Protecting Your Privacy Online, Anonymously
While the Internet is not anonymous, with a little help you can make yourself less obvious and hidden from public view.
Vidalia (Tor/Privoxy)
Vidalia
While there are many different public open proxies on the Internet today, the Tor onion router network is specifically about providing users with a degree of privacy and anonymity. The Tor project claims that hundreds of thousand of people use the Tor network to provide privacy. Though Tor is popular, by itself it’s not quite as easy to take advantage of as it could be and that’s where Vidalia comes in.
Vidalia is a packaged application that includes Tor, the Privoxy local proxy as well as the Vidalia GUI for managing the Tor experience. With the one Vidalia download, you end up with a local Privoxy proxy loaded on your local PC with an instance of Tor to connect through for privacy.
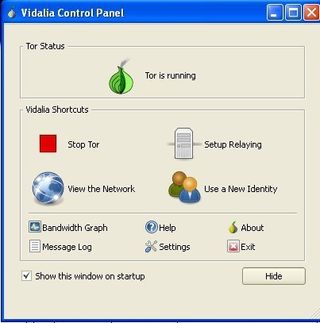
The Vidalia control panel
The Vidalia control panel shows you the status of your Tor connection, lets you start and stop it and provides an easy way to change proxies with the Use a New Identity button. Vidalia also offers a bandwidth graph so you can see exactly how much traffic you’ve sent through Tor. If you’re curious to see how big the Tor network is and how traffic flows, there is also an option to view the network
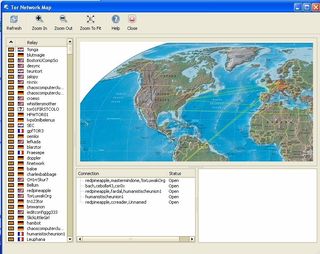
Vidalia : Tor Network Map showing connection activity
To get Vidalia to work with your Internet applications, there are a few different approaches. Since the Privoxy part of Vidalia is a local proxy, you can simply set any browser you may use to connect through the local proxy at the address and port what you specify in the Vidalia settings. For Mozilla Firefox users, taking advantage of Tor with Vidalia is even easier with a simple add-on called TorButton. With TorButton, there is a small indicator at the bottom of the browser display that you click on or off in order to activate an anonymous browsing experience.
Sign up to get the BEST of Tom's Guide direct to your inbox.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
While Vidalia makes Tor easy to use, there are still a few things the Vidalia control panel does not easily enable. For example, there is no easy way to specify or enable an SSL proxy. Also, there is no easy way to ensure that the proxy you select is in fact an anonymous proxy.
Using the free online ProxyJudge script at : http://www.proxyserverprivacy.com/adv-free-proxy-detector.shtml, we had proxies that were identified as anonymous as well as those that could be identified as being proxies—it all depended on which Tor server we were connected to.
The same issue goes for speed with Vidalia. While some Tor servers didn’t seem to impact our bandwidth by more than 25%, some servers were somewhat slower (several resulted in an 80% bandwidth or greater speed reduction).
Vidalia is, however, free and it is open source. You can also (if you’re so inclined) look at the source code and modify and/or extend it you need to.
Current page: Vidalia Tor-Privoxy Review - Internet Privacy Proxy - Tom’s Guide
Prev Page NetConceal Anonymity Security Shield Review - Proxy - Tom’s Guide Next Page MegaProxy Review - Online Anonymous Proxy Service - Tom’s Guide-
I found using a product like SafeSpace much better for protecting my privacy and it prevents malware infection too. Kinda two birds with one stone so to speak.Reply
-
Fbender You forgot to mention email privacy like Mailinator !!! (which I just used to sign up for this tom's acct (but had to use an alternate domain :) - you guys write about privacy but don't believe in allowing it?))Reply -
bberson I think this proxy stuff is over-rated and the concept of privacy is distorted. There are plenty of ways to toss your privacy out the window on the Internet and your IP address is at the very bottom of that list. And if you really need to hide your IP then (a) I can't help but wonder about the legality or propriety of what you're up to, (b) your first inquiry should be whether your anonymizing service is subpoena-proof. Many are not. The Tor network is interesting in this respect, since if nothing else it substantially complicates inquiry efforts.Reply
Let's separate fact from fiction and potential from practice...
Is your IP anonymous? Mostly, unless you have your own assigned address space (I do) or you're doing your surfing from a business or enterprise that has its own assigned address space. Finding out who is behind an ISP's dynamically assigned IP takes a letter from an attorney. Hardly an automated process.
