Listen Up! Your Headphones May Be Spying On You
A new piece of malware turns headphones into microphones -- even when they're not plugged into a computer's microphone jack.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
It's always been possible to use a pair of headphones as a low-grade microphone by plugging them into a microphone jack, but a new piece of malware does one better. It makes headphones record sound even when plugged into a computer's headphone jack. No need to worry, though: At present, this is just a proof-of-concept.
The malware was created by researchers at Israel's Ben-Gurion University of the Negev, who detail their work in a paper entitled SPEAKE(a)R: Turn Speakers to Microphones for Fun and Profit. The trick is so beautifully simple, it raises the question of why no one has ever tried this before.
Headphones and microphones basically use the same technology, but in reverse. Headphones convert electric signals to sound; a microphone converts sound to electric signals. The malware Ben-Gurion researchers designed simply makes the computer think that a headphone port is a microphone port instead.
Article continues belowMORE: Best Antivirus Software and Apps
Here's how SPEAKE(a)R might work: A cybercriminal distributes it to an intended victim. The delivery method is not really important, but it would likely be a targeted attack, so perhaps it would come via e-mail or even a well-placed USB stick. SPEAKE(a)R infects the audio chip on the PC's motherboard and flips the user's headphone jack to a microphone jack whenever it's not in use.
Assuming the user leaves his or her headphones plugged in even when not actively listening to anything, the attacker can then use recording software (presumably bundled with the malware) to record private conversations and store them for later listening.
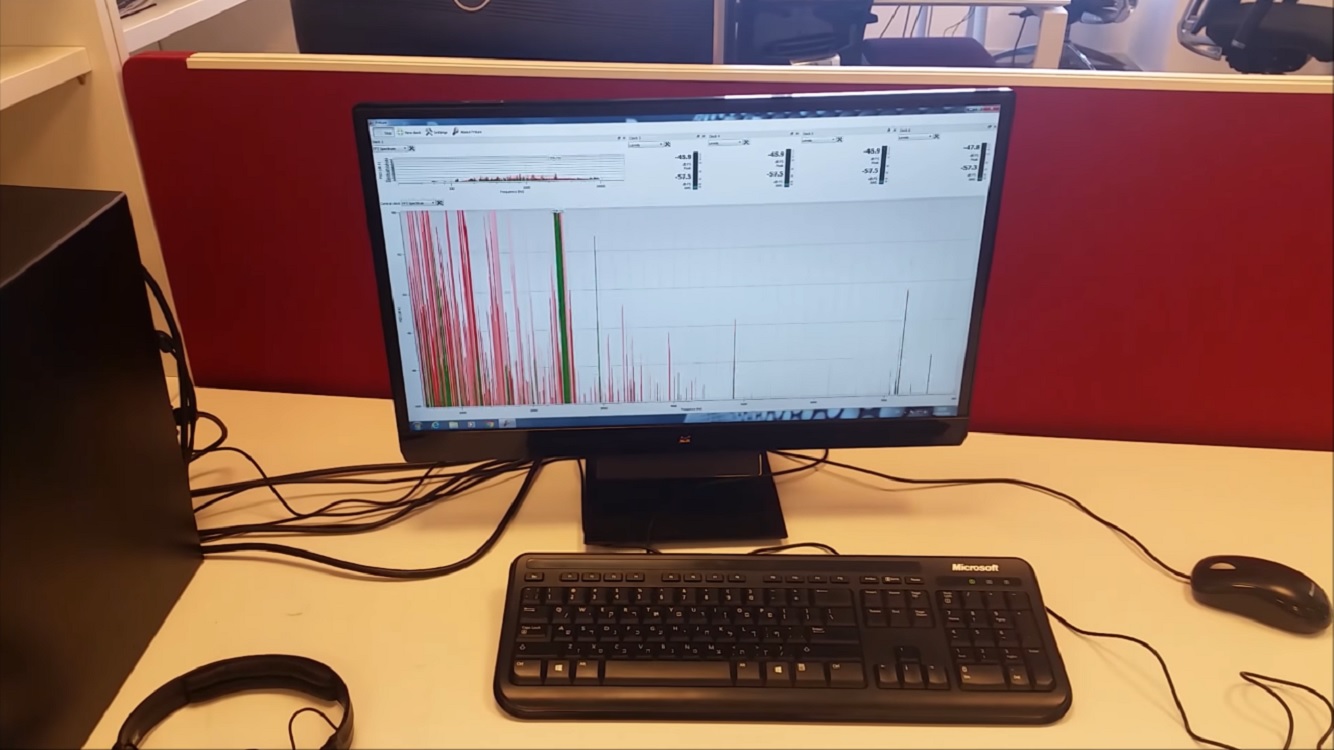
It’s not hard to see how the SPEAKE(a)R malware could be troublesome, especially in a corporate environment. Plenty of office workers have a set of work headphones that they leave plugged in all the time, and it would be trivially easy to overhear their conversations with coworkers. The average set of headphones make a pretty poor mic, but as long as the audio is intelligible (which it is), any extra sound quality is just gravy.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
Users need not worry about SPEAKE(a)R too much, though. In addition to the fact that it's only a research project, the use-case scenario for it seems extremely convoluted. You would have to choose a target and know for a fact that he or she not only keeps headphones plugged in, but also exchanges secretive information within earshot of them. You'd probably also need to know what kind of computer the target uses, although there are only a few major makers of audio chips for motherboards.
SPEAKE(a)R makes no sense as a wide-scale attack, since cybercriminals would not want to listen to hours of pointless audio in the vain hope of overhearing a credit-card number.
Furthermore, attackers might not even need to flip the input if they really wanted to listen in. Most gaming and high-end headphones today come with microphones installed for mobile compatibility, and 3.5-mm ports on new laptops generally pull double-duty as both headphone and microphone inputs. An enterprising malicious hacker could simply hit a user with hidden recording software and leave it at that. Doing so with a USB-based headset would be even easier, since there's usually only software to manipulate.
In other words, if someone wants to listen in on your private conversations, there are ways to do it, with or without a dedicated microphone. Your best bet, as always, is to be judicious about what you download, which should prevent the acquisition of malware in the first place.

Marshall Honorof was a senior editor for Tom's Guide, overseeing the site's coverage of gaming hardware and software. He comes from a science writing background, having studied paleomammalogy, biological anthropology, and the history of science and technology. After hours, you can find him practicing taekwondo or doing deep dives on classic sci-fi.

 Club Benefits
Club Benefits










