Why Cheap Security Cameras Aren't Secure at All
Hundreds of thousands of webcams from a variety of cut-rate brands can easily be hacked from afar, even without default passwords.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
If your house has a decent lock and you sleep there every night, you may not need a smart security camera. But if you do need one, you should at least buy a security camera made by a reputable manufacturer.
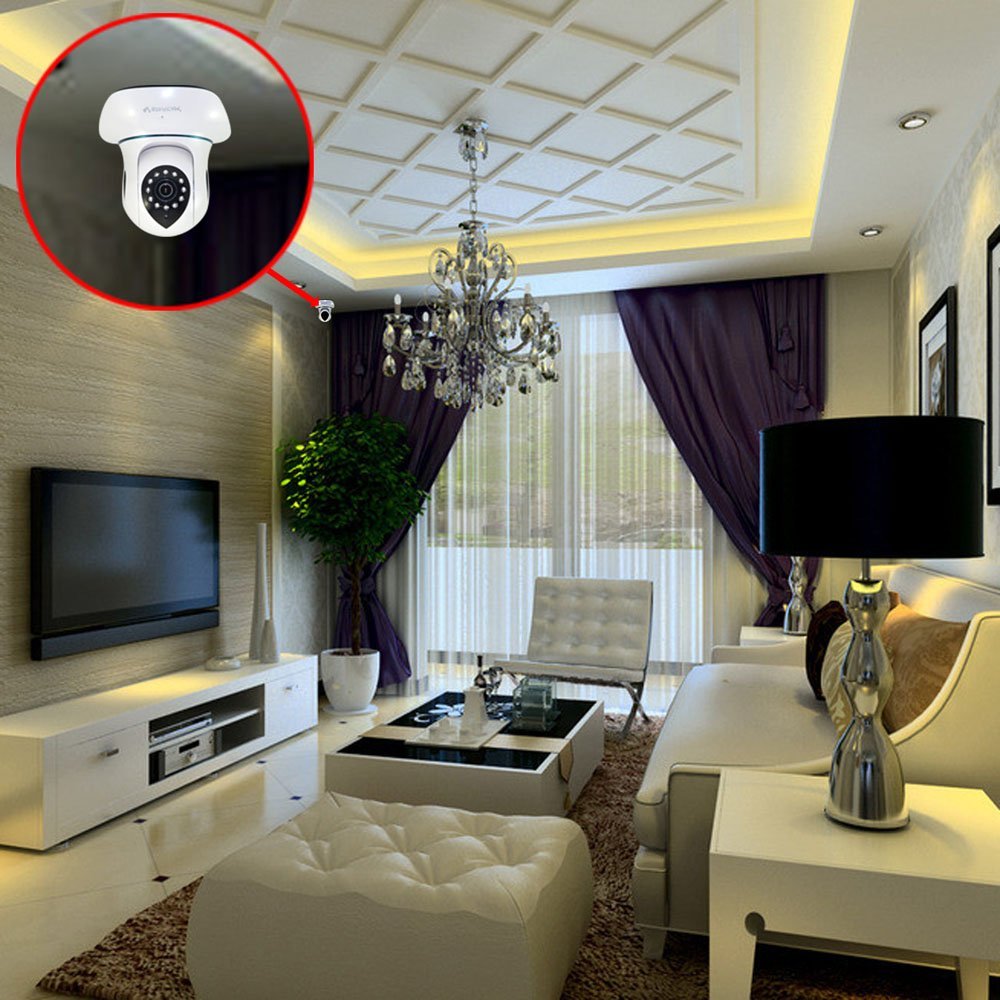
Hundreds of thousands of internet-connected security cameras from a variety of cut-rate brands may be vulnerable to a trivial hack. Not only may the camera give up your password with a bit of code, but it could also be drafted into a botnet to attack other systems. Fortunately, there's an online tool to check your camera's security.
In light of the recently distributed Mirai malware, which in October commandeered commercial security cameras and used the resulting botnet to disrupt internet connections worldwide, researchers from Boston-based security firm Cybereason thought it was high time to see whether cheap home security cameras could fall prey to a similar threat. They tested more than 30 "white-label" IP security cameras that were inexpensively produced and often sold under different brand names on eBay and Amazon for between $40 and $60, and the results were not encouraging.
Article continues belowMORE: Best Wireless Home Security Cameras
Cybereason did not reveal the brand names of all of the security cameras it tested. But one brand was VStarcam, aka Eye4, which runs on almost exactly the same software and hardware as dozens of other white-label brands. All the cameras ran older versions of Linux, including kernel 2.6.26, which was released back in 2008. The web-server software in some cameras dated back to 2002.
With old software comes old vulnerabilities. Cybereason researchers Amit Serper and Yoav Orot found a way to bypass a VStarcam camera’s authentication and request passwords, which the camera then delivered to them in plain text. Even if the user reset the default password (in this case, "888888") to something stronger, a hacker could obtain it.
From there, things just got worse. With the password in hand, the pair could use a remote server to access the camera’s root directory. Even if users then got wise to the hack and changed their passwords, it wouldn’t matter; a hacker would still have unfettered access to their systems.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
Both the bypass and the root access were enabled by zero-day vulnerabilities, meaning they were not previously known to researchers (or, hopefully, criminals). Serper and Orot found them before the camera manufacturers ever did.
Naturally, you don’t want a stranger tapping into your security camera, watching your in your private moments and listening in on your private conversations. But that’s only the beginning of what a dedicated hacker could accomplish. Since the security camera has a programmable OS and an internet connection, you could draft it into a botnet, as the Mirai malware did with other cameras. (The VStarcam's "888888" default password is not yet on Mirai's list of passwords to try.)
Although Cybereason did not reveal the details of every affected camera or how to exploit their vulnerabilities, the company's online tool will help you see if your camera is an affected model. If you enter your camera’s serial number, default password (check the instructions, and then change it), and a few more pertinent bits of information, the tool will take its best guess as to whether your camera could fall victim to the zero-day attack.
The bad news is that cheap cameras are not exactly known for their timely security updates or attentive customer service. Cybereason recommends that if you have a vulnerable camera, you should toss it in the trash. It’s not bad advice. Changing the password will not help, and it’s only a matter of time until malicious hackers discover the same vulnerability that Cybereason did.

Marshall Honorof was a senior editor for Tom's Guide, overseeing the site's coverage of gaming hardware and software. He comes from a science writing background, having studied paleomammalogy, biological anthropology, and the history of science and technology. After hours, you can find him practicing taekwondo or doing deep dives on classic sci-fi.

 Club Benefits
Club Benefits










