Massive Mac Flaw Gets Root Access in Seconds
A very simple task will let anyone gain root access to Macs running macOS High Sierra, earning easy access to settings and data.
UPDATED 9 p.m. EST Nov. 28 with comment from Apple, and 9:30 a.m. Nov. 29 with further details on how to break into a Mac.
A very simple task will let anyone gain permanent root access to Macs running macOS 10.13 High Sierra, earning easy access to all settings and data.

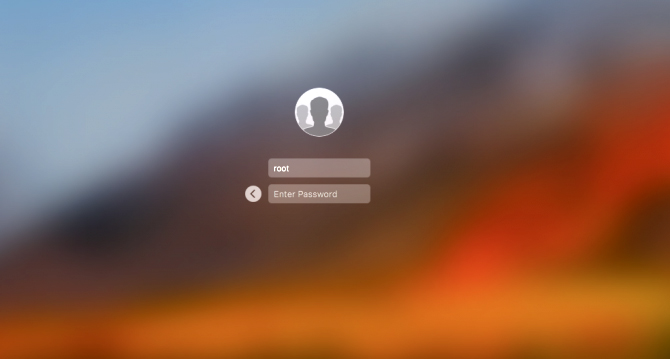
First disclosed on Twitter earlier today (Nov. 28) by Turkish app developer Lemi Orhan Egan, the bug lets anyone, not just users with administrator privileges, get into System Preferences by clicking on the lock and typing in "root" as the username and leaving the password blank. That may take several tries, but it eventually goes through.
Then it gets dastardly. The above procedure creates a new user profile that presents itself as "Other" on the Mac's primary login screen. Type in "root" as the username, type in nothing for the password, and you will open an account with complete root access.
Article continues belowUPDATE: Other methods than the one outlined about activate the root account, as demonstrated in this YouTube clip that shows an attacker using Apple's Screen Sharing feature to remotely activate the root account on a Mac to which he's connected over a network. Nor must the root password be blank -- the attacker can in fact choose any password.
MORE: Best Mac Antivirus Software
We tested this procedure on both an old MacBook Pro and the latest MacBook Air, each running High Sierra. In both cases, we were able to run routine "periodic" diagnostic commands that would usually require temporary "sudo" privileges and an administrator's password -- but this time, with no "sudo" request or admin credentials at all.
On Twitter, Apple Support wrote to Egan: "Thanks for reaching out. Send us a DM, and we'll look further into this with you."
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
We reached out to Apple ourselves but did not hear back immediately. We will update this story if we receive a response.
This is a massive security issue, as it would permit anyone to easily seize control of your laptop if they had even brief physical access. Even worse, this secret is now completely out in the open. Generally, flaws like this are disclosed privately to the company so they can be fixed without anyone taking advantage.
One way to prevent this would be to enable root access on your own, using the kosher method recommended by Apple in that link, and give the root account a password. Then you can go to the terminal to an type "dsenableroot -d" (without quotes) to turn off root access.
Anyone who tries to get in this way won't have the right password. If you want to turn root access back on, type "dsenableroot" in the terminal.
UPDATE: In a statement to MacRumors, Apple said that it was "working on a software update to address this issue." It then pointed users of macOS 10.13 High Sierra to the same Apple support page we've indicated above and suggested adding a password to the root account.
Best Mac Antivirus Software

Kaspersky Internet Security for Mac's top-shelf malware detection and barely there system impact make it the best antivirus solution.

Avast Free Mac Security's malware-squashing proficiency, negligible performance impact and included password manager make it the best free option.
Andrew E. Freedman is an editor at Tom's Hardware focusing on laptops, desktops and gaming as well as keeping up with the latest news. He holds a M.S. in Journalism (Digital Media) from Columbia University. A lover of all things gaming and tech, his previous work has shown up in Kotaku, PCMag, Complex, Tom's Guide and Laptop Mag among others.

 Club Benefits
Club Benefits












