Routers
Latest about Routers

Asus TUF Gaming BE6500 router review: dual-band Wi-Fi 7 with top-flight wired performance
By Brian Nadel published
The Asus TUF Gaming BE6500 offers many of Wi-Fi 7’s best features on a shoestring budget but its excellent wired performance makes it a great choice for gamers.
Acer Predator Connect T7 review: the Wi-Fi 7-powered gaming mesh router to beat
By Brian Nadel published
The Acer Predator Connect T7 combines Wi-Fi 7 speeds with whole home mesh coverage in a sleek, yet subtle package for a gaming router.

Asus RP-AX58 review
By Brian Nadel published
The Asus RP-AX58 delivers excellent speeds for the price minus a few creature comforts

ExpressVPN Aircove review
By Brian Nadel published
Who needs an app when this small, Wi-Fi 6-powered, VPN router can secure up to five devices at once?
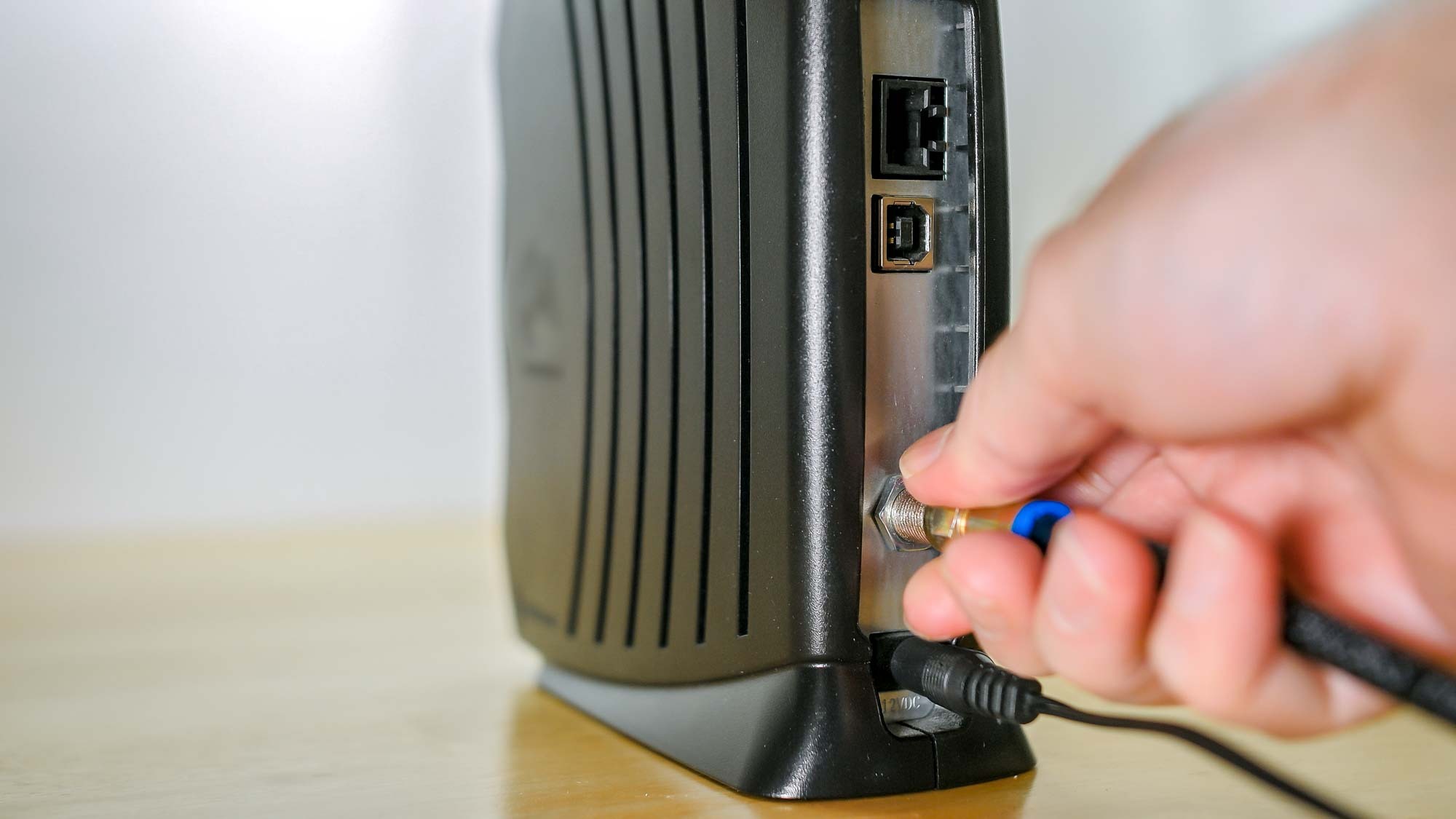
Best cable modems in 2025: Say goodbye to equipment rental fees for good
By Anthony Spadafora last updated
These are the best cable modems for your home or office so that you don't need to waste money each month renting one from your ISP.

