of the machine isn’t a different color. Likewise, if its keypad is hard to press or the numbers feel thicker than usual, a false keypad may have been installed.
Using a mobile wallet is another way to get around credit card skimming and POS malware but if you’re really concerned, you can always just pay in cash instead of using your card.
Now that credit cards are becoming more secure thanks to the introduction of chips and tap-to-pay, POS malware will likely continue to be less popular among hackers. Still though, it’s something you need to be aware of and on the lookout for when out in the real world.

Anthony Spadafora is the managing editor for security and home office furniture at Tom’s Guide where he covers everything from data breaches to password managers and the best way to cover your whole home or business with Wi-Fi. He also reviews standing desks, office chairs and other home office accessories with a penchant for building desk setups. Before joining the team, Anthony wrote for ITProPortal while living in Korea and later for TechRadar Pro after moving back to the US. Based in Houston, Texas, when he’s not writing Anthony can be found tinkering with PCs and game consoles, managing cables and upgrading his smart home.
 Club Benefits
Club Benefits