Can your IP address reveal your geographic location? Yes, but only roughly. It will not reveal your address. At best it will reveal your town and in some cases, even that may be somewhat inaccurate depending on how your service is provisioned.
On the other hand if you fake your IP, any web site that uses geolocation services to target advertising, will offer you ads that are irrelevant. I'm on the fence with this. Which is worse? Relevant ads or irrelevant ads? Those of us who are experienced pretty much ignore all ads anyway.
Can your IP address be used to track you? Absolutely not. I can walk out the door right now and although I'll have to stop typing, I can guarantee you that nothing about my IP address will have given away the fact that I went to get a bottle of Coca-Cola from across the street.
Can your IP address be used to track your activities? Yes, to a limited extent, but due to the prevalence of dynamic IP addressing and the number of proxy -based systems (frequently used more for security in large companies than for privacy), generally nobody bothers. Cookies are a more reliable way to associate a person (or at least a computer) with their browsing habits. But for that to happen successfully some cooperation is required among the sites that place those cookies on your computer. Don't even get me started about cookies - another overblown source of panic.
SSL proxy connections. All very well and good for keeping prying eyes out of your local data stream but useless once the data leaves the proxy and finds its way to the web server. So at least it'll keep your ISP and your neighbor's young hacker kid off your bits 'n bytes.
Some of the other options really slay me. Why block info about your OS and your browser version? Seriously! And why strip HTTP Referer header info? A lot of this is used to help improve the web browsing experience for a viewer and in the case of referers, helps protect the site from abuse.
There are some other interesting purposes for web proxies that aren't directly related to privacy, such as circumventing ridiculous limitations on certain web services. It might help with the quality of your search results during your stay in China, or help facilitate access to P2P applications that are blocked from USA IP addresses, or help travelers gain access to USA web services that block or offer reduced functionality to offshore IP addresses.
A final note is that web browsing these days often involves a lot of extra plug-ins, multimedia widgets, peer to peer gadgets and so on. Not all of these blindly play along with proxy settings or proxy stacks. Some will do their own thing and some simply won't work at all. You'll have no idea if one of those pieces are dancing to their own beat until you run packet capturing software - a job not well-suited to those without propellor beanies. Those of us with the beanies know better than to care. -
Man, there are so many things wrong with the comment above..too lazy to list them personally. But he's obviously not up with current times on what you can do with an ip address.Reply
-
scout123 IP Check makes anonymouse.org & Co look really nakedReply
The privacy test IP Check uncovers that web proxy providers like Anonymouse.org can indeed not provide any privacy protection. Any arbitrary website is able to circumvent web proxies and to uncover the user's IP address and browser data, which should be actually protected by the proxy.
The respective security leaks are supposed to be present since up to 10 years in the code of these services. The question arised, whether anybody had seriously checked them for attacks before... You may find a demo of the numerous possible attacks here:
http://anonymouse.org/cgi-bin/anon-www.cgi/http://ip-check.info/?lang=en
In the following, you moreover find a detailed description of the tests:
http://ip-check.info/description.php#WebProxyDeanonymization
You find the main page of the IP Check itself here:
http://ip-check.info?lang=en
The question is: are web proxy providers intentionally deceiving their users regarding the security of their systems? Or do they simply lack the necessary competence in the area of IT security? Is it all about making money, or also about collecting detailed data about the users? In any case, it should be clear that the currently available web proxies are at the best suitable for the circumvention of Internet censorship, but in neither case for anonymous surfing.
It is possible that the IP check wil be blocked by some web proxy providers because of this demonstration. This would not be astonishing, as there is even in theory no protection against some of the used leaks. Whoever wants to make himself convinced should therefore do it now, before censorship will take place. However, you might realize any censorship of the Ip check as a confession that the web proxy providers are helpless against the attacks that are shown. -
In a very short answer to Mr. I question the legality of what you're doing: stalkers. It's not what I'm doing, it's what I'm trying to avoid being done to me. I can move around, or I can move my IP around. Can someone tell I've stepped out for a Coke? No. Can someone sit on a corner, in the general area of the IP, waiting for the day I come by? Sounds stupid, yes? Ask law enforcement tasked with picking up the pieces when the stalker finds the stalked, even after very elaborate steps have been taken to protect the stalked. Stalkers are obsessed, and tracking an IP is only one of their tools. I choose not to give it to them.Reply