Best Wi-Fi routers for 2025: Tested and rated
By Anthony Spadafora last updated
The best Wi-Fi routers span from older Wi-Fi 6 devices to newer Wi-Fi 6E and Wi-Fi 7 routers with blazing fast speeds.

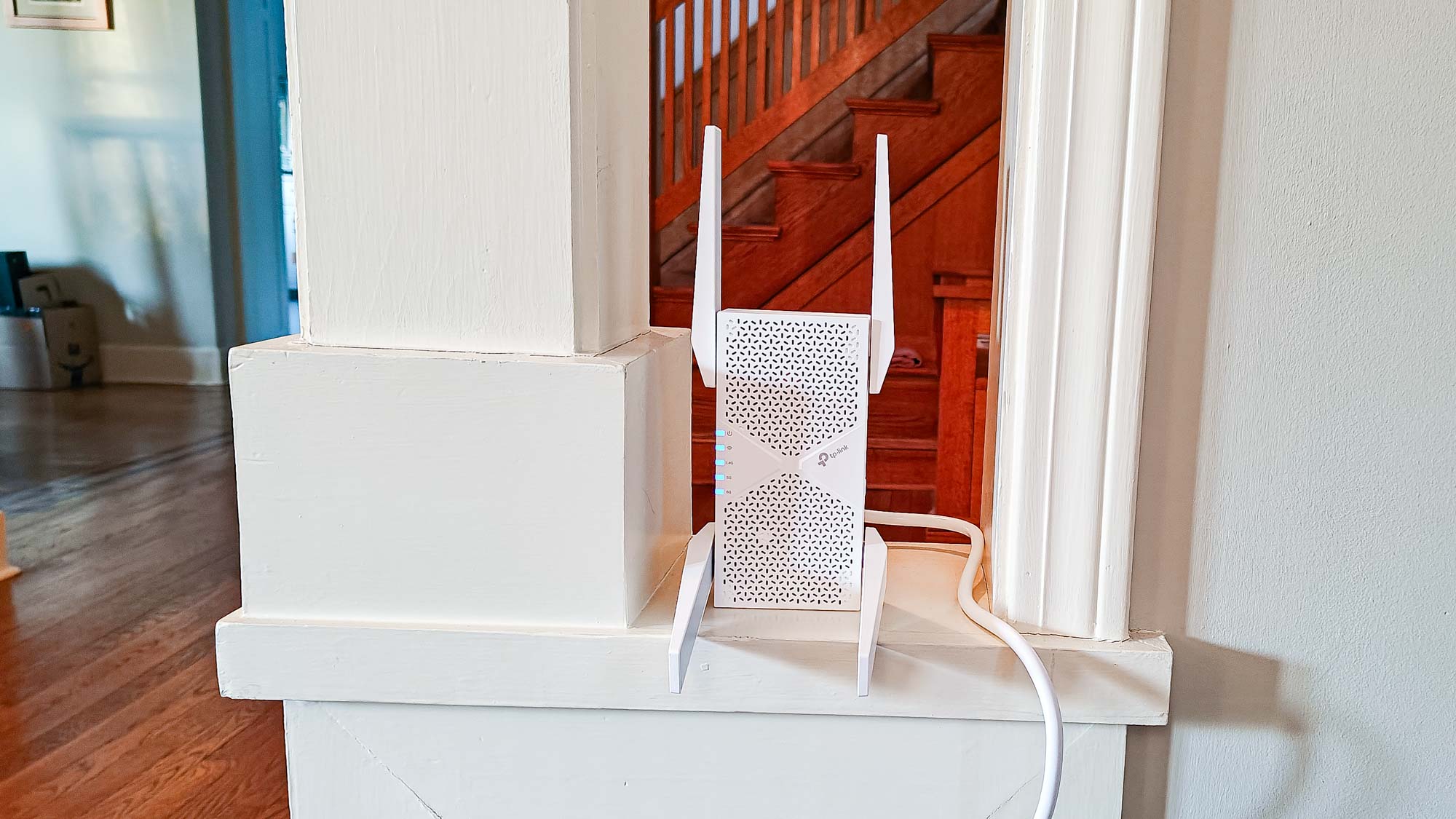
Linksys RE7350 review: a simple yet slow, app-free Wi-Fi extender
By Brian Nadel published
The Linksys RE7350 can help you eliminate Wi-Fi dead zones but its slow speeds and lack of an app to configure and control this Wi-Fi extender leave a lot to be desired.

Netgear EAX17 review: a Wi-Fi 6 extender that’s economical to use
By Brian Nadel published
The Netgear EAX17 provides good mid-range speeds and isn’t expensive to leave on at all times but its three-prong plug and slower Wi-Fi 6 rating might not make it the best fit for many home networks.
Here at Tom’s Guide our expert editors are committed to bringing you the best news, reviews and guides to help you stay informed and ahead of the curve!