NASA Admits Stolen Laptop Contained Control Codes for ISS
Laptop was unencrypted and among 48 stolen in the last two years.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!
You are now subscribed
Your newsletter sign-up was successful
Want to add more newsletters?
Join the club
Get full access to premium articles, exclusive features and a growing list of member rewards.
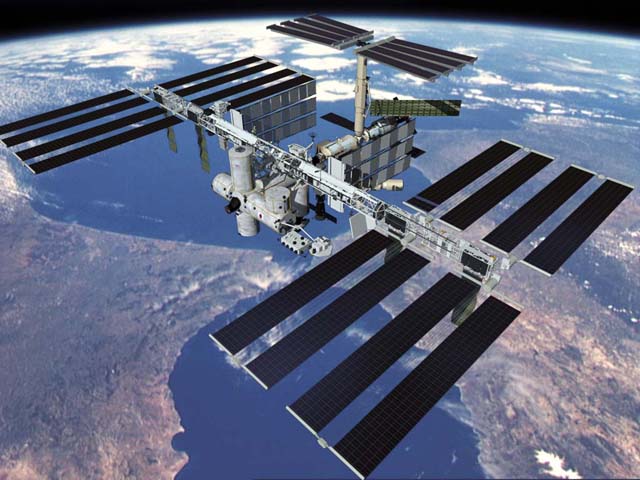
The National Aeronautics and Space Administration has revealed that a laptop stolen in 2011 contained command codes for controlling the International Space Station. NASA said the unencrypted computer went missing in March of last year and resulted in the loss of the algorithms used to command and control the ISS. The Huffington Post reports that NASA Inspector General Paul K. Martin made the revelation during his testimony before a Science, Space and Technology House subcommittee on Wednesday. However, despite Martin's admission, NASA has said that at no point in time was the ISS in jeopardy because of a data breach.
"NASA has made significant progress to better protect the agency's IT systems and is in the process of implementing the recommendations made by the NASA Inspector General in this area," NASA public affairs officer Trent Perrotto is quoted as telling SecurityNewsDaily.
Martin said on Wednesday that the laptop was one of 48 NASA notebooks or mobile devices stolen between April 2009 and April 2011. What's more, NASA was, in 2011, the target of 47 advanced persistent threats. Thirteen of these successfully compromised NASA computers.
Article continues below"These incidents spanned a wide continuum from individuals testing their skill to break into NASA systems, to well-organized criminal enterprises hacking for profit, to intrusions that may have been sponsored by foreign intelligence services seeking to further their countries' objectives," Martin is quoted by MSNBC as saying. MSNBC reports that the attacks are among more than 5000 attacks in 2010 and 2011 that saw unauthorized intrusions or malware planted on NASA systems and cost the agency roughly $7 million.
Martin said software vulnerabilities in NASA machines often go unpatched and only 1 percent of NASA mobile devices are encrypted. He said that until the space agency can implement an agency-wide encryption policy, data stored on mobile devices will remain at high risk.
Follow @JaneMcEntegart on Twitter.
Further Reading
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
Jane McEntegart works in marketing communications at Intel and was previously Manager of Content Marketing at ASUS North America. Before that, she worked for more than seven years at Tom's Guide and Tom's Hardware, holding such roles as Contributing Editor and Senior News Editor and writing about everything from smartphones to tablets and games consoles.
-
mcvf I just LoLed after reading this article. Sounds more like about schoolboy laptop than NASA computer.Reply -
JOSHSKORN I read somewhere (Associated Press, I think) that NASA had been hacked thousands of times in recent years.Reply -
A Bad Day "and resulted in the loss of the algorithms used to command and control the ISS."Reply
Not backing up critical data. That ended quite well. -
adobejesus The IT Dept in the college where I worked had a mandatory policy that any systems that could handle Win7 used BitLocker and systems that could not used TruCrypt but yet NASA doesn't have a encryption policy? Lol.Reply
The Coca-Cola recipe is safe guarded to extremes and there are only 2 people in the world that know the entire recipe. When they are mobile they keep it locked in a bullet-proof, bomb-resistant metal briefcase that is locked to their arms and they fly private jets with military style security... they even fly seperate planes in case one goes down and yet NASA does not keep back up copies of some of the most important information and also has extremely low security standards? This is pathetic. Epic Fail NASA! -
razor512 government organizations are generally slow to adopt good security practices such as encrypting hard drives.Reply
As for the hacking, just make nasa open to the public, that way there will be no need to hack it to get any information. (if you pay taxes then you are paying nasa, you should have access to all of the info) -
ap3x Yea, this is a shame. They should at least have whole disk encryption on all mobile devices.Reply -
blazorthon Well guys, this is NASA, a government, military group. Yes, NASA is not civilian for anyone who didn't know. What do we expect from groups that are tied to the government and/or many companies, etc? They all seem to not care about hackers. If they cared then they would actually do something about it.Reply
That makes me wonder if any of these groups even have anything they care about enough to protect. Maybe they are just scape goats for stuff that the governments and military want to keep protected.1% mobile devices being encrypted? Lets see if those have anything relevant.

 Club Benefits
Club Benefits










