News
Explore News
Latest News

Uma Thurman and Charlize Theron duke it out in Netflix's 'The Old Guard 2' trailer — watch it here
By Martin Shore published
Netflix has released 'The Old Guard 2', and this action-thriller sequel looks like a high-octane watch worth the five-year wait.

Google is going to start using AI to keep you safe — here's how
By Alex Hughes published
Google is keeping you safe from scams across search and your smartphone

Nintendo Switch 2 pre-orders live: Nintendo Store invites are rolling out and latest retailers to check
By Rory Mellon last updated
Nintendo Switch 2 pre-orders are live, and the next wave of stock comes from Nintendo itself. We're tracking the latest updates in this live blog.

‘Fallout’ season 2 gets major update — here’s what that could mean for the release window
By Alix Blackburn published
"Fallout" season 2 has officially wrapped filming. Here's what we know about the next season so far.

Sony just confirmed possible WH-1000XM6 launch date — here's when the ANC headphones will be unveiled
By Jeff Parsons published
Sony has seemingly confirmed the launch date of its highly anticipated XM6 over-ear headphones in the next few days.
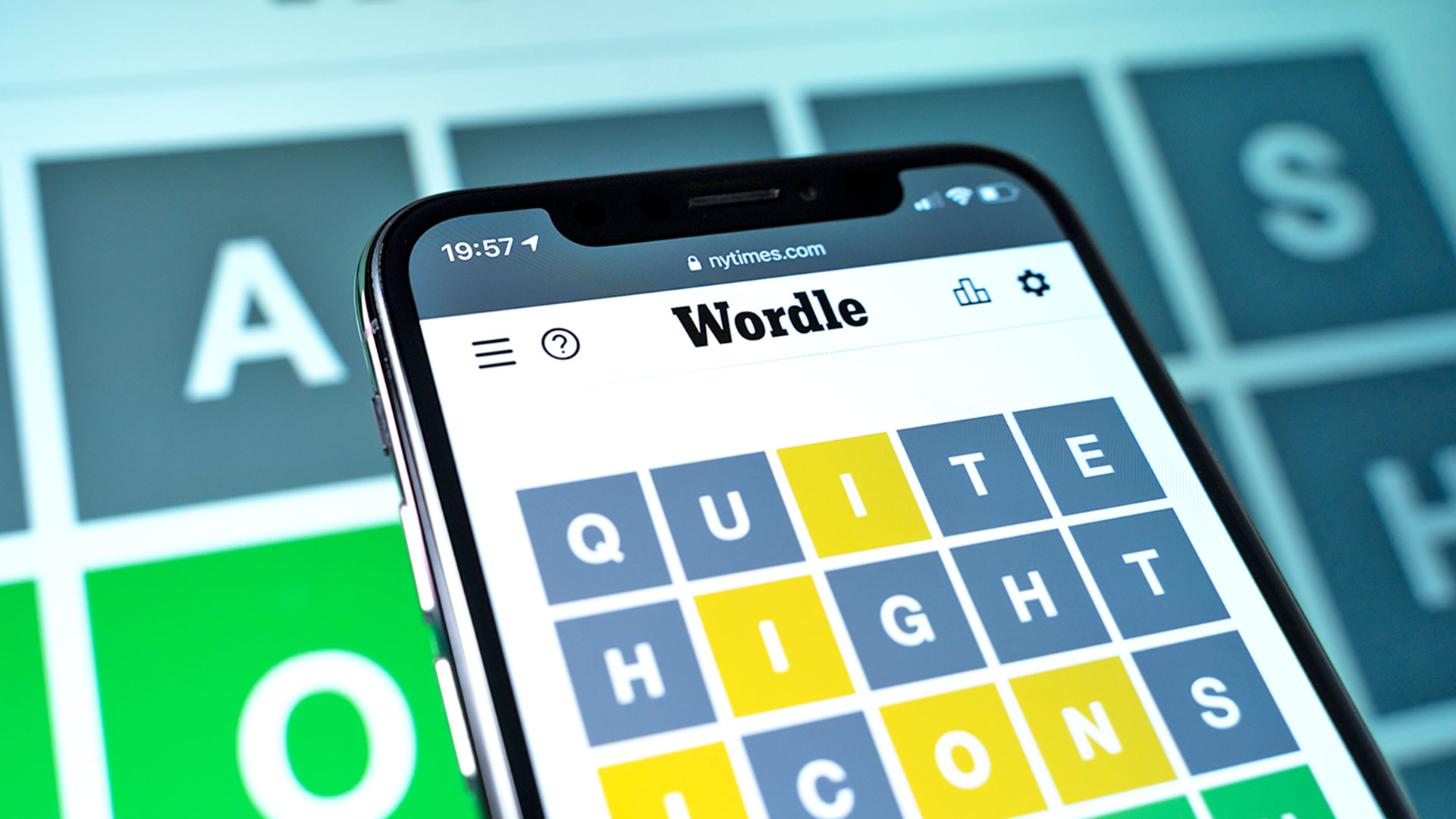
Today's Wordle hints and answer — solution #1,420, May 9
By Alan Martin last updated
Find out what today's Wordle hint and answer is and get some tips for it, plus see the solutions to previous games.

Baseus PicoGo power banks are a game-changer for charging, and I’m here for it
By Sponsored published
Sponsor Content Created With Baseus
Never suffer from low battery anxiety again...

Samsung Galaxy S25 Edge debuts Monday — 3 things we know and 2 we still need to find out
By Philip Michaels published
As the Galaxy S25 Edge draws closer, we review what we know about Samsung's ultra-thin phone plus the key details that are still missing.
Sign up to get the BEST of Tom's Guide direct to your inbox.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!


